Perguntas Frequentes

Início Rápido
Para começar com o Forward Email:
-
Crie uma conta em forwardemail.net/register
-
Adicione e verifique seu domínio em Minha Conta → Domínios
-
Adicione e configure aliases/caixas de email em Minha Conta → Domínios → Aliases
-
Teste sua configuração enviando um email para um dos seus novos aliases
Tip
Alterações no DNS podem levar até 24-48 horas para se propagar globalmente, embora frequentemente entrem em vigor muito antes.
Introdução
O que é o Forward Email
Note
O Forward Email é perfeito para indivíduos, pequenas empresas e desenvolvedores que desejam endereços de email profissionais sem o custo e a manutenção de uma solução completa de hospedagem de email.
O Forward Email é um provedor de serviço de email completo e provedor de hospedagem de email para nomes de domínio personalizados.
É o único serviço gratuito e de código aberto, que permite usar endereços de email com domínio personalizado sem a complexidade de configurar e manter seu próprio servidor de email.
Nosso serviço encaminha emails enviados para seu domínio personalizado para sua conta de email existente – e você pode até nos usar como seu provedor dedicado de hospedagem de email.
Principais recursos do Forward Email:
- Email com Domínio Personalizado: Use endereços de email profissionais com seu próprio nome de domínio
- Plano Gratuito: Encaminhamento básico de email sem custo
- Privacidade Aprimorada: Não lemos seus emails nem vendemos seus dados
- Código Aberto: Todo nosso código está disponível no GitHub
- Suporte SMTP, IMAP e POP3: Capacidades completas de envio e recebimento de email
- Criptografia de Ponta a Ponta: Suporte para OpenPGP/MIME
- Aliases Catch-All Personalizados: Crie aliases de email ilimitados
Você pode nos comparar com mais de 56 outros provedores de serviço de email em nossa página de Comparação de Email.
Tip
Saiba mais sobre o Forward Email lendo nosso Whitepaper Técnico gratuito e revisando nossa auditoria de segurança pela Cure53.
Quem usa o Forward Email
Fornecemos serviço de hospedagem e encaminhamento de email para mais de 500.000 domínios e estes usuários notáveis:
| Cliente | Estudo de Caso |
|---|---|
| Academia Naval dos EUA | 📄 Estudo de Caso |
| Canonical | 📄 Estudo de Caso |
| Netflix Games | |
| The Linux Foundation | 📄 Estudo de Caso |
| The PHP Foundation | |
| Fox News Radio | |
| Disney Ad Sales | |
| jQuery | 📄 Estudo de Caso |
| LineageOS | |
| Ubuntu | 📄 Estudo de Caso |
| Kubuntu | 📄 Estudo de Caso |
| Lubuntu | 📄 Estudo de Caso |
| Universidade de Cambridge | 📄 Estudo de Caso |
| Universidade de Maryland | 📄 Estudo de Caso |
| Universidade de Washington | 📄 Estudo de Caso |
| Universidade Tufts | 📄 Estudo de Caso |
| Swarthmore College | 📄 Estudo de Caso |
| Governo da Austrália do Sul | |
| Governo da República Dominicana | |
| Fly.io | |
| RCD Hotels | |
| Isaac Z. Schlueter (npm) | 📄 Estudo de Caso |
| David Heinemeier Hansson (Ruby on Rails) |
Qual é a história do Forward Email
Você pode saber mais sobre o Forward Email na nossa página Sobre.
Quão rápido é este serviço
Note
Nosso sistema é projetado para velocidade e confiabilidade, com múltiplos servidores redundantes para garantir que seus e-mails sejam entregues prontamente.
O Forward Email entrega mensagens com atraso mínimo, tipicamente em segundos após o recebimento.
Métricas de desempenho:
- Tempo Médio de Entrega: Menos de 5-10 segundos do recebimento ao encaminhamento (veja nossa página de monitoramento Tempo para Caixa de Entrada "TTI")
- Disponibilidade: 99,9%+ de disponibilidade do serviço
- Infraestrutura Global: Servidores estrategicamente localizados para roteamento ideal
- Escalonamento Automático: Nosso sistema escala durante períodos de pico de e-mails
Operamos em tempo real, diferente de outros provedores que dependem de filas atrasadas.
Não gravamos em disco nem armazenamos logs – com exceção de erros e SMTP de saída (veja nossa Política de Privacidade).
Tudo é feito em memória e nosso código-fonte está no GitHub.
Clientes de Email
Thunderbird
- Crie um novo alias e gere uma senha no seu painel do Forward Email
- Abra o Thunderbird e vá em Editar → Configurações de Conta → Ações da Conta → Adicionar Conta de Email
- Insira seu nome, endereço Forward Email e senha
- Clique em Configurar manualmente e insira:
- Entrada: IMAP,
imap.forwardemail.net, porta 993, SSL/TLS - Saída: SMTP,
smtp.forwardemail.net, porta 465, SSL/TLS (recomendado; porta 587 com STARTTLS também é suportada)
- Entrada: IMAP,
- Clique em Concluído
Microsoft Outlook
- Crie um novo alias e gere uma senha no seu painel do Forward Email
- Vá em Arquivo → Adicionar Conta
- Insira seu endereço Forward Email e clique em Conectar
- Escolha Opções avançadas e selecione Deixe-me configurar minha conta manualmente
- Selecione IMAP e insira:
- Entrada:
imap.forwardemail.net, porta 993, SSL - Saída:
smtp.forwardemail.net, porta 465, SSL/TLS (recomendado; porta 587 com STARTTLS também é suportada) - Nome de usuário: Seu endereço de e-mail completo
- Senha: Sua senha gerada
- Entrada:
- Clique em Conectar
Apple Mail
- Crie um novo alias e gere uma senha no seu painel do Forward Email
- Vá em Mail → Preferências → Contas → +
- Selecione Outra Conta de Email
- Insira seu nome, endereço Forward Email e senha
- Para configurações do servidor, insira:
- Entrada:
imap.forwardemail.net - Saída:
smtp.forwardemail.net - Nome de usuário: Seu endereço de e-mail completo
- Senha: Sua senha gerada
- Entrada:
- Clique em Entrar
eM Client
- Crie um novo alias e gere uma senha no seu painel do Forward Email
- Abra o eM Client e vá em Menu → Contas → + Adicionar Conta
- Clique em Email e depois selecione Outro
- Insira seu endereço Forward Email e clique em Próximo
- Insira as seguintes configurações de servidor:
- Servidor de entrada:
imap.forwardemail.net - Servidor de saída:
smtp.forwardemail.net
- Servidor de entrada:
- Insira seu endereço de e-mail completo como Nome de usuário e sua senha gerada como Senha para ambos os servidores de entrada e saída.
- O eM Client testará a conexão. Quando passar, clique em Próximo.
- Insira seu nome e escolha um nome para a conta.
- Clique em Concluir.
Dispositivos Móveis
Para iOS:
- Vá em Ajustes → Mail → Contas → Adicionar Conta → Outra
- Toque em Adicionar Conta de Email e insira seus dados
- Para configurações do servidor, use as mesmas configurações IMAP e SMTP acima
Para Android:
- Vá em Configurações → Contas → Adicionar Conta → Pessoal (IMAP)
- Insira seu endereço Forward Email e senha
- Para configurações do servidor, use as mesmas configurações IMAP e SMTP acima
Configuração de Relay SMTP Sendmail
Você pode configurar o Sendmail para retransmitir e-mails através dos servidores SMTP do Forward Email. Esta é uma configuração comum para sistemas legados ou aplicações que dependem do Sendmail.
Configuração
-
Edite seu arquivo
sendmail.mc, normalmente localizado em/etc/mail/sendmail.mc:sudo nano /etc/mail/sendmail.mc -
Adicione as seguintes linhas para definir o smart host e a autenticação:
define(`SMART_HOST', `smtp.forwardemail.net')dnl define(`RELAY_MAILER_ARGS', `TCP $h 465')dnl define(`confAUTH_MECHANISMS', `EXTERNAL GSSAPI DIGEST-MD5 CRAM-MD5 LOGIN PLAIN')dnl FEATURE(`authinfo',`hash -o /etc/mail/authinfo.db')dnl -
Crie o arquivo de autenticação
/etc/mail/authinfo:sudo nano /etc/mail/authinfo -
Adicione suas credenciais do Forward Email no arquivo
authinfo:AuthInfo:smtp.forwardemail.net "U:your-alias@yourdomain.com" "P:your-generated-password" "M:PLAIN" -
Gere o banco de dados de autenticação e proteja os arquivos:
sudo makemap hash /etc/mail/authinfo < /etc/mail/authinfo sudo chmod 600 /etc/mail/authinfo /etc/mail/authinfo.db -
Reconstrua a configuração do Sendmail e reinicie o serviço:
sudo make -C /etc/mail sudo systemctl restart sendmail
Testando
Envie um email de teste para verificar a configuração:
echo "Test email from Sendmail" | mail -s "Sendmail Test" recipient@example.com
Configuração do Relay SMTP Exim4
Exim4 é um MTA popular em sistemas baseados em Debian. Você pode configurá-lo para usar o Forward Email como smarthost.
Configuração
-
Execute a ferramenta de configuração do Exim4:
sudo dpkg-reconfigure exim4-config -
Selecione as seguintes opções:
- Tipo geral de configuração de email: email enviado por smarthost; recebido via SMTP ou fetchmail
- Nome do sistema de email: your.hostname
- Endereços IP para escutar conexões SMTP de entrada: 127.0.0.1 ; ::1
- Outros destinos para os quais o email é aceito: (deixe em branco)
- Domínios para retransmitir email: (deixe em branco)
- Endereço IP ou nome do host do smarthost de saída: smtp.forwardemail.net::465
- Ocultar nome local do email no email de saída? Não
- Manter o número de consultas DNS mínimo (Dial-on-Demand)? Não
- Método de entrega para email local: formato Mbox em /var/mail/
- Dividir configuração em arquivos pequenos? Não
-
Edite o arquivo
passwd.clientpara adicionar suas credenciais:sudo nano /etc/exim4/passwd.client -
Adicione a seguinte linha:
smtp.forwardemail.net:your-alias@yourdomain.com:your-generated-password -
Atualize a configuração e reinicie o Exim4:
sudo update-exim4.conf sudo systemctl restart exim4
Testando
Envie um email de teste:
echo "Test from Exim4" | mail -s "Exim4 Test" recipient@example.com
Configuração do Cliente SMTP msmtp
msmtp é um cliente SMTP leve que é útil para enviar emails a partir de scripts ou aplicações de linha de comando.
Configuração
-
Crie ou edite o arquivo de configuração do msmtp em
~/.msmtprc:nano ~/.msmtprc -
Adicione a seguinte configuração:
defaults auth on tls on tls_trust_file /etc/ssl/certs/ca-certificates.crt logfile ~/.msmtp.log account forwardemail host smtp.forwardemail.net port 465 tls_starttls off from seu-apelido@seudominio.com user seu-apelido@seudominio.com password sua-senha-gerada account default : forwardemail -
Defina as permissões corretas para o arquivo de configuração:
chmod 600 ~/.msmtprc
Testando
Envie um email de teste:
echo "Este é um email de teste do msmtp" | msmtp -a default recipient@example.com
Clientes de Email via Linha de Comando
Clientes de email populares via linha de comando como Mutt, NeoMutt, e Alpine podem ser configurados para usar os servidores SMTP do Forward Email para envio de emails. A configuração será semelhante à do msmtp, onde você fornece os detalhes do servidor SMTP e suas credenciais nos respectivos arquivos de configuração (.muttrc, .neomuttrc ou .pinerc).
Configuração de Email no Windows
Para usuários Windows, você pode configurar clientes de email populares como Microsoft Outlook e eM Client usando as configurações IMAP e SMTP fornecidas na sua conta Forward Email. Para uso via linha de comando ou scripts, você pode usar o cmdlet Send-MailMessage do PowerShell (embora seja considerado obsoleto) ou uma ferramenta leve de relay SMTP como E-MailRelay.
Configuração de Relay SMTP no Postfix
Você pode configurar o Postfix para encaminhar emails através dos servidores SMTP do Forward Email. Isso é útil para aplicações de servidor que precisam enviar emails.
Instalação
- Instale o Postfix no seu servidor:
# Ubuntu/Debian
sudo apt update && sudo apt install postfix
# CentOS/RHEL
sudo yum install postfix
# macOS
brew install postfix
- Durante a instalação, selecione "Internet Site" quando solicitado o tipo de configuração.
Configuração
- Edite o arquivo principal de configuração do Postfix:
sudo nano /etc/postfix/main.cf
- Adicione ou modifique estas configurações:
# Configuração do relay SMTP
relayhost = [smtp.forwardemail.net]:465
smtp_tls_wrappermode = yes
smtp_tls_security_level = encrypt
smtp_sasl_auth_enable = yes
smtp_sasl_password_maps = hash:/etc/postfix/sasl_passwd
smtp_sasl_security_options = noanonymous
smtp_tls_CAfile = /etc/ssl/certs/ca-certificates.crt
- Crie o arquivo de senha SASL:
sudo nano /etc/postfix/sasl_passwd
- Adicione suas credenciais do Forward Email:
[smtp.forwardemail.net]:465 seu-apelido@seudominio.com:sua-senha-gerada
- Proteja e gere o hash do arquivo de senha:
sudo chmod 600 /etc/postfix/sasl_passwd
sudo postmap /etc/postfix/sasl_passwd
- Reinicie o Postfix:
sudo systemctl restart postfix
Testando
Teste sua configuração enviando um email de teste:
echo "Corpo do email de teste" | mail -s "Assunto do Teste" recipient@example.com
Como Enviar Email Como usando Gmail
-
Vá para Minha Conta Domínios Configurações Configuração SMTP de Saída e siga as instruções de configuração
-
Crie um novo alias para seu domínio em Minha Conta Domínios Aliases (ex.
hello@example.com) -
Clique em Gerar Senha ao lado do alias recém-criado. Copie para sua área de transferência e armazene com segurança a senha gerada exibida na tela.
-
Vá para Gmail e em Configurações Contas e Importação Enviar e-mail como, clique em "Adicionar outro endereço de e-mail"
-
Quando solicitado o "Nome", insira o nome que você deseja que seu e-mail apareça como "De" (ex. "Linus Torvalds").
-
Quando solicitado o "Endereço de e-mail", insira o endereço de e-mail completo de um alias que você criou em Minha Conta Domínios Aliases (ex.
hello@example.com) -
Desmarque "Tratar como um alias"
-
Clique em "Próxima etapa" para continuar
-
Quando solicitado o "Servidor SMTP", insira
smtp.forwardemail.nete altere a porta para465 -
Quando solicitado o "Nome de usuário", insira o endereço de e-mail completo de um alias que você criou em Minha Conta Domínios Aliases (ex.
hello@example.com) -
Quando solicitado a "Senha", cole a senha do Gerar Senha no passo 3 acima
-
Selecione o botão de opção para "Conexão segura usando SSL"
-
Clique em "Adicionar Conta" para continuar
-
Abra uma nova aba em Gmail e aguarde o e-mail de verificação chegar (você receberá um código de verificação que confirma que você é o proprietário do endereço de e-mail que está tentando "Enviar e-mail como")
-
Quando chegar, copie e cole o código de verificação no prompt que você recebeu no passo anterior
-
Depois de fazer isso, volte ao e-mail e clique no link para "confirmar a solicitação". Você provavelmente precisará fazer esta etapa e a etapa anterior para que o e-mail seja configurado corretamente.
O que é o guia legado gratuito para Enviar Email Como usando Gmail
-
Você precisa ter a Autenticação de Dois Fatores do Gmail ativada para que isso funcione. Visite https://www.google.com/landing/2step/ se ainda não a tiver ativado.
-
Depois que a Autenticação de Dois Fatores estiver ativada (ou se você já a tinha ativada), visite https://myaccount.google.com/apppasswords.
-
Quando solicitado para "Selecione o app e o dispositivo para o qual deseja gerar a senha do app":
- Selecione "Mail" no menu suspenso "Selecionar app"
- Selecione "Outro" no menu suspenso "Selecionar dispositivo"
- Quando solicitado para inserir texto, digite o endereço de e-mail do seu domínio personalizado do qual você está encaminhando (ex.:
hello@example.com- isso ajudará você a acompanhar caso use este serviço para várias contas)
-
Copie a senha para sua área de transferência que é gerada automaticamente
Importante: Se você estiver usando o G Suite, acesse seu painel de administrador Apps G Suite Configurações do Gmail Configurações e certifique-se de marcar "Permitir que usuários enviem e-mails por meio de um servidor SMTP externo...". Haverá um atraso para que essa alteração seja ativada, então aguarde alguns minutos. -
Vá para Gmail e em Configurações Contas e Importação Enviar e-mail como, clique em "Adicionar outro endereço de e-mail"
-
Quando solicitado para "Nome", insira o nome que você quer que seu e-mail apareça como remetente (ex.: "Linus Torvalds")
-
Quando solicitado para "Endereço de e-mail", insira o endereço de e-mail com o domínio personalizado que você usou acima (ex.:
hello@example.com) -
Desmarque "Tratar como um alias"
-
Clique em "Próximo Passo" para continuar
-
Quando solicitado por "Servidor SMTP", insira
smtp.gmail.come deixe a porta como587 -
Quando solicitado por "Nome de usuário", insira a parte do seu endereço Gmail sem a parte gmail.com (por exemplo, apenas "user" se meu email for user@gmail.com)
Importante: Se a parte "Nome de usuário" for preenchida automaticamente, então você precisará alterar isso para a parte do nome de usuário do seu endereço Gmail. -
Quando solicitado por "Senha", cole da sua área de transferência a senha que você gerou no passo 2 acima
-
Deixe o botão de opção marcado para "Conexão segura usando TLS"
-
Clique em "Adicionar Conta" para continuar
-
Abra uma nova aba em Gmail e aguarde o email de verificação chegar (você receberá um código de verificação que confirma que você é o proprietário do endereço de email que está tentando "Enviar Email Como")
-
Quando chegar, copie e cole o código de verificação no prompt que você recebeu no passo anterior
-
Depois de fazer isso, volte ao email e clique no link para "confirmar a solicitação". Você provavelmente precisará fazer este passo e o anterior para que o email seja configurado corretamente.
Configuração Avançada de Roteamento do Gmail
Se você quiser configurar roteamento avançado no Gmail para que aliases que não correspondam a uma caixa de correio sejam encaminhados para os servidores de email do Forward Email, siga estes passos:
- Faça login no seu console do Google Admin em admin.google.com
- Vá para Apps → Google Workspace → Gmail → Roteamento
- Clique em Adicionar Rota e configure as seguintes opções:
Configurações de Destinatário Único:
- Selecione "Alterar destinatário do envelope" e insira seu endereço Gmail principal
- Marque "Adicionar cabeçalho X-Gm-Original-To com destinatário original"
Padrões de Destinatário do Envelope:
- Adicione um padrão que corresponda a todas as caixas de correio inexistentes (por exemplo,
.*@seudominio.com)
Configurações do Servidor de Email:
- Selecione "Roteamento para host" e insira
mx1.forwardemail.netcomo servidor principal - Adicione
mx2.forwardemail.netcomo servidor de backup - Defina a porta para 25
- Selecione "Exigir TLS" para segurança
- Clique em Salvar para criar a rota
Configuração Avançada de Roteamento do Outlook
Para usuários do Microsoft 365 (antigo Office 365) que desejam configurar roteamento avançado para que aliases que não correspondam a uma caixa de correio sejam encaminhados para os servidores de email do Forward Email:
- Faça login no centro de administração do Microsoft 365 em admin.microsoft.com
- Vá para Exchange → Fluxo de email → Regras
- Clique em Adicionar uma regra e selecione Criar uma nova regra
- Nomeie sua regra (por exemplo, "Encaminhar caixas inexistentes para Forward Email")
- Em Aplicar esta regra se, selecione:
- "O endereço do destinatário corresponder a..."
- Insira um padrão que corresponda a todos os endereços do seu domínio (por exemplo,
*@seudominio.com)
- Em Fazer o seguinte, selecione:
- "Redirecionar a mensagem para..."
- Escolha "O seguinte servidor de email"
- Insira
mx1.forwardemail.nete porta 25 - Adicione
mx2.forwardemail.netcomo servidor de backup
- Em Exceto se, selecione:
- "O destinatário for..."
- Adicione todas as suas caixas de correio existentes que não devem ser encaminhadas
- Defina a prioridade da regra para garantir que ela seja executada após outras regras de fluxo de email
- Clique em Salvar para ativar a regra
Solução de Problemas
Por que não estou recebendo meus e-mails de teste
Se você está enviando um e-mail de teste para si mesmo, ele pode não aparecer na sua caixa de entrada porque possui o mesmo cabeçalho "Message-ID".
Este é um problema amplamente conhecido, que também afeta serviços como o Gmail. Aqui está a resposta oficial do Gmail sobre esse problema.
Se você continuar tendo problemas, provavelmente é uma questão de propagação de DNS. Você precisará esperar um pouco mais e tentar novamente (ou tentar definir um valor TTL mais baixo nos seus registros TXT).
Ainda está tendo problemas? Por favor, entre em contato conosco para que possamos ajudar a investigar o problema e encontrar uma solução rápida.
Como configurar meu cliente de e-mail para funcionar com o Forward Email
| Tipo | Nome do Host | Protocolo | Portas |
|---|---|---|---|
| IMAP | imap.forwardemail.net |
SSL/TLS Preferido | 993 e 2993 |
| SMTP | smtp.forwardemail.net |
SSL/TLS Recomendado | 465 e 2465 para SSL/TLS (recomendado) ou 587, 2587, 2525 e 25 para STARTTLS |
Por que meus e-mails estão caindo na Lixeira e Spam e como posso verificar a reputação do meu domínio
Esta seção orienta você caso seu e-mail de saída esteja usando nossos servidores SMTP (por exemplo, smtp.forwardemail.net) (ou encaminhado via mx1.forwardemail.net ou mx2.forwardemail.net) e esteja sendo entregue na pasta de Spam ou Lixo Eletrônico dos destinatários.
Monitoramos rotineiramente nossos endereços IP contra todas as listas de bloqueio DNS reputadas, portanto, é muito provável que seja um problema específico de reputação do domínio.
E-mails podem cair em pastas de spam por várias razões:
-
Autenticação Ausente: Configure os registros SPF, DKIM e DMARC.
-
Reputação do Domínio: Domínios novos geralmente têm reputação neutra até estabelecerem um histórico de envio.
-
Gatilhos de Conteúdo: Certas palavras ou frases podem ativar filtros de spam.
-
Padrões de Envio: Aumentos súbitos no volume de e-mails podem parecer suspeitos.
Você pode tentar usar uma ou mais destas ferramentas para verificar a reputação e categorização do seu domínio:
Ferramentas de Verificação de Reputação e Listas de Bloqueio
| Nome da Ferramenta | URL | Tipo |
|---|---|---|
| Feedback de Categorização de Domínio Cloudflare | https://radar.cloudflare.com/domains/feedback | Categorização |
| Verificador de Reputação de IP e Domínio Spamhaus | https://check.spamhaus.org/ | DNSBL |
| Centro de Reputação de IP e Domínio Cisco Talos | https://talosintelligence.com/reputation_center | Reputação |
| Consulta de Reputação de IP e Domínio Barracuda | https://www.barracudacentral.org/lookups/lookup-reputation | DNSBL |
| Verificação de Lista Negra MX Toolbox | https://mxtoolbox.com/blacklists.aspx | Lista Negra |
| Ferramentas do Postmaster do Google | https://www.gmail.com/postmaster/ | Reputação |
| Hub de Remetentes do Yahoo | https://senders.yahooinc.com/ | Reputação |
| Verificação de Lista Negra MultiRBL.valli.org | https://multirbl.valli.org/lookup/ | DNSBL |
| Sender Score | https://senderscore.org/act/blocklist-remover/ | Reputação |
| Invaluement | https://www.invaluement.com/lookup/ | DNSBL |
| SURBL | https://www.surbl.org/ | DNSBL |
| SpamCop | https://www.spamcop.net/bl.shtml | DNSBL |
| Níveis 1, 2 e 3 do UCEPROTECT | https://www.uceprotect.net/en/rblcheck.php | DNSBL |
| backscatterer.org do UCEPROTECT | https://www.backscatterer.org/ | Proteção contra Backscatter |
| whitelisted.org do UCEPROTECT | https://www.whitelisted.org/ (requer taxa) | DNSWL |
Formulários de Solicitação de Remoção de IP por Provedor
Se seu endereço IP foi bloqueado por um provedor de e-mail específico, use o formulário de remoção apropriado ou contato abaixo:
| Provedor | Formulário de Remoção / Contato | Notas |
|---|---|---|
| Google/Gmail | https://support.google.com/mail/contact/bulk_send_new | Formulário de contato para remetentes em massa |
| Microsoft (Outlook/Office 365/Hotmail) | https://sender.office.com | Portal de delistagem de IP do Office 365 |
| Yahoo/AOL/Verizon | https://senders.yahooinc.com/ | Hub de Remetentes do Yahoo |
| Apple/iCloud | https://ipcheck.proofpoint.com/ | Apple usa Proofpoint para reputação de IP |
| Proofpoint | https://ipcheck.proofpoint.com/ | Verificação e remoção de IP no Proofpoint |
| Barracuda Networks | https://www.barracudacentral.org/lookups/lookup-reputation | Consulta e remoção de reputação Barracuda |
| Cloudmark | https://csi.cloudmark.com/en/reset/ | Solicitação de reset Cloudmark CSI |
| GoDaddy/SecureServer | https://unblock.secureserver.net | Formulário de desbloqueio de IP GoDaddy |
| Comcast/Xfinity | https://spa.xfinity.com/report | Solicitação de remoção de IP Comcast |
| Charter/Spectrum | https://www.spectrum.net/support/internet/understanding-email-error-codes | Contate o suporte Spectrum para remoção |
| AT&T | abuse_rbl@abuse-att.net |
E-mail para solicitação de remoção |
| Cox Communications | unblock.request@cox.net |
E-mail para solicitação de remoção |
| CenturyLink/Lumen | abuse@centurylink.com |
Usa Cloudfilter |
| Windstream | abuse@windstream.net |
E-mail para solicitação de remoção |
| t-online.de (Alemanha) | tobr@rx.t-online.de |
E-mail para solicitação de remoção |
| Orange France | https://postmaster.orange.fr/ | Use formulário de contato ou e-mail abuse@orange.fr |
| GMX | https://postmaster.gmx.net/en/contact | Formulário de contato do postmaster GMX |
| Mail.ru | https://postmaster.mail.ru/ | Portal do postmaster Mail.ru |
| Yandex | https://postmaster.yandex.ru/ | Portal do postmaster Yandex |
| QQ Mail (Tencent) | https://open.mail.qq.com/ | Aplicação para whitelist do QQ Mail (Chinês) |
| Netease (163.com) | https://mail.163.com/postmaster/ | Portal do postmaster Netease |
| Alibaba/Aliyun/HiChina | https://www.alibabacloud.com/help/en/alibaba-mail/ | Contato via console Alibaba Cloud |
| Amazon SES | https://docs.aws.amazon.com/ses/latest/dg/faqs-dnsbls.html | Console AWS SES > Remoção de Lista Negra |
| SendGrid | https://support.sendgrid.com/ | Contato com suporte SendGrid |
| Mimecast | https://community.mimecast.com/ | Usa RBLs de terceiros - contate RBL específico |
| Fastmail | https://www.fastmail.com/support/ | Contato com suporte Fastmail |
| Zoho | https://help.zoho.com/portal/en/kb/campaigns/faqs/campaign-review/articles/how-do-i-delist-my-ip-address | Contato com suporte Zoho |
| ProtonMail | https://proton.me/support/contact | Contato com suporte Proton |
| Tutanota | https://tutanota.com/support | Contato com suporte Tutanota |
| Hushmail | https://www.hushmail.com/support/ | Contato com suporte Hushmail |
| Mailbox.org | https://mailbox.org/en/support | Contato com suporte Mailbox.org |
| Posteo | https://posteo.de/en/site/contact | Contato com suporte Posteo |
| DuckDuckGo Email | https://duckduckgo.com/email/support | Contato com suporte DuckDuckGo |
| Sonic.net | https://www.sonic.com/support | Contato com suporte Sonic |
| Telus | https://www.telus.com/en/support | Contato com suporte Telus |
| Vodafone Germany | https://www.vodafone.de/hilfe/ | Contato com suporte Vodafone |
| Xtra (Spark NZ) | https://www.spark.co.nz/help/ | Contato com suporte Spark NZ |
| UOL/BOL (Brasil) | https://ajuda.uol.com.br/ | Contato com suporte UOL (Português) |
| Libero (Itália) | https://aiuto.libero.it/ | Contato com suporte Libero (Italiano) |
| Telenet (Bélgica) | https://www2.telenet.be/en/support/ | Contato com suporte Telenet |
| Facebook/WhatsApp | https://www.facebook.com/business/help | Contato com suporte comercial Facebook |
| https://www.linkedin.com/help/linkedin | Contato com suporte LinkedIn | |
| Groups.io | https://groups.io/helpcenter | Contato com suporte Groups.io |
| Earthlink/Vade Secure | https://sendertool.vadesecure.com/en/ | Ferramenta de remetente Vade Secure |
| Cloudflare Email Security | https://www.cloudflare.com/products/zero-trust/email-security/ | Contato com suporte Cloudflare |
| Hornetsecurity/Expurgate | https://www.hornetsecurity.com/ | Contato com suporte Hornetsecurity |
| SpamExperts/Antispamcloud | https://www.spamexperts.com/ | Contato via provedor de hospedagem |
| Mail2World | https://www.mail2world.com/support/ | Contato com suporte Mail2World |
Tip
Comece com um volume baixo de e-mails de alta qualidade para construir uma reputação positiva antes de enviar em volumes maiores.
Important
Se seu domínio estiver em uma lista negra, cada lista negra tem seu próprio processo de remoção. Verifique os sites deles para instruções.
Tip
Se precisar de ajuda adicional ou descobrir que estamos listados como falso-positivo como spam por algum provedor de serviço de e-mail, por favor contate-nos.
O que devo fazer se receber e-mails de spam
Você deve cancelar a inscrição da lista de e-mails (se possível) e bloquear o remetente.
Por favor, não reporte a mensagem como spam, mas encaminhe-a para nosso sistema manualmente curado e focado em privacidade para prevenção de abusos.
O endereço de e-mail para encaminhar spam é: abuse@forwardemail.net
Por que meus e-mails de teste enviados para mim mesmo no Gmail aparecem como "suspeitos"
Se você vir essa mensagem de erro no Gmail ao enviar um teste para si mesmo, ou quando uma pessoa com quem você está enviando e-mails com seu alias vê um e-mail seu pela primeira vez, então por favor, não se preocupe – pois isso é um recurso de segurança embutido do Gmail.
Você pode simplesmente clicar em "Parece seguro". Por exemplo, se você enviar uma mensagem de teste usando o recurso enviar e-mail como (para outra pessoa), então ela não verá essa mensagem.
No entanto, se ela vir essa mensagem, é porque normalmente estava acostumada a ver seus e-mails vindo de john@gmail.com em vez de john@customdomain.com (apenas um exemplo). O Gmail alerta os usuários apenas para garantir que tudo está seguro, não há solução alternativa.
Posso remover o via forwardemail dot net no Gmail
Este tópico está relacionado a um problema amplamente conhecido no Gmail onde informações extras aparecem ao lado do nome do remetente.
A partir de maio de 2023, oferecemos suporte ao envio de e-mails com SMTP como um complemento para todos os usuários pagos – o que significa que você pode remover o via forwardemail dot net no Gmail.
Note que este tópico de FAQ é específico para quem usa o recurso Como Enviar E-mail Como usando Gmail.
Por favor, veja a seção sobre Vocês suportam envio de e-mail com SMTP para instruções de configuração.
Gerenciamento de Dados
Onde estão localizados seus servidores
Tip
Em breve podemos anunciar nossa localização de datacenter na UE hospedada em forwardemail.eu. Inscreva-se na discussão em https://github.com/orgs/forwardemail/discussions/336 para atualizações.
Nossos servidores estão localizados principalmente em Denver, Colorado – veja https://forwardemail.net/ips para nossa lista completa de endereços IP.
Você pode conhecer nossos subprocessadores em nossas páginas GDPR, DPA e Privacidade.
Como exporto e faço backup da minha caixa de correio
A qualquer momento você pode exportar suas caixas de correio nos formatos EML, Mbox ou SQLite criptografados.
Vá para Minha Conta Domínios Aliases Baixar Backup e selecione seu tipo de formato de exportação preferido.
Você receberá um link para download da exportação por e-mail assim que ela for concluída.
Note que este link para download da exportação expira após 4 horas por questões de segurança.
Se precisar inspecionar seus formatos exportados EML ou Mbox, estas ferramentas open-source podem ser úteis:
| Nome | Formato | Plataforma | URL do GitHub |
|---|---|---|---|
| MBox Viewer | Mbox | Windows | https://github.com/eneam/mboxviewer |
| mbox-web-viewer | Mbox | Todas | https://github.com/PHMRanger/mbox-web-viewer |
| EmlReader | EML | Windows | https://github.com/ayamadori/EmlReader |
| Email viewer | EML | VSCode | https://github.com/joelharkes/vscode_email_viewer |
| eml-reader | EML | Todas | https://github.com/s0ph1e/eml-reader |
| Additionally if you need to convert a Mbox file to EML file, then you can use https://github.com/noelmartinon/mboxzilla. |
Como importar e migrar minha caixa de correio existente
Você pode facilmente importar seu e-mail para o Forward Email (por exemplo, usando o Thunderbird) com as instruções abaixo:
-
Exporte seu e-mail do seu provedor de e-mail atual:
Provedor de E-mail Formato de Exportação Instruções de Exportação Gmail MBOX https://takeout.google.com/settings/takeout/custom/gmail Outlook PST Dica: Se você usa Outlook (formato de exportação PST), então você pode simplesmente seguir as instruções em "Outros" abaixo. No entanto, fornecemos links abaixo para converter PST para formato MBOX/EML conforme seu sistema operacional:- Zinkuba para Windows (GitHub)
- readpst para Windows cygwin – (ex:
readpst -u -o $OUT_DIR $IN_DIRsubstituindo$OUT_DIRe$IN_DIRpelos caminhos do diretório de saída e entrada, respectivamente). - readpst para Ubuntu/Linux – (ex:
sudo apt-get install readpste depoisreadpst -u -o $OUT_DIR $IN_DIR, substituindo$OUT_DIRe$IN_DIRpelos caminhos do diretório de saída e entrada, respectivamente). - readpst para macOS (via brew) – (ex:
brew install libpste depoisreadpst -u -o $OUT_DIR $IN_DIR, substituindo$OUT_DIRe$IN_DIRpelos caminhos do diretório de saída e entrada, respectivamente). - Conversor PST para Windows (GitHub)
Apple Mail MBOX https://support.apple.com/guide/mail/import-or-export-mailboxes-mlhlp1030/mac#apd37a3190755974 Fastmail EML https://www.fastmail.help/hc/en-us/articles/360060590573-Download-all-your-data#downloadmail Proton Mail MBOX/EML https://proton.me/support/export-emails-import-export-app Tutanota EML https://github.com/crepererum-oss/tatutanatata Gandi EML https://docs.gandi.net/en/gandimail/common_operations/backup_email.html#contents Zoho EML https://www.zoho.com/mail/help/import-export-emails.html#alink2 Outros Use Thunderbird Configure sua conta de e-mail existente no Thunderbird e então use o plugin ImportExportTools NG para exportar e importar seu e-mail. Você também pode simplesmente copiar/colar ou arrastar/soltar e-mails entre uma conta e outra. -
Baixe, instale e abra o Thunderbird.
-
Crie uma nova conta usando o endereço de e-mail completo do seu alias (ex.:
you@yourdomain.com) e sua senha gerada. Se você ainda não possui uma senha gerada, então consulte nossas instruções de configuração. -
Baixe e instale o plugin ImportExportTools NG para Thunderbird.
-
Crie uma nova pasta local no Thunderbird, e então clique com o botão direito nela → selecione a opção
ImportExportTools NG→ escolhaImport mbox file(para formato de exportação MBOX) – ou –Import messages/Import all messages from a directory(para formato de exportação EML). -
Arraste e solte da pasta local para uma nova pasta IMAP (ou existente) no Thunderbird para a qual deseja enviar mensagens no armazenamento IMAP com nosso serviço. Isso garantirá que elas sejam salvas online com nosso armazenamento criptografado SQLite.
Dica: Se você estiver com dúvidas sobre como importar no Thunderbird, pode consultar as instruções oficiais em https://kb.mozillazine.org/Importing_folders e https://github.com/thunderbird/import-export-tools-ng/wiki.
Como uso meu próprio armazenamento compatível com S3 para backups
Usuários de planos pagos podem configurar seu próprio provedor de armazenamento compatível com S3 por domínio para backups IMAP/SQLite. Isso significa que seus backups criptografados da caixa de correio podem ser armazenados em sua própria infraestrutura em vez de (ou além de) nosso armazenamento padrão.
Os provedores suportados incluem Amazon S3, Cloudflare R2, MinIO, Backblaze B2, DigitalOcean Spaces e qualquer outro serviço compatível com S3.
Configuração
- Crie um bucket privado com seu provedor compatível com S3. O bucket não deve ser acessível publicamente.
- Crie credenciais de acesso (ID da chave de acesso e chave secreta de acesso) com permissões de leitura/gravação para o bucket.
- Vá para Minha Conta Domínios Configurações Avançadas Armazenamento Compatível com S3 Personalizado.
- Marque "Ativar armazenamento compatível com S3 personalizado" e preencha sua URL de endpoint, ID da chave de acesso, chave secreta de acesso, região e nome do bucket.
- Clique em "Testar Conexão" para verificar suas credenciais, acesso ao bucket e permissões de gravação.
- Clique em "Salvar" para aplicar as configurações.
Como os Backups Funcionam
Os backups são acionados automaticamente para cada alias IMAP conectado. O servidor IMAP verifica todas as conexões ativas uma vez por hora e dispara um backup para cada alias conectado. Um bloqueio baseado em Redis impede que backups duplicados sejam executados dentro de 30 minutos um do outro, e o backup real é pulado se um backup bem-sucedido já foi concluído nas últimas 24 horas (a menos que o backup tenha sido explicitamente solicitado por um usuário para download). Backups também podem ser acionados manualmente clicando em "Download Backup" para qualquer alias no painel. Backups manuais sempre são executados independentemente da janela de 24 horas.
O processo de backup funciona da seguinte forma:
- O banco de dados SQLite é copiado usando
VACUUM INTO, que cria um snapshot consistente sem interromper conexões ativas e preserva a criptografia do banco de dados. - O arquivo de backup é verificado abrindo-o para confirmar que a criptografia ainda é válida.
- Um hash SHA-256 é calculado e comparado com o backup existente no armazenamento. Se o hash coincidir, o upload é pulado (sem alterações desde o último backup).
- O backup é enviado para o S3 usando upload multipart via a biblioteca @aws-sdk/lib-storage.
- Uma URL de download assinada (válida por 4 horas) é gerada e enviada por e-mail ao usuário.
Backup Formats
Três formatos de backup são suportados:
| Formato | Extensão | Descrição |
|---|---|---|
sqlite |
.sqlite |
Snapshot bruto do banco de dados SQLite criptografado (padrão para backups IMAP automáticos) |
mbox |
.zip |
ZIP protegido por senha contendo a caixa de correio no formato mbox |
eml |
.zip |
ZIP protegido por senha contendo arquivos .eml individuais por mensagem |
Dica: Se você tem arquivos de backup
.sqlitee quer convertê-los para arquivos.emllocalmente, use nossa ferramenta CLI independente convert-sqlite-to-eml. Funciona no Windows, Linux e macOS e não requer conexão de rede.
File Naming and Key Structure
Ao usar armazenamento S3 personalizado, os arquivos de backup são armazenados com um prefixo de timestamp ISO 8601 para que cada backup seja preservado como um objeto separado. Isso fornece um histórico completo de backups no seu próprio bucket.
O formato da chave é:
{ISO 8601 timestamp}-{alias_id}.{extension}
Por exemplo:
2025-03-01T12:00:00.000Z-65a31c53c36b75ed685f3fda.sqlite
2025-03-01T12:00:00.000Z-65a31c53c36b75ed685f3fda.zip
2025-03-02T12:00:00.000Z-65a31c53c36b75ed685f3fda.sqlite
O alias_id é o ObjectId do MongoDB do alias. Você pode encontrá-lo na página de configurações do alias ou via API.
Ao usar o armazenamento padrão (do sistema), a chave é plana (ex.: 65a31c53c36b75ed685f3fda.sqlite) e cada backup sobrescreve o anterior.
Nota: Como o armazenamento S3 personalizado retém todas as versões de backup, o uso de armazenamento crescerá com o tempo. Recomendamos configurar regras de ciclo de vida no seu bucket para expirar automaticamente backups antigos (ex.: excluir objetos com mais de 30 ou 90 dias).
Data Ownership and Deletion Policy
Seu bucket S3 personalizado está totalmente sob seu controle. Nós nunca deletamos ou modificamos arquivos no seu bucket S3 personalizado — nem quando um alias é deletado, nem quando um domínio é removido, nem durante quaisquer operações de limpeza. Nós apenas escrevemos novos arquivos de backup no seu bucket.
Isso significa:
- Exclusão de alias — Quando você deleta um alias, removemos o backup apenas do nosso armazenamento padrão do sistema. Quaisquer backups previamente gravados no seu bucket S3 personalizado permanecem intactos.
- Remoção de domínio — Remover um domínio não afeta arquivos no seu bucket personalizado.
- Gerenciamento de retenção — Você é responsável por gerenciar o armazenamento no seu próprio bucket, incluindo configurar regras de ciclo de vida para expirar backups antigos.
Se você desativar o armazenamento S3 personalizado ou voltar para nosso armazenamento padrão, os arquivos existentes no seu bucket são preservados. Backups futuros simplesmente serão gravados no nosso armazenamento padrão.
Security
- Sua chave de acesso e chave secreta são criptografadas em repouso usando AES-256-GCM antes de serem armazenadas em nosso banco de dados. Elas são descriptografadas apenas em tempo de execução durante operações de backup.
- Validamos automaticamente que seu bucket não é publicamente acessível. Se um bucket público for detectado, a configuração será rejeitada ao salvar. Se o acesso público for detectado no momento do backup, voltamos ao nosso armazenamento padrão e notificamos todos os administradores do domínio por e-mail.
- As credenciais são validadas ao salvar via uma chamada HeadBucket para garantir que o bucket existe e as credenciais estão corretas. Se a validação falhar, o armazenamento S3 personalizado é desativado automaticamente.
- Cada arquivo de backup inclui um hash SHA-256 em seus metadados S3, que é usado para detectar bancos de dados inalterados e pular uploads redundantes.
Notificações de Erro
Se um backup falhar ao usar seu armazenamento S3 personalizado (por exemplo, devido a credenciais expiradas ou um problema de conectividade), todos os administradores do domínio serão notificados por e-mail. Essas notificações são limitadas a uma vez a cada 6 horas para evitar alertas duplicados. Se seu bucket for detectado como publicamente acessível no momento do backup, os administradores serão notificados uma vez por dia.
API
Você também pode configurar armazenamento S3 personalizado via API:
curl -X PUT https://api.forwardemail.net/v1/domains/example.com \
-u API_TOKEN: \
-d has_custom_s3=true \
-d s3_endpoint=https://s3.us-east-1.amazonaws.com \
-d s3_access_key_id=YOUR_ACCESS_KEY_ID \
-d s3_secret_access_key=YOUR_SECRET_ACCESS_KEY \
-d s3_region=us-east-1 \
-d s3_bucket=my-email-backups
Para testar a conexão via API:
curl -X POST https://api.forwardemail.net/v1/domains/example.com/test-s3-connection \
-u API_TOKEN:
Como converter backups SQLite para arquivos EML
Se você baixar ou armazenar backups SQLite (seja do nosso armazenamento padrão ou do seu próprio bucket S3 personalizado), pode convertê-los para arquivos .eml padrão usando nossa ferramenta CLI independente convert-sqlite-to-eml. Arquivos EML podem ser abertos com qualquer cliente de e-mail (Thunderbird, Outlook, Apple Mail, etc.) ou importados para outros servidores de e-mail.
Instalação
Você pode baixar um binário pré-compilado (não requer Node.js) ou executá-lo diretamente com Node.js:
Binários pré-compilados — Baixe a última versão para sua plataforma em GitHub Releases:
| Plataforma | Arquitetura | Arquivo |
|---|---|---|
| Linux | x64 | convert-sqlite-to-eml-linux-x64 |
| Linux | arm64 | convert-sqlite-to-eml-linux-arm64 |
| macOS | Apple Silicon | convert-sqlite-to-eml-darwin-arm64 |
| Windows | x64 | convert-sqlite-to-eml-win-x64.exe |
Usuários macOS: Após o download, pode ser necessário remover o atributo de quarentena antes de executar o binário:
sudo xattr -rd com.apple.quarantine ./convert-sqlite-to-eml-darwin-arm64(Substitua
./convert-sqlite-to-eml-darwin-arm64pelo caminho real do arquivo baixado.)
Usuários Linux: Após o download, pode ser necessário tornar o binário executável:
chmod +x ./convert-sqlite-to-eml-linux-x64(Substitua
./convert-sqlite-to-eml-linux-x64pelo caminho real do arquivo baixado.)
A partir do código-fonte (requer Node.js >= 18):
cd tools/convert-sqlite-to-eml
npm install
node index.js
Uso
A ferramenta suporta modos interativo e não interativo.
Modo interativo — execute sem argumentos e você será solicitado a fornecer todas as entradas:
./convert-sqlite-to-eml
Forward Email - Converter Backup SQLite para EML
================================================
Caminho para o arquivo de backup SQLite: /path/to/backup.sqlite
Senha IMAP/alias: ********
Caminho de saída do ZIP [/path/to/backup-2025-03-01T12-00-00-000Z.zip]:
Modo não interativo — passe argumentos via flags na linha de comando para scripts e automação:
./convert-sqlite-to-eml \
--path /path/to/backup.sqlite \
--password "sua-senha-imap" \
--output /path/to/output.zip
| Flag | Descrição |
|---|---|
--path <path> |
Caminho para o arquivo de backup SQLite criptografado |
--password <pass> |
Senha IMAP/alias para descriptografia |
--output <path> |
Caminho de saída para o arquivo ZIP (padrão: gerado automaticamente com timestamp ISO 8601) |
--help |
Exibe mensagem de ajuda |
Formato de Saída
A ferramenta produz um arquivo ZIP protegido por senha (criptografado com AES-256) contendo:
README.txt
INBOX/
<message-id-1>.eml
<message-id-2>.eml
Sent/
<message-id-3>.eml
Drafts/
<message-id-4>.eml
Os arquivos EML são organizados por pasta da caixa de correio. A senha do ZIP é a mesma da sua senha IMAP/alias. Cada arquivo .eml é uma mensagem de email padrão RFC 5322 com cabeçalhos completos, texto do corpo e anexos reconstruídos a partir do banco de dados SQLite.
Como Funciona
- Abre o banco de dados SQLite criptografado usando sua senha IMAP/alias (suporta os cifradores ChaCha20 e AES-256-CBC).
- Lê a tabela Mailboxes para descobrir a estrutura das pastas.
- Para cada mensagem, decodifica o mimeTree (armazenado como JSON comprimido com Brotli) da tabela Messages.
- Reconstrói o EML completo percorrendo a árvore MIME e buscando os corpos dos anexos na tabela Attachments.
- Empacota tudo em um arquivo ZIP protegido por senha usando archiver-zip-encrypted.
Vocês suportam auto-hospedagem
Sim, a partir de março de 2025, suportamos uma opção auto-hospedada. Leia o blog aqui. Confira o guia de auto-hospedagem para começar. E para quem estiver interessado em uma versão mais detalhada passo a passo, veja nossos guias baseados em Ubuntu ou Debian.
Configuração de Email
Como começo e configuro o encaminhamento de email
user@gmail.com pelo endereço de email para o qual deseja encaminhar os emails (se ainda não estiver correto). Da mesma forma, certifique-se de substituir example.com pelo seu nome de domínio personalizado (se ainda não estiver correto).
- Se você já registrou seu nome de domínio em algum lugar, então deve pular completamente esta etapa e ir para o passo dois! Caso contrário, você pode clicar aqui para registrar seu nome de domínio.
-
Você lembra onde registrou seu domínio? Uma vez que se lembre, siga as instruções abaixo:
Importante: Você deve abrir uma nova aba e entrar na sua conta do registrador de domínios. Você pode facilmente clicar no seu "Registrador" abaixo para fazer isso automaticamente. Nesta nova aba, você deve navegar até a página de gerenciamento de DNS no seu registrador – e fornecemos os passos detalhados de navegação abaixo na coluna "Passos para Configurar". Depois de navegar até essa página na nova aba, você pode retornar a esta aba e prosseguir para o passo três abaixo. Não feche a aba aberta ainda; você vai precisar dela para os próximos passos!
Registrador Passos para Configurar 1&1 Faça login Centro de Domínios (Selecione seu domínio) Editar Configurações de DNS Amazon Route 53 Faça login Zonas Hospedadas (Selecione seu domínio) Aplus.net Faça login Meus Servidores Gerenciamento de Domínios Gerenciador de DNS Bluehost PARA ROCK: Faça login Domínios (Clique no ícone ▼ ao lado de gerenciar) DNS
PARA LEGADO: Faça login Domínios Editor de Zona (Selecione seu domínio)Cloudflare Faça login DNS DNS Made Easy Faça login DNS (Selecione seu domínio) DNSimple Faça login (Selecione seu domínio) DNS Gerenciar Digital Ocean Faça login Rede Domínios (Selecione seu domínio) Mais Gerenciar Domínio Domain.com Faça login Na visualização em cartão, clique em gerenciar seu domínio Na visualização em lista, clique no ícone de engrenagem DNS & Nameservers Registros DNS Domains.com
AssistirFaça login (Selecione seu domínio) Gerenciar (clique no ícone de engrenagem) Clique em DNS & Nameservers no menu à esquerda DreamHost Faça login Painel Domínios Gerenciar Domínios DNS Dyn Faça login Visão Geral Gerenciar Editor Simples Registros Gandi Faça login (Selecione seu domínio) Gerenciamento Editar a zona GoDaddy
AssistirFaça login Gerenciar Meus Domínios (Selecione seu domínio) Gerenciar DNS Google Domains
AssistirFaça login (Selecione seu domínio) Configurar DNS Namecheap
AssistirFaça login Lista de Domínios (Selecione seu domínio) Gerenciar DNS Avançado Netlify Faça login (Selecione seu domínio) Configurar DNS Netlify Network Solutions Faça login Gerenciador de Conta Meus Nomes de Domínio (Selecione seu domínio) Gerenciar Alterar para onde o domínio aponta DNS Avançado Shopify
AssistirFaça login Domínios Gerenciados (Selecione seu domínio) Configurações de DNS Squarespace Faça login Menu inicial Configurações Domínios (Selecione seu domínio) Configurações avançadas Registros personalizados Now da Vercel Usando o CLI "now" now dns add [domain] '@' MX [record-value] [priority]Weebly Faça login Página de Domínios (Selecione seu domínio) DNS Wix Faça login Página de Domínios (Clique no ícone ) Selecione Gerenciar Registros DNS eNom Faça login Domínios Meus Domínios Outro Importante: Não vê o nome do seu registrador listado aqui? Simplesmente pesquise na Internet por "como alterar registros DNS no $REGISTRADOR" (substituindo $REGISTRADOR pelo nome do seu registrador – por exemplo, "como alterar registros DNS no GoDaddy" se você usa GoDaddy). - Usando a página de gerenciamento de DNS do seu registrador (a outra aba que você abriu), configure os seguintes registros "MX":
Importante: Observe que NÃO deve haver outros registros MX configurados. Ambos os registros mostrados abaixo DEVEM existir. Certifique-se de que não há erros de digitação; e que você escreveu corretamente tanto mx1 quanto mx2. Se já existiam registros MX, por favor, exclua-os completamente. O valor "TTL" não precisa ser 3600, pode ser um valor menor ou maior, se necessário.
Nome/Host/Alias TTL Tipo Prioridade Resposta/Valor "@", ".", ou vazio 3600 MX 0 mx1.forwardemail.net"@", ".", ou vazio 3600 MX 0 mx2.forwardemail.net - Usando a página de gerenciamento DNS do seu registrador (a outra aba que você abriu), configure o(s) seguinte(s) registro(s) TXT:
Importante: Se você está em um plano pago, deve pular completamente esta etapa e ir para o passo cinco! Se você não está em um plano pago, seus endereços encaminhados serão publicamente pesquisáveis – vá para Minha Conta Domínios e faça upgrade do seu domínio para um plano pago, se desejar. Se quiser saber mais sobre planos pagos, veja nossa página de Preços. Caso contrário, você pode continuar escolhendo uma ou mais combinações da Opção A até a Opção F listadas abaixo.
Opção A: Se você está encaminhando todos os e-mails do seu domínio, (ex.: "all@example.com", "hello@example.com", etc) para um endereço específico "user@gmail.com":Nome/Host/Alias TTL Tipo Resposta/Valor "@", ".", ou vazio 3600 TXT forward-email=user@gmail.comDica: Certifique-se de substituir os valores acima na coluna "Valor" pelo seu próprio endereço de e-mail. O valor "TTL" não precisa ser 3600, pode ser um valor menor ou maior, se necessário. Um valor menor de tempo de vida ("TTL") garantirá que quaisquer alterações futuras feitas nos seus registros DNS sejam propagadas pela Internet mais rapidamente – pense nisso como o tempo que ficará em cache na memória (em segundos). Você pode aprender mais sobre TTL na Wikipédia.
Opção B: Se você precisa apenas encaminhar um único endereço de e-mail (ex.:hello@example.comparauser@gmail.com; isso também encaminhará automaticamente "hello+test@example.com" para "user+test@gmail.com"):Nome/Host/Alias TTL Tipo Resposta/Valor "@", ".", ou em branco 3600 TXT forward-email=hello:user@gmail.com
Opção C: Se você estiver encaminhando múltiplos e-mails, então você deve separá-los com uma vírgula:Nome/Host/Alias TTL Tipo Resposta/Valor "@", ".", ou em branco 3600 TXT forward-email=hello:user@gmail.com,support:user@gmail.com
Opção D: Você pode configurar uma quantidade infinita de e-mails de encaminhamento – apenas certifique-se de não ultrapassar 255 caracteres em uma única linha e comece cada linha com "forward-email=". Um exemplo é fornecido abaixo:Nome/Host/Alias TTL Tipo Resposta/Valor "@", ".", ou em branco 3600 TXT forward-email=hello:user@gmail.com,support:user@gmail.com"@", ".", ou em branco 3600 TXT forward-email=help:user@gmail.com,foo:user@gmail.com"@", ".", ou em branco 3600 TXT forward-email=orders:user@gmail.com,baz:user@gmail.com"@", ".", ou em branco 3600 TXT forward-email=info:user@gmail.com,beep:user@gmail.com"@", ".", ou em branco 3600 TXT forward-email=errors:user@gmail.com,boop:user@gmail.com
Opção E: Você também pode especificar um nome de domínio no seu registro TXT para ter encaminhamento global de alias (por exemplo, "user@example.com" será encaminhado para "user@example.net"):Nome/Host/Alias TTL Tipo Resposta/Valor "@", ".", ou em branco 3600 TXT forward-email=example.net
Opção F: Você pode até usar webhooks como um alias global ou individual para encaminhar e-mails. Veja o exemplo e a seção completa sobre webhooks intitulada Você suporta webhooks abaixo.Nome/Host/Alias TTL Tipo Resposta/Valor "@", ".", ou em branco 3600 TXT forward-email=alias:https://requestbin.com/r/en8pfhdgcculn
Opção G: Você pode até usar expressões regulares ("regex") para corresponder aliases e para lidar com substituições para encaminhar e-mails. Veja os exemplos e a seção completa sobre regex intitulada Você suporta expressões regulares ou regex abaixo.Precisa de regex avançado com substituição? Veja os exemplos e a seção completa sobre regex intitulada Você suporta expressões regulares ou regex abaixo.Exemplo Simples: Se eu quiser que todos os e-mails que vão para `linus@example.com` ou `torvalds@example.com` sejam encaminhados para `user@gmail.com`:Nome/Host/Alias TTL Tipo Resposta/Valor "@", ".", ou em branco 3600 TXT forward-email=/^(linus|torvalds)$/:user@gmail.comImportante: Regras de encaminhamento catch-all também podem ser descritas como "fall-through". Isso significa que e-mails recebidos que correspondem a pelo menos uma regra específica de encaminhamento serão usados em vez do catch-all. Regras específicas incluem endereços de e-mail e expressões regulares.
Por exemplo:
forward-email=hello:first@gmail.com,second@gmail.com
E-mails enviados parahello@example.com**não** serão encaminhados parasecond@gmail.com(catch-all) com esta configuração, e em vez disso serão entregues apenas parafirst@gmail.com.
- Usando a página de gerenciamento de DNS do seu registrador (a outra aba que você abriu), configure adicionalmente o seguinte registro TXT:
Nome/Host/Alias TTL Tipo Resposta/Valor "@", ".", ou em branco 3600 TXT v=spf1 a include:spf.forwardemail.net -allImportante: Se você estiver usando Gmail (por exemplo, Enviar Email Como) ou G Suite, então precisará adicionarinclude:_spf.google.comao valor acima, por exemplo:
v=spf1 a include:spf.forwardemail.net include:_spf.google.com -allDica: Se você já tem uma linha similar com "v=spf1", então precisará adicionarinclude:spf.forwardemail.netlogo antes de quaisquer registros existentes "include:host.com" e antes do "-all" na mesma linha, por exemplo:
v=spf1 a include:spf.forwardemail.net include:host.com -all
Note que há uma diferença entre "-all" e "~all". O "-" indica que a verificação SPF deve FALHAR se não corresponder, e "~" indica que a verificação SPF deve SOFTFAIL. Recomendamos usar a abordagem "-all" para prevenir falsificação de domínio.
Você também pode precisar incluir o registro SPF para o host de onde estiver enviando e-mails (por exemplo, Outlook). - Verifique seus registros DNS usando nossa ferramenta "Verificar Registros" disponível em Minha Conta Domínios Configuração.
- Envie um e-mail de teste para confirmar que funciona. Note que pode levar algum tempo para que seus registros DNS se propaguem.
Dica: Se você não está recebendo e-mails de teste, ou recebe um e-mail de teste que diz "Tenha cuidado com esta mensagem", então veja as respostas para Por que não estou recebendo meus e-mails de teste e Por que meus e-mails de teste enviados para mim mesmo no Gmail aparecem como "suspeitos", respectivamente.
- Se você deseja "Enviar Email Como" pelo Gmail, então você precisará assistir a este vídeo, ou seguir os passos em Como Enviar Email Como Usando Gmail abaixo.
Posso usar múltiplos servidores e trocadores MX para encaminhamento avançado
Sim, mas você deve ter apenas um trocador MX listado em seus registros DNS.
Não tente usar "Prioridade" como forma de configurar múltiplos trocadores MX.
Em vez disso, você precisa configurar seu trocador MX existente para encaminhar e-mails para todos os aliases que não correspondem para os trocadores do nosso serviço (mx1.forwardemail.net e/ou mx2.forwardemail.net).
Se você estiver usando Google Workspace e quiser encaminhar todos os aliases que não correspondem para o nosso serviço, veja https://support.google.com/a/answer/6297084.
Se você estiver usando Microsoft 365 (Outlook) e quiser encaminhar todos os aliases que não correspondem para o nosso serviço, veja https://learn.microsoft.com/en-us/exchange/mail-flow-best-practices/use-connectors-to-configure-mail-flow/set-up-connectors-to-route-mail e https://learn.microsoft.com/en-us/exchange/mail-flow-best-practices/manage-mail-flow-for-multiple-locations.
Como configurar um respondedor de férias (resposta automática fora do escritório)
Vá para Minha Conta Domínios Aliases e crie ou edite o alias para o qual deseja configurar um respondedor automático de férias. Você tem a capacidade de configurar uma data de início, data de término, assunto e mensagem, e ativá-lo ou desativá-lo a qualquer momento:
- Assunto e mensagem em texto simples são atualmente suportados (usamos o pacote
striptagsinternamente para remover qualquer HTML). - O assunto é limitado a 100 caracteres.
- A mensagem é limitada a 1000 caracteres.
- A configuração requer configuração de SMTP de saída (por exemplo, você precisará configurar registros DNS DKIM, DMARC e Return-Path).
- Vá para Minha Conta Domínios Configurações Configuração SMTP de Saída e siga as instruções de configuração.
- O respondedor de férias não pode ser ativado em nomes de domínio globais personalizados (por exemplo, endereços descartáveis não são suportados).
- O respondedor de férias não pode ser ativado para aliases com curinga/catch-all (
*) nem expressões regulares.
Ao contrário de sistemas de e-mail como postfix (por exemplo, que usam a extensão de filtro de férias sieve) – o Forward Email adiciona automaticamente sua assinatura DKIM, previne problemas de conexão ao enviar respostas de férias (por exemplo, devido a problemas comuns de conexão SSL/TLS e servidores legados mantidos), e até suporta Open WKD e criptografia PGP para respostas de férias.
-
Enviamos apenas uma vez por remetente permitido a cada 4 dias (o que é semelhante ao comportamento do Gmail).
-
Nosso cache Redis usa uma impressão digital de
alias_idesender, ondealias_idé o ID do alias no MongoDB esenderé o endereço From (se permitido) ou o domínio raiz no endereço From (se não permitido). Para simplificar, o tempo de expiração dessa impressão digital no cache é definido para 4 dias. -
Nossa abordagem de usar o domínio raiz extraído do endereço From para remetentes não permitidos previne abusos de remetentes relativamente desconhecidos (por exemplo, atores maliciosos) que tentam inundar mensagens do respondedor de férias.
-
-
Enviamos apenas quando o MAIL FROM e/ou From não estiverem em branco e não contiverem (sem diferenciar maiúsculas de minúsculas) um nome de usuário postmaster (a parte antes do @ em um e-mail).
-
Não enviamos se a mensagem original tiver algum dos seguintes cabeçalhos (sem diferenciar maiúsculas de minúsculas):
- Cabeçalho
auto-submittedcom valor diferente deno. - Cabeçalho
x-auto-response-suppresscom valordr,autoreply,auto-reply,auto_replyouall. - Cabeçalho
list-id,list-subscribe,list-unsubscribe,list-help,list-post,list-owner,list-archive,x-autoreply,x-autorespondoux-auto-respond(independente do valor). - Cabeçalho
precedencecom valorbulk,autoreply,auto-reply,auto_replyoulist.
- Cabeçalho
-
Não enviamos se o endereço de e-mail MAIL FROM ou From terminar com
+donotreply,-donotreply,+noreplyou-noreply. -
Não enviamos se a parte do nome de usuário do endereço From for
mdaemone houver um cabeçalhoX-MDDSN-Message(sem diferenciar maiúsculas de minúsculas). -
Não enviamos se houver um cabeçalho
content-typecom valormultipart/report(sem diferenciar maiúsculas de minúsculas).
Como configurar SPF para Forward Email
Usando a página de gerenciamento DNS do seu registrador, configure o seguinte registro TXT:
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | v=spf1 a include:spf.forwardemail.net -all |
include:_spf.google.com ao valor acima, por exemplo:
v=spf1 a include:spf.forwardemail.net include:_spf.google.com -all
include:spf.protection.outlook.com ao seu registro SPF TXT, por exemplo:
v=spf1 a include:spf.forwardemail.net include:spf.protection.outlook.com -all
include:spf.forwardemail.net logo antes de quaisquer registros "include:host.com" existentes e antes do "-all" na mesma linha, por exemplo:
v=spf1 a include:spf.forwardemail.net include:host.com -all
Note que há uma diferença entre "-all" e "~all". O "-" indica que a verificação SPF deve FALHAR se não corresponder, e "~" indica que a verificação SPF deve SOFTFAIL. Recomendamos usar a abordagem "-all" para prevenir falsificação de domínio.
Você também pode precisar incluir o registro SPF para o host de onde está enviando o e-mail (por exemplo, Outlook).
Como configurar DKIM para Forward Email
Vá para Minha Conta Domínios Configurações Configuração SMTP de Saída e siga as instruções de configuração.
Como configurar DMARC para Forward Email
Vá para Minha Conta Domínios Configurações Configuração SMTP de Saída e siga as instruções de configuração.
Como visualizar Relatórios DMARC
Forward Email oferece um painel abrangente de Relatórios DMARC que permite monitorar o desempenho da autenticação de seus e-mails em todos os seus domínios a partir de uma única interface.
O que são Relatórios DMARC?
Relatórios DMARC (Domain-based Message Authentication, Reporting, and Conformance) são arquivos XML enviados pelos servidores de e-mail receptores que informam como seus e-mails estão sendo autenticados. Esses relatórios ajudam você a entender:
- Quantos e-mails estão sendo enviados do seu domínio
- Se esses e-mails estão passando na autenticação SPF e DKIM
- Quais ações os servidores receptores estão tomando (aceitar, colocar em quarentena ou rejeitar)
- Quais endereços IP estão enviando e-mails em nome do seu domínio
Como acessar os Relatórios DMARC
Vá para Minha Conta Relatórios DMARC para visualizar seu painel. Você também pode acessar relatórios específicos de domínio em Minha Conta Domínios clicando no botão "DMARC" ao lado de qualquer domínio.
Recursos do Painel
O painel de Relatórios DMARC oferece:
- Métricas Resumidas: Total de relatórios recebidos, total de mensagens analisadas, taxa de alinhamento SPF, taxa de alinhamento DKIM e taxa geral de aprovação
- Gráfico de Mensagens ao Longo do Tempo: Tendência visual do volume de e-mails e taxas de autenticação nos últimos 30 dias
- Resumo de Alinhamento: Gráfico de rosca mostrando a distribuição do alinhamento SPF vs DKIM
- Disposição das Mensagens: Gráfico de barras empilhadas mostrando como os servidores receptores trataram seus e-mails (aceitos, em quarentena ou rejeitados)
- Tabela de Relatórios Recentes: Lista detalhada de relatórios DMARC individuais com filtros e paginação
- Filtro por Domínio: Filtre relatórios por domínio específico ao gerenciar múltiplos domínios Por Que Isso Importa
Para organizações que gerenciam múltiplos domínios (como empresas, organizações sem fins lucrativos ou agências), os relatórios DMARC são essenciais para:
- Identificar remetentes não autorizados: Detectar se alguém está falsificando seu domínio
- Melhorar a entregabilidade: Garantir que seus e-mails legítimos passem na autenticação
- Monitorar a infraestrutura de e-mail: Acompanhar quais serviços e IPs estão enviando em seu nome
- Conformidade: Manter visibilidade na autenticação de e-mails para auditorias de segurança
Ao contrário de outros serviços que exigem ferramentas separadas de monitoramento DMARC, o Forward Email inclui o processamento e visualização de relatórios DMARC como parte da sua conta sem custo adicional.
Requisitos
- Relatórios DMARC estão disponíveis apenas para planos pagos
- Seu domínio deve ter DMARC configurado (veja Como configurar DMARC para Forward Email)
- Os relatórios são coletados automaticamente quando servidores de recebimento enviam para o endereço de relatório DMARC configurado
Relatórios Semanais por E-mail
Usuários de planos pagos recebem automaticamente resumos semanais dos relatórios DMARC por e-mail. Esses e-mails incluem:
- Estatísticas resumidas para todos os seus domínios
- Taxas de alinhamento SPF e DKIM
- Distribuição da disposição das mensagens (aceitas, em quarentena, rejeitadas)
- Principais organizações que reportam (Google, Microsoft, Yahoo, etc.)
- Endereços IP com problemas de alinhamento que podem precisar de atenção
- Links diretos para seu painel de Relatórios DMARC
Os relatórios semanais são enviados automaticamente e não podem ser desativados separadamente de outras notificações por e-mail.
Como conectar e configurar meus contatos
Para configurar seus contatos, use a URL CardDAV: https://carddav.forwardemail.net (ou simplesmente carddav.forwardemail.net se seu cliente permitir)
Como conectar e configurar meus calendários
Para configurar seu calendário, use a URL CalDAV: https://caldav.forwardemail.net (ou simplesmente caldav.forwardemail.net se seu cliente permitir)
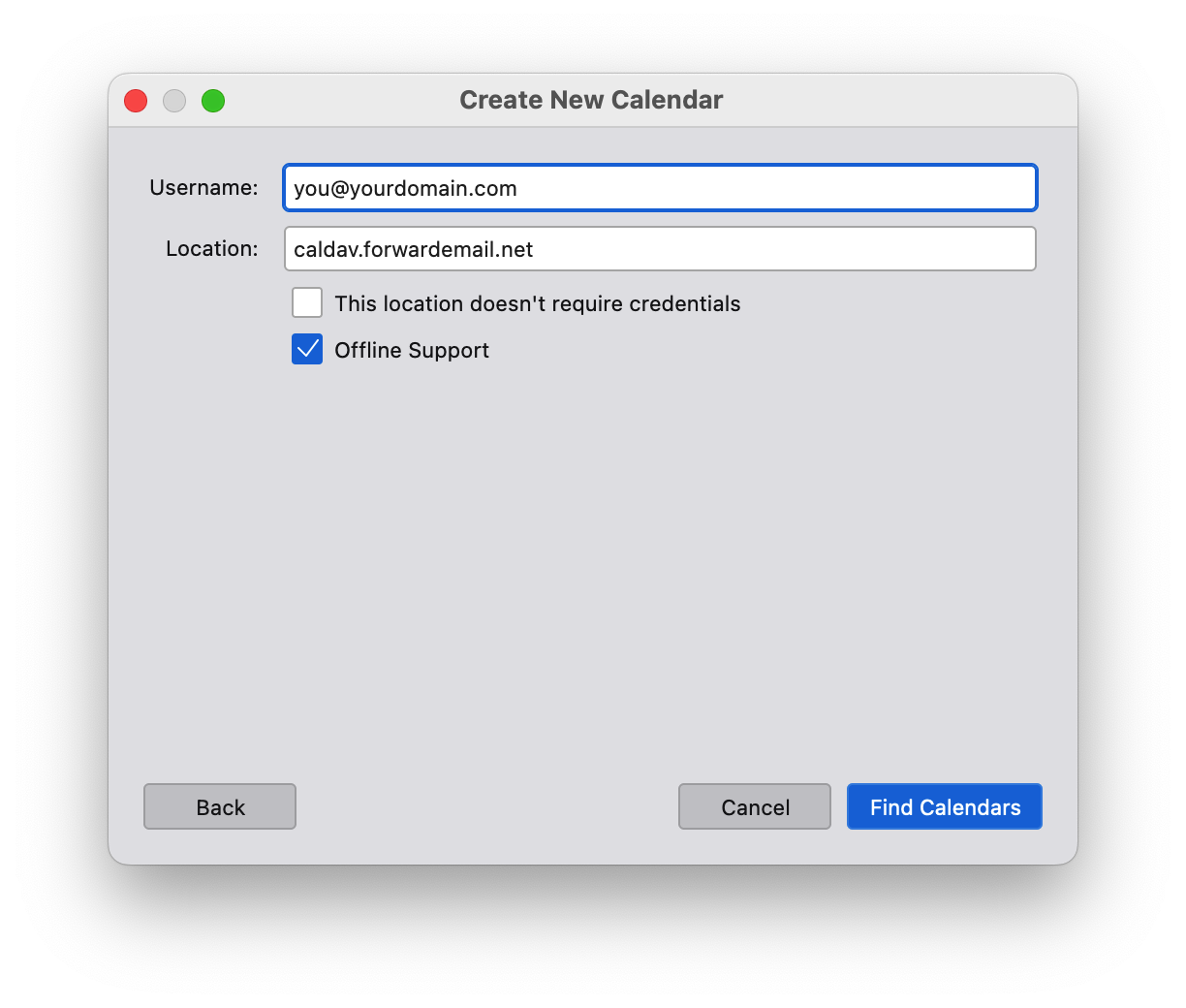
Como adicionar mais calendários e gerenciar calendários existentes
Se desejar adicionar calendários adicionais, basta adicionar uma nova URL de calendário: https://caldav.forwardemail.net/dav/principals/calendar-name (certifique-se de substituir calendar-name pelo nome desejado do calendário)
Você pode alterar o nome e a cor de um calendário após a criação – basta usar seu aplicativo de calendário preferido (ex.: Apple Mail ou Thunderbird).
Como conectar e configurar tarefas e lembretes
Para configurar tarefas e lembretes, use a mesma URL CalDAV dos calendários: https://caldav.forwardemail.net (ou simplesmente caldav.forwardemail.net se seu cliente permitir)
Tarefas e lembretes serão automaticamente separados dos eventos do calendário em sua própria coleção de calendário "Lembretes" ou "Tarefas".
Instruções de configuração por plataforma:
macOS/iOS:
- Adicione uma nova conta CalDAV em Preferências do Sistema > Contas de Internet (ou Ajustes > Contas no iOS)
- Use
caldav.forwardemail.netcomo servidor - Insira seu alias Forward Email e senha gerada
- Após a configuração, você verá as coleções "Calendário" e "Lembretes"
- Use o app Lembretes para criar e gerenciar tarefas
Android com Tasks.org:
- Instale o Tasks.org na Google Play Store ou F-Droid
- Vá em Configurações > Sincronização > Adicionar Conta > CalDAV
- Insira o servidor:
https://caldav.forwardemail.net - Insira seu alias Forward Email e senha gerada
- O Tasks.org descobrirá automaticamente seus calendários de tarefas
Thunderbird:
- Instale o complemento Lightning se ainda não estiver instalado
- Crie um novo calendário do tipo "CalDAV"
- Use a URL:
https://caldav.forwardemail.net - Insira suas credenciais Forward Email
- Eventos e tarefas estarão disponíveis na interface do calendário
Por que não consigo criar tarefas no macOS Lembretes
Se você está tendo problemas para criar tarefas no macOS Lembretes, tente estas etapas de solução de problemas:
-
Verifique a configuração da conta: Certifique-se de que sua conta CalDAV está configurada corretamente com
caldav.forwardemail.net -
Verifique calendários separados: Você deve ver tanto "Calendário" quanto "Lembretes" em sua conta. Se você vir apenas "Calendário", o suporte a tarefas pode não estar totalmente ativado ainda.
-
Atualize a conta: Tente remover e adicionar novamente sua conta CalDAV em Preferências do Sistema > Contas de Internet
-
Verifique a conectividade com o servidor: Teste se você consegue acessar
https://caldav.forwardemail.netno seu navegador -
Verifique as credenciais: Certifique-se de que está usando o alias de e-mail correto e a senha gerada (não a senha da sua conta)
-
Forçar sincronização: No app Lembretes, tente criar uma tarefa e depois atualizar manualmente a sincronização
Problemas comuns:
- "Calendário de lembretes não encontrado": O servidor pode precisar de um momento para criar a coleção de Lembretes no primeiro acesso
- Tarefas não sincronizam: Verifique se ambos os dispositivos estão usando as mesmas credenciais da conta CalDAV
- Conteúdo misto: Certifique-se de que as tarefas estão sendo criadas no calendário "Lembretes", não no "Calendário" geral
Como configurar o Tasks.org no Android
Tasks.org é um gerenciador de tarefas open-source popular que funciona perfeitamente com o suporte a tarefas CalDAV do Forward Email.
Instalação e Configuração:
-
Instale o Tasks.org:
- Na Google Play Store: Tasks.org
- No F-Droid: Tasks.org on F-Droid
-
Configure a sincronização CalDAV:
- Abra o Tasks.org
- Vá para ☰ Menu > Configurações > Sincronização
- Toque em "Adicionar Conta"
- Selecione "CalDAV"
-
Insira as configurações do Forward Email:
- URL do servidor:
https://caldav.forwardemail.net - Nome de usuário: Seu alias do Forward Email (ex.:
voce@seudominio.com) - Senha: Sua senha gerada específica para o alias
- Toque em "Adicionar Conta"
- URL do servidor:
-
Descoberta da conta:
- O Tasks.org irá descobrir automaticamente seus calendários de tarefas
- Você deverá ver sua coleção "Lembretes" aparecer
- Toque em "Assinar" para ativar a sincronização do calendário de tarefas
-
Teste a sincronização:
- Crie uma tarefa de teste no Tasks.org
- Verifique se ela aparece em outros clientes CalDAV (como o Lembretes do macOS)
- Confirme que as alterações sincronizam em ambas as direções
Recursos disponíveis:
- ✅ Criação e edição de tarefas
- ✅ Datas de vencimento e lembretes
- ✅ Conclusão e status das tarefas
- ✅ Níveis de prioridade
- ✅ Subtarefas e hierarquia de tarefas
- ✅ Etiquetas e categorias
- ✅ Sincronização bidirecional com outros clientes CalDAV
Solução de problemas:
- Se nenhum calendário de tarefas aparecer, tente atualizar manualmente nas configurações do Tasks.org
- Certifique-se de ter pelo menos uma tarefa criada no servidor (você pode criar uma primeiro no Lembretes do macOS)
- Verifique a conectividade de rede com
caldav.forwardemail.net
Como configurar SRS para Forward Email
Nós configuramos automaticamente o Sender Rewriting Scheme ("SRS") – você não precisa fazer isso manualmente.
Como configurar MTA-STS para Forward Email
Por favor, consulte nossa seção sobre MTA-STS para mais informações.
Como adicionar uma foto de perfil ao meu endereço de e-mail
Se você usa Gmail, siga os passos abaixo:
- Acesse https://google.com e saia de todas as contas de e-mail
- Clique em "Fazer login" e no menu suspenso clique em "outra conta"
- Selecione "Usar outra conta"
- Selecione "Criar conta"
- Selecione "Usar meu endereço de e-mail atual em vez disso"
- Digite seu endereço de e-mail do domínio personalizado
- Recupere o e-mail de verificação enviado para seu endereço
- Insira o código de verificação deste e-mail
- Complete as informações do perfil para sua nova conta Google
- Concorde com todas as políticas de Privacidade e Termos de Uso
- Acesse https://google.com e no canto superior direito, clique no ícone do seu perfil e clique no botão "alterar"
- Faça upload de uma nova foto ou avatar para sua conta
- As alterações levarão aproximadamente 1-2 horas para propagar, mas às vezes podem ser muito rápidas.
- Envie um e-mail de teste e a foto do perfil deverá aparecer.
Recursos Avançados
Vocês suportam newsletters ou listas de mala direta para e-mails relacionados a marketing
Sim, você pode ler mais em https://forwardemail.net/guides/newsletter-with-listmonk.
Por favor, note que para manter a reputação do IP e garantir a entregabilidade, o Forward Email possui um processo de revisão manual por domínio para aprovação de newsletter. Envie um e-mail para support@forwardemail.net ou abra uma solicitação de ajuda para aprovação. Isso normalmente leva menos de 24 horas, com a maioria das solicitações sendo atendidas em 1-2 horas. Em breve, pretendemos tornar esse processo instantâneo com controles adicionais de spam e alertas. Esse processo garante que seus e-mails cheguem à caixa de entrada e que suas mensagens não sejam marcadas como spam.
Vocês suportam o envio de e-mails via API
Sim, desde maio de 2023 suportamos o envio de e-mails via API como um complemento para todos os usuários pagos.
Por favor, consulte nossa seção sobre E-mails na documentação da API para opções, exemplos e mais informações.
Para enviar e-mails de saída com nossa API, você deve usar seu token de API disponível em Minha Segurança.
Vocês suportam o recebimento de e-mails via IMAP
Sim, desde 16 de outubro de 2023 suportamos o recebimento de e-mails via IMAP como um complemento para todos os usuários pagos. Por favor, leia nosso artigo detalhado sobre como funciona nosso recurso de armazenamento de caixa de correio criptografado SQLite.
-
Crie um novo alias para seu domínio em Minha Conta Domínios Aliases (ex.:
hello@example.com) -
Clique em Gerar Senha ao lado do alias recém-criado. Copie para sua área de transferência e armazene com segurança a senha gerada exibida na tela.
-
Usando seu aplicativo de e-mail preferido, adicione ou configure uma conta com seu alias recém-criado (ex.:
hello@example.com)Dica: Recomendamos usar Thunderbird, Thunderbird Mobile, Apple Mail ou uma alternativa open-source e focada em privacidade. -
Quando solicitado o nome do servidor IMAP, insira
imap.forwardemail.net -
Quando solicitado a porta do servidor IMAP, insira
993(SSL/TLS) – veja portas IMAP alternativas se necessárioDica: Se estiver usando Thunderbird, certifique-se de que "Segurança da conexão" esteja configurada para "SSL/TLS" e o método de autenticação para "Senha normal". -
Quando solicitado a senha do servidor IMAP, cole a senha de Gerar Senha no passo 2 acima
-
Salve suas configurações – se estiver tendo problemas, por favor contate-nos
Vocês suportam POP3
Sim, a partir de 4 de dezembro de 2023 suportamos POP3 como um complemento para todos os usuários pagos. Por favor, leia nosso artigo detalhado sobre como funciona nosso recurso de armazenamento de caixa de correio criptografado SQLite.
-
Crie um novo alias para seu domínio em Minha Conta Domínios Aliases (ex.
hello@example.com) -
Clique em Gerar Senha ao lado do alias recém-criado. Copie para sua área de transferência e armazene com segurança a senha gerada exibida na tela.
-
Usando seu aplicativo de e-mail preferido, adicione ou configure uma conta com seu alias recém-criado (ex.
hello@example.com)Dica: Recomendamos usar Thunderbird, Thunderbird Mobile, Apple Mail, ou uma alternativa open-source e focada em privacidade. -
Quando solicitado o nome do servidor POP3, insira
pop3.forwardemail.net -
Quando solicitado a porta do servidor POP3, insira
995(SSL/TLS) – veja portas alternativas para POP3 se necessárioDica: Se estiver usando Thunderbird, certifique-se de que "Segurança da conexão" esteja configurada para "SSL/TLS" e o método de autenticação esteja definido como "Senha normal". -
Quando solicitado a senha do servidor POP3, cole a senha de Gerar Senha no passo 2 acima
-
Salve suas configurações – se estiver tendo problemas, por favor contate-nos
Vocês suportam calendários (CalDAV)
Sim, a partir de 5 de fevereiro de 2024 adicionamos este recurso. Nosso servidor é caldav.forwardemail.net e também é monitorado em nossa página de status.
Ele suporta tanto IPv4 quanto IPv6 e está disponível na porta 443 (HTTPS).
| Login | Exemplo | Descrição |
|---|---|---|
| Nome de usuário | user@example.com |
Endereço de e-mail de um alias que existe para o domínio em Minha Conta Domínios. |
| Senha | ************************ |
Senha gerada específica para o alias. |
Para usar o suporte ao calendário, o usuário deve ser o endereço de e-mail de um alias que existe para o domínio em Minha Conta Domínios – e a senha deve ser uma senha gerada específica para o alias.
Vocês suportam tarefas e lembretes (CalDAV VTODO)
Sim, a partir de 14 de outubro de 2025 adicionamos suporte CalDAV VTODO para tarefas e lembretes. Isso usa o mesmo servidor do nosso suporte ao calendário: caldav.forwardemail.net.
Nosso servidor CalDAV suporta tanto eventos de calendário (VEVENT) quanto componentes de tarefas (VTODO) usando calendários unificados. Isso significa que cada calendário pode conter tanto eventos quanto tarefas, proporcionando máxima flexibilidade e compatibilidade em todos os clientes CalDAV.
Como funcionam os calendários e listas:
- Cada calendário suporta eventos e tarefas - Você pode adicionar eventos, tarefas ou ambos em qualquer calendário
- Listas do Apple Lembretes - Cada lista que você cria no Apple Lembretes se torna um calendário separado no servidor
- Múltiplos calendários - Você pode criar quantos calendários precisar, cada um com seu próprio nome, cor e organização
- Sincronização entre clientes - Tarefas e eventos sincronizam perfeitamente entre todos os clientes compatíveis
Clientes de tarefas suportados:
- macOS Lembretes - Suporte nativo completo para criação, edição, conclusão e sincronização de tarefas
- iOS Lembretes - Suporte nativo completo em todos os dispositivos iOS
- Tasks.org (Android) - Gerenciador de tarefas open-source popular com sincronização CalDAV
- Thunderbird - Suporte a tarefas e calendário no cliente de e-mail desktop
- Qualquer gerenciador de tarefas compatível com CalDAV - Suporte padrão ao componente VTODO
Recursos de tarefas suportados:
- Criação, edição e exclusão de tarefas
- Datas de vencimento e datas de início
- Status de conclusão da tarefa (NEEDS-ACTION, IN-PROCESS, COMPLETED, CANCELLED)
- Níveis de prioridade da tarefa
- Tarefas recorrentes
- Descrições e notas das tarefas
- Sincronização entre múltiplos dispositivos
- Subtarefas com propriedade RELATED-TO
- Lembretes de tarefas com VALARM
As credenciais de login são as mesmas do suporte ao calendário:
| Login | Exemplo | Descrição |
|---|---|---|
| Nome de usuário | user@example.com |
Endereço de e-mail de um alias que existe para o domínio em Minha Conta Domínios. |
| Senha | ************************ |
Senha gerada específica para o alias. |
Notas importantes:
- Cada lista do Lembretes é um calendário separado - Quando você cria uma nova lista no Apple Lembretes, ela cria um novo calendário no servidor CalDAV
- Usuários Thunderbird - Você precisará se inscrever manualmente em cada calendário/lista que deseja sincronizar, ou usar a URL da home do calendário:
https://caldav.forwardemail.net/dav/your-email@domain.com/ - Usuários Apple - A descoberta do calendário acontece automaticamente, então todos os seus calendários e listas aparecerão no Calendar.app e Reminders.app
- Calendários unificados - Todos os calendários suportam eventos e tarefas, dando flexibilidade na organização dos seus dados
Você suporta contatos (CardDAV)
Sim, a partir de 12 de junho de 2025 adicionamos esse recurso. Nosso servidor é carddav.forwardemail.net e também é monitorado em nossa página de status.
Ele suporta tanto IPv4 quanto IPv6 e está disponível na porta 443 (HTTPS).
| Login | Exemplo | Descrição |
|---|---|---|
| Nome de usuário | user@example.com |
Endereço de email de um alias que existe para o domínio em Minha Conta Domínios. |
| Senha | ************************ |
Senha gerada específica para o alias. |
Para usar o suporte a contatos, o usuário deve ser o endereço de email de um alias que existe para o domínio em Minha Conta Domínios – e a senha deve ser uma senha gerada específica para o alias.
Você suporta envio de email com SMTP
Sim, desde maio de 2023 suportamos o envio de email com SMTP como um complemento para todos os usuários pagos.
-
Vá para Minha Conta Domínios Configurações Configuração SMTP de Saída e siga as instruções de configuração
-
Crie um novo alias para seu domínio em Minha Conta Domínios Aliases (ex.
hello@example.com) -
Clique em Gerar Senha ao lado do alias recém-criado. Copie para sua área de transferência e armazene com segurança a senha gerada exibida na tela.
-
Usando seu aplicativo de email preferido, adicione ou configure uma conta com seu alias recém-criado (ex.
hello@example.com)Dica: Recomendamos usar Thunderbird, Thunderbird Mobile, Apple Mail ou uma alternativa open-source e focada em privacidade. -
Quando solicitado o nome do servidor SMTP, insira
smtp.forwardemail.net -
Quando solicitado a porta do servidor SMTP, insira
465(SSL/TLS) – veja portas SMTP alternativas se necessárioDica: Se você estiver usando Thunderbird, certifique-se de que "Segurança da conexão" esteja configurada para "SSL/TLS" e o método de autenticação esteja definido como "Senha normal". -
Quando solicitado a senha do servidor SMTP, cole a senha de Gerar Senha no passo 3 acima
-
Salve suas configurações e envie seu primeiro e-mail de teste – se estiver tendo problemas, por favor contate-nos
Vocês suportam OpenPGP/MIME, criptografia de ponta a ponta ("E2EE") e Web Key Directory ("WKD")
Sim, suportamos OpenPGP, criptografia de ponta a ponta ("E2EE") e a descoberta de chaves públicas usando Web Key Directory ("WKD"). Você pode configurar o OpenPGP usando keys.openpgp.org ou hospedar suas próprias chaves (consulte este gist para configuração do servidor WKD).
- As consultas WKD são armazenadas em cache por 1 hora para garantir a entrega oportuna do e-mail → portanto, se você adicionar, alterar ou remover sua chave WKD, por favor envie um e-mail para
support@forwardemail.netcom seu endereço de e-mail para que possamos limpar o cache manualmente. - Suportamos criptografia PGP para mensagens encaminhadas via consulta WKD ou usando uma chave PGP carregada em nossa interface.
- Chaves carregadas têm precedência enquanto a caixa de seleção PGP estiver habilitada/marcada.
- Mensagens enviadas para webhooks atualmente não são criptografadas com PGP.
- Se você tiver múltiplos aliases que correspondem a um endereço de encaminhamento dado (ex: combinação regex/wildcard/exata) e se mais de um deles contiver uma chave PGP carregada e tiver PGP marcado → então enviaremos um e-mail de alerta de erro e não criptografaremos a mensagem com sua chave PGP carregada. Isso é muito raro e geralmente se aplica apenas a usuários avançados com regras complexas de alias.
- A criptografia PGP não será aplicada ao encaminhamento de e-mail através dos nossos servidores MX se o remetente tiver uma política DMARC de rejeição. Se você precisar de criptografia PGP em todos os e-mails, sugerimos usar nosso serviço IMAP e configurar sua chave PGP para seu alias para e-mails recebidos.
Você pode validar sua configuração do Web Key Directory em https://wkd.chimbosonic.com/ (open-source) ou https://www.webkeydirectory.com/ (proprietário).
-
Baixe e instale o plugin recomendado para seu cliente de email abaixo:
Cliente de Email Plataforma Plugin Recomendado Notas Thunderbird Desktop Configurar OpenPGP no Thunderbird Thunderbird tem suporte nativo para OpenPGP. Gmail Navegador Mailvelope ou FlowCrypt (licença proprietária) O Gmail não suporta OpenPGP, porém você pode baixar o plugin open-source Mailvelope ou FlowCrypt. Apple Mail macOS Free-GPGMail O Apple Mail não suporta OpenPGP, porém você pode baixar o plugin open-source Free-GPGMail. Apple Mail iOS PGPro ou FlowCrypt (licença proprietária) O Apple Mail não suporta OpenPGP, porém você pode baixar o plugin open-source PGPro ou FlowCrypt. Outlook Windows gpg4win O cliente de email desktop do Outlook não suporta OpenPGP, porém você pode baixar o plugin open-source gpg4win. Outlook Navegador Mailvelope ou FlowCrypt (licença proprietária) O cliente de email web do Outlook não suporta OpenPGP, porém você pode baixar o plugin open-source Mailvelope ou FlowCrypt. Android Mobile OpenKeychain ou FlowCrypt Clientes de email Android como Thunderbird Mobile e FairEmail suportam o plugin open-source OpenKeychain. Você pode alternativamente usar o plugin open-source (licenciamento proprietário) FlowCrypt. Google Chrome Navegador Mailvelope ou FlowCrypt (licença proprietária) Você pode baixar a extensão open-source para navegador Mailvelope ou FlowCrypt. Mozilla Firefox Navegador Mailvelope ou FlowCrypt (licença proprietária) Você pode baixar a extensão open-source para navegador Mailvelope ou FlowCrypt. Microsoft Edge Navegador Mailvelope Você pode baixar a extensão open-source para navegador Mailvelope. Brave Navegador Mailvelope ou FlowCrypt (licença proprietária) Você pode baixar a extensão open-source para navegador Mailvelope ou FlowCrypt. Balsa Desktop Configurar OpenPGP no Balsa Balsa tem suporte nativo para OpenPGP. KMail Desktop Configurar OpenPGP no KMail KMail tem suporte nativo para OpenPGP. GNOME Evolution Desktop Configurar OpenPGP no Evolution GNOME Evolution tem suporte nativo para OpenPGP. Terminal Desktop Configurar gpg no Terminal Você pode usar a ferramenta open-source de linha de comando gpg para gerar uma nova chave via linha de comando. -
Abra o plugin, crie sua chave pública e configure seu cliente de e-mail para usá-la.
-
Faça o upload da sua chave pública em https://keys.openpgp.org/upload.
Dica: Você pode visitar https://keys.openpgp.org/manage para gerenciar sua chave no futuro.Complemento Opcional: Se você estiver usando nosso serviço de armazenamento criptografado (IMAP/POP3) e quiser que todos os e-mails armazenados em seu banco de dados SQLite (já criptografado) sejam criptografados com sua chave pública, então vá para Minha Conta Domínios Aliases (ex.hello@example.com) Editar OpenPGP e faça o upload da sua chave pública. -
Adicione um novo registro
CNAMEao seu nome de domínio (ex.example.com):Nome/Host/Alias TTL Tipo Resposta/Valor openpgpkey3600 CNAME wkd.keys.openpgp.orgDica: Se seu alias estiver usando nossos domínios descartáveis/vanity (ex.hideaddress.net), então você pode pular esta etapa.
Vocês suportam criptografia S/MIME
Sim, suportamos criptografia S/MIME (Secure/Multipurpose Internet Mail Extensions) conforme definido na RFC 8551. S/MIME fornece criptografia de ponta a ponta usando certificados X.509, amplamente suportados por clientes de e-mail corporativos.
Suportamos certificados RSA e ECC (Criptografia de Curva Elíptica):
- Certificados RSA: mínimo de 2048 bits, recomendado 4096 bits
- Certificados ECC: curvas NIST P-256, P-384 e P-521
Para configurar a criptografia S/MIME para seu alias:
-
Obtenha um certificado S/MIME de uma Autoridade Certificadora (CA) confiável ou gere um certificado autoassinado para testes.
Dica: Certificados S/MIME gratuitos estão disponíveis em provedores como Actalis ou Actalis Free S/MIME. -
Exporte seu certificado no formato PEM (apenas o certificado público, não a chave privada).
-
Vá para Minha Conta Domínios Aliases (ex.
hello@example.com) Editar S/MIME e faça o upload do seu certificado público. -
Uma vez configurado, todos os e-mails recebidos para seu alias serão criptografados usando seu certificado S/MIME antes de serem armazenados ou encaminhados.
Nota: A criptografia S/MIME é aplicada às mensagens recebidas que ainda não estão criptografadas. Se uma mensagem já estiver criptografada com OpenPGP ou S/MIME, ela não será recriptografada.Importante: A criptografia S/MIME não será aplicada ao encaminhamento de e-mails através dos nossos servidores MX se o remetente tiver uma política DMARC de rejeição. Se você precisar de criptografia S/MIME em todos os e-mails, sugerimos usar nosso serviço IMAP e configurar seu certificado S/MIME para seu alias para e-mails recebidos.
Os seguintes clientes de e-mail possuem suporte nativo a S/MIME:
| Cliente de E-mail | Plataforma | Notas |
|---|---|---|
| Apple Mail | macOS | Suporte nativo a S/MIME. Vá em Mail > Preferences > Accounts > sua conta > Trust para configurar certificados. |
| Apple Mail | iOS | Suporte nativo a S/MIME. Vá em Settings > Mail > Accounts > sua conta > Advanced > S/MIME para configurar. |
| Microsoft Outlook | Windows | Suporte nativo a S/MIME. Vá em File > Options > Trust Center > Trust Center Settings > Email Security para configurar. |
| Microsoft Outlook | macOS | Suporte nativo a S/MIME. Vá em Tools > Accounts > Advanced > Security para configurar. |
| Thunderbird | Desktop | Suporte nativo a S/MIME. Vá em Account Settings > End-To-End Encryption > S/MIME para configurar. |
| GNOME Evolution | Desktop | Suporte nativo a S/MIME. Vá em Edit > Preferences > Mail Accounts > sua conta > Security para configurar. |
| KMail | Desktop | Suporte nativo a S/MIME. Vá em Settings > Configure KMail > Identities > sua identidade > Cryptography para configurar. |
Vocês suportam filtragem de e-mail Sieve
Sim! Suportamos filtragem de e-mail Sieve conforme definido na RFC 5228. Sieve é uma linguagem de script poderosa e padronizada para filtragem de e-mails no lado do servidor que permite organizar, filtrar e responder automaticamente às mensagens recebidas.
Extensões Sieve suportadas
Suportamos um conjunto abrangente de extensões Sieve:
| Extensão | RFC | Descrição |
|---|---|---|
fileinto |
RFC 5228 | Arquivar mensagens em pastas específicas |
reject / ereject |
RFC 5429 | Rejeitar mensagens com um erro |
vacation |
RFC 5230 | Respostas automáticas de férias/ausência |
vacation-seconds |
RFC 6131 | Intervalos detalhados para respostas de férias |
imap4flags |
RFC 5232 | Definir flags IMAP (\Seen, \Flagged, etc.) |
envelope |
RFC 5228 | Testar remetente/destinatário do envelope |
body |
RFC 5173 | Testar conteúdo do corpo da mensagem |
variables |
RFC 5229 | Armazenar e usar variáveis em scripts |
relational |
RFC 5231 | Comparações relacionais (maior que, menor que) |
comparator-i;ascii-numeric |
RFC 4790 | Comparações numéricas |
copy |
RFC 3894 | Copiar mensagens enquanto redireciona |
editheader |
RFC 5293 | Adicionar ou deletar cabeçalhos de mensagem |
date |
RFC 5260 | Testar valores de data/hora |
index |
RFC 5260 | Acessar ocorrências específicas de cabeçalhos |
regex |
draft-ietf-sieve-regex | Correspondência por expressões regulares |
enotify |
RFC 5435 | Enviar notificações (ex: mailto:) |
environment |
RFC 5183 | Acessar informações do ambiente |
mailbox |
RFC 5490 | Testar existência de caixa postal, criar caixas |
special-use |
RFC 8579 | Arquivar em caixas de uso especial (\Junk, \Trash) |
duplicate |
RFC 7352 | Detectar mensagens duplicadas |
ihave |
RFC 5463 | Testar disponibilidade de extensão |
subaddress |
RFC 5233 | Acessar partes do endereço user+detail |
Extensões Não Suportadas
As seguintes extensões não são atualmente suportadas:
| Extensão | Motivo |
|---|---|
include |
Risco de segurança (injeção de script) e requer armazenamento global de scripts |
mboxmetadata / servermetadata |
Requer suporte à extensão IMAP METADATA |
foreverypart / mime / extracttext / replace / enclose |
Manipulação complexa da árvore MIME ainda não implementada |
Exemplos de Scripts Sieve
Arquivar newsletters em uma pasta:
require ["fileinto"];
if header :contains "List-Id" "newsletter" {
fileinto "Newsletters";
}
Resposta automática durante férias:
require ["vacation"];
vacation :days 7 :subject "Fora do Escritório"
"Estou atualmente fora do escritório e responderei quando retornar.";
Marcar mensagens de remetentes importantes:
require ["imap4flags"];
if address :is "from" "boss@example.com" {
setflag "\\Flagged";
}
Rejeitar spam com assuntos específicos:
require ["reject"];
if header :contains "subject" ["lottery", "winner", "urgent transfer"] {
reject "Mensagem rejeitada devido a conteúdo de spam.";
}
Descartar silenciosamente mensagens indesejadas:
if header :contains "List-Unsubscribe" "marketing.example.com" {
discard;
}
Filtragem complexa com variáveis:
require ["variables", "fileinto", "mailbox"];
if address :all :matches "From" "*@example.com" {
set :lower :upperfirst "sender" "${1}";
fileinto :create "Contacts/${sender}";
}
Gerenciando Scripts Sieve
Você pode gerenciar seus scripts Sieve de várias maneiras:
-
Interface Web: Vá para Minha Conta Domínios Apelidos Scripts Sieve para criar e gerenciar scripts.
-
Protocolo ManageSieve: Conecte-se usando qualquer cliente compatível com ManageSieve (como o complemento Sieve do Thunderbird ou sieve-connect) para
imap.forwardemail.net. Use a porta2190com STARTTLS (recomendado para a maioria dos clientes) ou a porta4190com TLS implícito. -
API: Use nossa API REST para gerenciar scripts programaticamente.
Vocês suportam MTA-STS
Sim, desde 2 de março de 2023 suportamos MTA-STS. Você pode usar este modelo se desejar habilitá-lo em seu domínio.
Nossa configuração pode ser encontrada publicamente no GitHub em https://github.com/forwardemail/mta-sts.forwardemail.net.
Vocês suportam passkeys e WebAuthn
Sim! Desde 13 de dezembro de 2023 adicionamos suporte para passkeys devido à alta demanda.
Passkeys permitem que você faça login com segurança sem precisar de senha e autenticação de dois fatores.
Você pode validar sua identidade com toque, reconhecimento facial, senha baseada no dispositivo ou PIN.
Permitimos que você gerencie até 30 passkeys ao mesmo tempo, para que possa fazer login com todos os seus dispositivos com facilidade.
Saiba mais sobre passkeys nos seguintes links:
- Faça login em seus aplicativos e sites com passkeys (Google)
- Use passkeys para fazer login em apps e sites no iPhone (Apple)
- Artigo da Wikipedia sobre Passkeys
Vocês suportam as melhores práticas de email
Sim. Temos suporte integrado para SPF, DKIM, DMARC, ARC e SRS em todos os planos. Também trabalhamos extensivamente com os autores originais dessas especificações e outros especialistas em email para garantir perfeição e alta entregabilidade.
Vocês suportam webhooks de bounce
Sim, a partir de 14 de agosto de 2024 adicionamos esse recurso. Agora você pode ir em Minha Conta → Domínios → Configurações → URL do Webhook de Bounce e configurar uma URL http:// ou https:// para a qual enviaremos uma requisição POST sempre que emails SMTP enviados retornarem bounce.
Isso é útil para você gerenciar e monitorar seu SMTP de saída – e pode ser usado para manter assinantes, opt-out e detectar sempre que ocorrerem bounces.
Os payloads do webhook de bounce são enviados como JSON com as seguintes propriedades:
email_id(String) - ID do email que corresponde a um email em Minha Conta → Emails (SMTP de saída)list_id(String) - valor do cabeçalhoList-ID(case-insensitive), se houver, do email original enviadolist_unsubscribe(String) - valor do cabeçalhoList-Unsubscribe(case-insensitive), se houver, do email original enviadofeedback_id(String) - valor do cabeçalhoFeedback-ID(case-insensitive), se houver, do email original enviadorecipient(String) - endereço de email do destinatário que retornou bounce ou erromessage(String) - mensagem detalhada de erro do bounceresponse(String) - mensagem de resposta SMTPresponse_code(Number) - código de resposta SMTP analisadotruth_source(String) - se o código de resposta veio de uma fonte confiável, este valor será preenchido com o nome do domínio raiz (ex.:google.comouyahoo.com)bounce(Object) - objeto contendo as seguintes propriedades que detalham o bounce e o status de rejeiçãoaction(String) - ação do bounce (ex.:"reject")message(String) - motivo do bounce (ex.:"Message Sender Blocked By Receiving Server")category(String) - categoria do bounce (ex.:"block")code(Number) - código de status do bounce (ex.:554)status(String) - código do bounce da mensagem de resposta (ex.:5.7.1)line(Number) - número da linha analisada, se houver, da lista de parse de bounce do Zone-MTA (ex.:526)
headers(Object) - pares chave-valor dos cabeçalhos do email enviadobounced_at(String) - data formatada em ISO 8601 de quando o erro de bounce ocorreu
Por exemplo:
{
"email_id": "66bcce793ef7b2a0928e14ba",
"recipient": "example@gmail.com",
"message": "The email account that you tried to reach is over quota.",
"response": "552 5.2.2 The email account that you tried to reach is over quota.",
"response_code": 552,
"truth_source": "google.com",
"bounce": {
"action": "reject",
"message": "Gmail Mailbox is full",
"category": "capacity",
"code": 552,
"status": "5.2.2",
"line": 300
},
"headers": {},
"bounced_at": "2024-08-24T01:50:02.828Z"
}
Aqui estão algumas notas adicionais sobre webhooks de bounce:
- Se o payload do webhook contiver um valor
list_id,list_unsubscribeoufeedback_id, você deve tomar a ação apropriada para remover orecipientda lista, se necessário.- Se o valor de
bounce.categoryfor um dos seguintes:"block","recipient","spam"ou"virus", você definitivamente deve remover o usuário da lista.
- Se o valor de
- Se precisar verificar os payloads do webhook (para garantir que eles realmente vêm do nosso servidor), você pode resolver o endereço IP remoto do cliente para o hostname usando uma busca reversa – deve ser
smtp.forwardemail.net.- Você também pode verificar o IP contra nossos endereços IP publicados.
- Vá em Minha Conta → Domínios → Configurações → Chave de Verificação de Payload da Assinatura do Webhook para obter sua chave de webhook.
- Você pode rotacionar essa chave a qualquer momento por razões de segurança.
- Calcule e compare o valor
X-Webhook-Signatureda nossa requisição de webhook com o valor do corpo computado usando essa chave. Um exemplo de como fazer isso está disponível em esta postagem do Stack Overflow.
- Veja a discussão em https://github.com/forwardemail/free-email-forwarding/issues/235 para mais informações.
- Esperaremos até
5segundos para que seu endpoint de webhook responda com um código de status200, e tentaremos novamente até1vez. - Se detectarmos que sua URL de webhook de bounce apresenta erro ao tentarmos enviar uma requisição, enviaremos um email de cortesia uma vez por semana.
Você suporta webhooks
Sim, desde 15 de maio de 2020 adicionamos esse recurso. Você pode simplesmente adicionar webhook(s) exatamente como faria com qualquer destinatário! Por favor, certifique-se de que o protocolo "http" ou "https" esteja prefixado na URL do webhook.
Se você está no plano gratuito, basta adicionar um novo registro DNS TXT conforme mostrado abaixo:
Por exemplo, se eu quiser que todos os e-mails enviados para alias@example.com sejam encaminhados para um novo endpoint de teste request bin:
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=alias:https://requestbin.com/r/en8pfhdgcculn |
Ou talvez você queira que todos os e-mails enviados para example.com sejam encaminhados para este endpoint:
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=https://requestbin.com/r/en8pfhdgcculn |
Aqui estão notas adicionais sobre webhooks:
- Se você precisar verificar os payloads do webhook (para garantir que eles realmente vêm do nosso servidor), então você pode resolver o endereço IP remoto do cliente e o hostname do cliente usando uma busca reversa – deve ser
mx1.forwardemail.netoumx2.forwardemail.net.- Você também pode verificar o IP contra nossos endereços IP publicados.
- Se você estiver em um plano pago, vá para Minha Conta → Domínios → Configurações → Chave de Verificação de Payload da Assinatura do Webhook para obter sua chave de webhook.
- Você pode rotacionar essa chave a qualquer momento por razões de segurança.
- Calcule e compare o valor
X-Webhook-Signatureda nossa requisição webhook com o valor do corpo computado usando essa chave. Um exemplo de como fazer isso está disponível em esta postagem do Stack Overflow.
- Veja a discussão em https://github.com/forwardemail/free-email-forwarding/issues/235 para mais informações.
- Se um webhook não responder com um código de status
200, então armazenaremos sua resposta no log de erros criado – o que é útil para depuração. - As requisições HTTP do webhook serão tentadas até 3 vezes a cada tentativa de conexão SMTP, com um timeout máximo de 60 segundos por requisição POST ao endpoint. Note que isso não significa que ele só tenta 3 vezes, na verdade ele tentará continuamente ao longo do tempo enviando um código SMTP 421 (que indica ao remetente para tentar novamente depois) após a 3ª tentativa falha de requisição HTTP POST. Isso significa que o e-mail será tentado continuamente por dias até que um código de status 200 seja alcançado.
- Tentaremos automaticamente com base nos códigos de status e erro padrão usados no método retry do superagent (somos mantenedores).
- Agrupamos as requisições HTTP do webhook para o mesmo endpoint em uma única requisição em vez de múltiplas para economizar recursos e acelerar o tempo de resposta. Por exemplo, se você enviar um e-mail para webhook1@example.com, webhook2@example.com e webhook3@example.com, e todos estiverem configurados para atingir o mesmo URL exato do endpoint, então apenas uma requisição será feita. Agrupamos por correspondência exata do endpoint com igualdade estrita.
- Note que usamos o método "simpleParser" da biblioteca mailparser para analisar a mensagem em um objeto amigável ao JSON.
- O valor do e-mail bruto como String é fornecido na propriedade "raw".
- Os resultados de autenticação são fornecidos nas propriedades "dkim", "spf", "arc", "dmarc" e "bimi".
- Os cabeçalhos do e-mail analisados são fornecidos na propriedade "headers" – mas também note que você pode usar "headerLines" para facilitar a iteração e análise.
- Os destinatários agrupados para este webhook são agrupados juntos e fornecidos na propriedade "recipients".
- As informações da sessão SMTP são fornecidas na propriedade "session". Isso contém informações sobre o remetente da mensagem, horário de chegada da mensagem, HELO e hostname do cliente. O valor do hostname do cliente como
session.clientHostnameé ou o FQDN (de uma busca PTR reversa) ou ésession.remoteAddressentre colchetes (ex.:"[127.0.0.1]"). - Se você precisar de uma forma rápida de obter o valor de
X-Original-To, então pode usar o valor desession.recipient(veja o exemplo abaixo). O cabeçalhoX-Original-Toé um cabeçalho que adicionamos às mensagens para depuração com o destinatário original (antes do encaminhamento mascarado) da mensagem. - Se você precisar remover as propriedades
attachmentse/ourawdo corpo do payload, basta adicionar?attachments=false,?raw=falseou?attachments=false&raw=falseao seu endpoint webhook como parâmetro de querystring (ex.:https://example.com/webhook?attachments=false&raw=false). - Se houver anexos, eles serão adicionados ao Array
attachmentscom valores Buffer. Você pode analisá-los de volta para conteúdo usando uma abordagem com JavaScript como:const data = [ 104, 101, 108, 108, 111, 32, 119, 111, 114, 108, 100, 33 ]; // // outputs "hello world!" to the console // (this is the content from the filename "text1.txt" in the example JSON request payload above) // console.log(Buffer.from(data).toString());
{
"attachments": [
{
"type": "attachment",
"content": {
"type": "Buffer",
"data": [
104,
101,
108,
108,
111,
32,
119,
111,
114,
108,
100,
33
]
},
"contentType": "text/plain",
"partId": "2",
"release": null,
"contentDisposition": "attachment",
"filename": "text1.txt",
"headers": {},
"checksum": "fc3ff98e8c6a0d3087d515c0473f8677",
"size": 12
}
],
"headers": "ARC-Seal: i=1; a=rsa-sha256; t=1653506802; cv=none; d=forwardemail.net;\r\n s=default;\r\n b=R6QJ0tGwwjg2VPxiAlVIKxsg3jEPtRGKPTIOdZNWuhWrbssttFdOYzRRqvacDyN5SLoyDhVye\r\n DUA/64IxANXdHVFlpR258Yp7WxLDv2gtJD5vNSKYmUJZOWk1TynmlqTYrp0Vuqg2xIUjIlPBWAJ\r\n PPNx4JvOLjJuWYynU2qIWz0=\r\nARC-Message-Signature: i=1; a=rsa-sha256; c=relaxed/relaxed;\r\n d=forwardemail.net; h=MIME-Version: Date: Message-ID: From: Content-Type;\r\n q=dns/txt; s=default; t=1653506802;\r\n bh=cEYDoyTy+Ub29XZt/zXR+sprfUE6BW0y5cHfah01PT4=;\r\n b=F/t56AAXr2Kv3G6VsbdT5OKDVJf2ulhwLiTM18Ra4tDPUKPSGSLKrWvxiXEg5NMWwdWnsOYrL\r\n r3YSm4uMxVMhHZbHm/sUu4QZq5/18hQsAkCv6fI9ifTjDwBrN5zpLOhPoZFFo+TyvHxiII3Xv3L\r\n UEzmUIIaJRX6tboQ160tino=\r\nARC-Authentication-Results: i=1; mx1.forwardemail.net;\r\n dkim=none (message not signed);\r\n spf=none (mx1.forwardemail.net: example.net does not designate permitted sender hosts) smtp.mailfrom=test@example.net smtp.helo=user.oem.local;\r\n dmarc=none header.from=example.com;\r\n bimi=skipped (DMARC not enabled)\r\nReceived-SPF: none (mx1.forwardemail.net: example.net does not designate permitted sender hosts) client-ip=127.0.0.1;\r\nAuthentication-Results: mx1.forwardemail.net;\r\n dkim=none (message not signed);\r\n spf=none (mx1.forwardemail.net: example.net does not designate permitted sender hosts) smtp.mailfrom=test@example.net smtp.helo=user.oem.local;\r\n dmarc=none header.from=example.com;\r\n bimi=skipped (DMARC not enabled)\r\n",
"headerLines": [
{
"key": "arc-seal",
"line": "ARC-Seal: i=1; a=rsa-sha256; t=1653506802; cv=none; d=forwardemail.net;\r\n s=default;\r\n b=R6QJ0tGwwjg2VPxiAlVIKxsg3jEPtRGKPTIOdZNWuhWrbssttFdOYzRRqvacDyN5SLoyDhVye\r\n DUA/64IxANXdHVFlpR258Yp7WxLDv2gtJD5vNSKYmUJZOWk1TynmlqTYrp0Vuqg2xIUjIlPBWAJ\r\n PPNx4JvOLjJuWYynU2qIWz0="
},
{
"key": "arc-message-signature",
"line": "ARC-Message-Signature: i=1; a=rsa-sha256; c=relaxed/relaxed;\r\n d=forwardemail.net; h=MIME-Version: Date: Message-ID: From: Content-Type;\r\n q=dns/txt; s=default; t=1653506802;\r\n bh=cEYDoyTy+Ub29XZt/zXR+sprfUE6BW0y5cHfah01PT4=;\r\n b=F/t56AAXr2Kv3G6VsbdT5OKDVJf2ulhwLiTM18Ra4tDPUKPSGSLKrWvxiXEg5NMWwdWnsOYrL\r\n r3YSm4uMxVMhHZbHm/sUu4QZq5/18hQsAkCv6fI9ifTjDwBrN5zpLOhPoZFFo+TyvHxiII3Xv3L\r\n UEzmUIIaJRX6tboQ160tino="
},
{
"key": "arc-authentication-results",
"line": "ARC-Authentication-Results: i=1; mx1.forwardemail.net;\r\n dkim=none (message not signed);\r\n spf=none (mx1.forwardemail.net: example.net does not designate permitted sender hosts) smtp.mailfrom=test@example.net smtp.helo=user.oem.local;\r\n dmarc=none header.from=example.com;\r\n bimi=skipped (DMARC not enabled)"
},
{
"key": "received-spf",
"line": "Received-SPF: none (mx1.forwardemail.net: example.net does not designate permitted sender hosts) client-ip=127.0.0.1;"
},
{
"key": "authentication-results",
"line": "Authentication-Results: mx1.forwardemail.net;\r\n dkim=none (message not signed);\r\n spf=none (mx1.forwardemail.net: example.net does not designate permitted sender hosts) smtp.mailfrom=test@example.net smtp.helo=user.oem.local;\r\n dmarc=none header.from=example.com;\r\n bimi=skipped (DMARC not enabled)"
},
{
"key": "x-forward-email-sender",
"line": "X-Forward-Email-Sender: rfc822; test@example.net"
},
{
"key": "x-forward-email-session-id",
"line": "X-Forward-Email-Session-ID: w2czxgznghn5ryyw"
},
{
"key": "x-forward-email-version",
"line": "X-Forward-Email-Version: 9.0.0"
},
{
"key": "content-type",
"line": "Content-Type: multipart/mixed; boundary=\"--_NmP-179a735428ca7575-Part_1\""
},
{
"key": "from",
"line": "From: some <random@example.com>"
},
{
"key": "message-id",
"line": "Message-ID: <69ad5fc2-91cb-728f-ae5c-eeedc5f267b6@example.net>"
},
{
"key": "date",
"line": "Date: Wed, 25 May 2022 19:26:41 +0000"
},
{
"key": "mime-version",
"line": "MIME-Version: 1.0"
}
],
"html": "<strong>some random text</strong>",
"text": "some random text",
"textAsHtml": "<p>some random text</p>",
"date": "2022-05-25T19:26:41.000Z",
"from": {
"value": [
{
"address": "random@example.com",
"name": "some"
}
],
"html": "<span class=\"mp_address_group\"><span class=\"mp_address_name\">some</span> <<a href=\"mailto:random@example.com\" class=\"mp_address_email\">random@example.com</a>></span>",
"text": "some <random@example.com>"
},
"messageId": "<69ad5fc2-91cb-728f-ae5c-eeedc5f267b6@example.net>",
"raw": "ARC-Seal: i=1; a=rsa-sha256; t=1653506802; cv=none; d=forwardemail.net;\r\n s=default;\r\n b=R6QJ0tGwwjg2VPxiAlVIKxsg3jEPtRGKPTIOdZNWuhWrbssttFdOYzRRqvacDyN5SLoyDhVye\r\n DUA/64IxANXdHVFlpR258Yp7WxLDv2gtJD5vNSKYmUJZOWk1TynmlqTYrp0Vuqg2xIUjIlPBWAJ\r\n PPNx4JvOLjJuWYynU2qIWz0=\r\nARC-Message-Signature: i=1; a=rsa-sha256; c=relaxed/relaxed;\r\n d=forwardemail.net; h=MIME-Version: Date: Message-ID: From: Content-Type;\r\n q=dns/txt; s=default; t=1653506802;\r\n bh=cEYDoyTy+Ub29XZt/zXR+sprfUE6BW0y5cHfah01PT4=;\r\n b=F/t56AAXr2Kv3G6VsbdT5OKDVJf2ulhwLiTM18Ra4tDPUKPSGSLKrWvxiXEg5NMWwdWnsOYrL\r\n r3YSm4uMxVMhHZbHm/sUu4QZq5/18hQsAkCv6fI9ifTjDwBrN5zpLOhPoZFFo+TyvHxiII3Xv3L\r\n UEzmUIIaJRX6tboQ160tino=\r\nARC-Authentication-Results: i=1; mx1.forwardemail.net;\r\n dkim=none (message not signed);\r\n spf=none (mx1.forwardemail.net: example.net does not designate permitted sender hosts) smtp.mailfrom=test@example.net smtp.helo=user.oem.local;\r\n dmarc=none header.from=example.com;\r\n bimi=skipped (DMARC not enabled)\r\nReceived-SPF: none (mx1.forwardemail.net: example.net does not designate permitted sender hosts) client-ip=127.0.0.1;\r\nAuthentication-Results: mx1.forwardemail.net;\r\n dkim=none (message not signed);\r\n spf=none (mx1.forwardemail.net: example.net does not designate permitted sender hosts) smtp.mailfrom=test@example.net smtp.helo=user.oem.local;\r\n dmarc=none header.from=example.com;\r\n bimi=skipped (DMARC not enabled)\r\nX-Forward-Email-Sender: rfc822; test@example.net\r\nX-Forward-Email-Session-ID: w2czxgznghn5ryyw\r\nX-Forward-Email-Version: 9.0.0\r\nContent-Type: multipart/mixed; boundary=\"--_NmP-179a735428ca7575-Part_1\"\r\nFrom: some <random@example.com>\r\nMessage-ID: <69ad5fc2-91cb-728f-ae5c-eeedc5f267b6@example.net>\r\nDate: Wed, 25 May 2022 19:26:41 +0000\r\nMIME-Version: 1.0\r\n\r\n----_NmP-179a735428ca7575-Part_1\r\nContent-Type: multipart/alternative;\r\n boundary=\"--_NmP-179a735428ca7575-Part_2\"\r\n\r\n----_NmP-179a735428ca7575-Part_2\r\nContent-Type: text/plain; charset=utf-8\r\nContent-Transfer-Encoding: 7bit\r\n\r\nsome random text\r\n----_NmP-179a735428ca7575-Part_2\r\nContent-Type: text/html; charset=utf-8\r\nContent-Transfer-Encoding: 7bit\r\n\r\n<strong>some random text</strong>\r\n----_NmP-179a735428ca7575-Part_2--\r\n\r\n----_NmP-179a735428ca7575-Part_1\r\nContent-Type: text/plain; name=text1.txt\r\nContent-Transfer-Encoding: base64\r\nContent-Disposition: attachment; filename=text1.txt\r\n\r\naGVsbG8gd29ybGQh\r\n----_NmP-179a735428ca7575-Part_1--\r\n",
"dkim": {
"headerFrom": [
"random@example.com"
],
"envelopeFrom": "test@example.net",
"results": [
{
"status": {
"result": "none",
"comment": "message not signed"
},
"info": "dkim=none (message not signed)"
}
]
},
"spf": {
"domain": "example.net",
"client-ip": "127.0.0.1",
"helo": "user.oem.local",
"envelope-from": "test@example.net",
"status": {
"result": "none",
"comment": "mx1.forwardemail.net: example.net does not designate permitted sender hosts",
"smtp": {
"mailfrom": "test@example.net",
"helo": "user.oem.local"
}
},
"header": "Received-SPF: none (mx1.forwardemail.net: example.net does not designate permitted sender hosts) client-ip=127.0.0.1;",
"info": "spf=none (mx1.forwardemail.net: example.net does not designate permitted sender hosts) smtp.mailfrom=test@example.net smtp.helo=user.oem.local",
"lookups": {
"limit": 50,
"count": 1
}
},
"arc": {
"status": {
"result": "none"
},
"i": 0,
"authResults": "mx1.forwardemail.net;\r\n dkim=none (message not signed);\r\n spf=none (mx1.forwardemail.net: example.net does not designate permitted sender hosts) smtp.mailfrom=test@example.net smtp.helo=user.oem.local;\r\n dmarc=none header.from=example.com;\r\n bimi=skipped (DMARC not enabled)"
},
"dmarc": {
"status": {
"result": "none",
"header": {
"from": "example.com"
}
},
"domain": "example.com",
"info": "dmarc=none header.from=example.com"
},
"bimi": {
"status": {
"header": {},
"result": "skipped",
"comment": "DMARC not enabled"
},
"info": "bimi=skipped (DMARC not enabled)"
},
"recipients": [
"webhook1@webhooks.net"
],
"session": {
"recipient": "webhook1@webhooks.net",
"remoteAddress": "127.0.0.1",
"remotePort": 65138,
"clientHostname": "[127.0.0.1]",
"hostNameAppearsAs": "user.oem.local",
"sender": "test@example.net",
"mta": "mx1.forwardemail.net",
"arrivalDate": "2022-05-25T19:26:41.423Z",
"arrivalTime": 1653506801423
}
}
Você suporta expressões regulares ou regex
Sim, a partir de 27 de setembro de 2021 adicionamos esse recurso. Você pode simplesmente escrever expressões regulares ("regex") para corresponder aliases e realizar substituições.
Aliases suportados por expressões regulares são aqueles que começam com / e terminam com / e seus destinatários são endereços de e-mail ou webhooks. Os destinatários também podem incluir suporte a substituição regex (ex.: $1, $2).
Suportamos duas flags de expressões regulares, incluindo i e g. A flag case-insensitive i é um padrão permanente e sempre aplicada. A flag global g pode ser adicionada por você ao acrescentar /g ao final da expressão.
Observe que também suportamos nosso recurso de alias desabilitado para a parte do destinatário com nosso suporte a regex.
Expressões regulares não são suportadas em domínios vanity globais (pois isso poderia ser uma vulnerabilidade de segurança).
Exemplos para Proteção Avançada de Privacidade
| Nome do Alias | Efeito | Teste |
|---|---|---|
/^(linus|torvalds)$/ |
E-mails para `linus@example.com` ou `torvalds@example.com` | (ver teste no RegExr) |
/^24highst(reet)$/ |
E-mails para `24highst@example.com` ou `24highstreet@example.com` | (ver teste no RegExr) |
Exemplos para o plano gratuito
Se você está no plano gratuito, basta adicionar um novo registro DNS TXT usando um ou mais dos exemplos fornecidos abaixo:
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou vazio | 3600 | TXT | forward-email=/^(linus|torvalds)$/:user@gmail.com |
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=/^([A-Za-z]+)+\.([A-Za-z]+)+$/:$1.$2@company.com |
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=/^(support|info)$/:user+$1@gmail.com |
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=/^(.*?)$/:https://example.com/webhook?username=$1 |
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=/^(linus|torvalds)$/:! |
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=/^(linus|torvalds)$/:!! |
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=/^(linus|torvalds)$/:!!! |
Quais são os seus limites de SMTP de saída
Limitamos usuários e domínios a 300 mensagens SMTP de saída por 1 dia. Isso equivale a uma média de mais de 9000 e-mails em um mês calendário. Se você precisar exceder essa quantidade ou tiver e-mails consistentemente grandes, por favor entre em contato conosco.
Preciso de aprovação para ativar o SMTP
Sim, por favor, note que para manter a reputação do IP e garantir a entregabilidade, o Forward Email possui um processo de revisão manual por domínio para aprovação do SMTP de saída. Envie um e-mail para support@forwardemail.net ou abra uma solicitação de ajuda para aprovação. Isso normalmente leva menos de 24 horas, com a maioria dos pedidos sendo atendidos em 1-2 horas. Em breve, pretendemos tornar esse processo instantâneo com controles adicionais de spam e alertas. Esse processo garante que seus e-mails cheguem à caixa de entrada e que suas mensagens não sejam marcadas como spam.
Quais são as configurações do seu servidor SMTP
Nosso servidor é smtp.forwardemail.net e também é monitorado em nossa página de status.
Ele suporta tanto IPv4 quanto IPv6 e está disponível nas portas 465 e 2465 para SSL/TLS (recomendado) e 587, 2587, 2525 e 25 para TLS (STARTTLS).
A partir de outubro de 2025, agora suportamos conexões TLS 1.0 legadas nas portas 2455 (SSL/TLS) e 2555 (STARTTLS) para dispositivos mais antigos, como impressoras, scanners, câmeras e clientes de e-mail legados que não suportam versões modernas do TLS. Essas portas são fornecidas como alternativa ao Gmail, Yahoo, Outlook e outros provedores que descontinuaram o suporte para protocolos TLS mais antigos.
Caution
Suporte TLS 1.0 Legado (Portas 2455 e 2555): Essas portas usam o protocolo TLS 1.0 obsoleto, que possui vulnerabilidades de segurança conhecidas (BEAST, POODLE). Use essas portas somente se seu dispositivo absolutamente não puder suportar TLS 1.2 ou superior. Recomendamos fortemente atualizar o firmware do seu dispositivo ou mudar para clientes de e-mail modernos sempre que possível. Essas portas destinam-se exclusivamente à compatibilidade com hardware legado (impressoras antigas, scanners, câmeras, dispositivos IoT).
| Protocolo | Nome do Host | Portas | IPv4 | IPv6 | Notas |
|---|---|---|---|---|---|
SSL/TLS Preferido |
smtp.forwardemail.net |
465, 2465 |
✅ | ✅ | TLS 1.2+ moderno (Recomendado) |
TLS (STARTTLS) |
smtp.forwardemail.net |
587, 2587, 2525, 25 |
✅ | ✅ | Suportado (prefira a porta SSL/TLS 465) |
SSL/TLS Apenas Legado |
smtp.forwardemail.net |
2455 |
✅ | ✅ | ⚠️ TLS 1.0 apenas para dispositivos antigos |
TLS (STARTTLS) Apenas Legado |
smtp.forwardemail.net |
2555 |
✅ | ✅ | ⚠️ TLS 1.0 apenas para dispositivos antigos |
| Login | Exemplo | Descrição | |||
| -------- | ------------------------- | ----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | |||
| Username | user@example.com |
Endereço de email de um alias que existe para o domínio em Minha Conta Domínios. | |||
| Password | ************************ |
Alias |
Para enviar email de saída com SMTP, o usuário SMTP deve ser o endereço de email de um alias que existe para o domínio em Minha Conta Domínios – e a senha SMTP deve ser uma senha gerada específica para o alias.
Por favor, consulte Vocês suportam o envio de email com SMTP para instruções passo a passo.
Quais são as configurações do seu servidor IMAP
Nosso servidor é imap.forwardemail.net e também é monitorado em nossa página de status.
Ele suporta tanto IPv4 quanto IPv6 e está disponível nas portas 993 e 2993 para SSL/TLS.
| Protocolo | Nome do Host | Portas | IPv4 | IPv6 |
|---|---|---|---|---|
SSL/TLS Preferido |
imap.forwardemail.net |
993, 2993 |
✅ | ✅ |
| Login | Exemplo | Descrição |
|---|---|---|
| Username | user@example.com |
Endereço de email de um alias que existe para o domínio em Minha Conta Domínios. |
| Password | ************************ |
Senha gerada específica para o alias. |
Para conectar-se via IMAP, o usuário IMAP deve ser o endereço de email de um alias que existe para o domínio em Minha Conta Domínios – e a senha IMAP deve ser uma senha gerada específica para o alias.
Por favor, consulte Vocês suportam o recebimento de email com IMAP para instruções passo a passo.
Quais são as configurações do seu servidor POP3
Nosso servidor é pop3.forwardemail.net e também é monitorado em nossa página de status.
Ele suporta tanto IPv4 quanto IPv6 e está disponível nas portas 995 e 2995 para SSL/TLS.
| Protocolo | Nome do Host | Portas | IPv4 | IPv6 |
|---|---|---|---|---|
SSL/TLS Preferido |
pop3.forwardemail.net |
995, 2995 |
✅ | ✅ |
| Login | Exemplo | Descrição | ||
| -------- | ------------------------- | ----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | ||
| Username | user@example.com |
Endereço de email de um alias que existe para o domínio em Minha Conta Domínios. | ||
| Password | ************************ |
Senha gerada específica para o alias. |
Para conectar com POP3, o usuário POP3 deve ser o endereço de email de um alias que existe para o domínio em Minha Conta Domínios – e a senha IMAP deve ser uma senha gerada específica para o alias.
Por favor, consulte Você suporta POP3 para instruções passo a passo.
Como configurar a autodetecção de email para meu domínio
A autodetecção de email permite que clientes de email como Thunderbird, Apple Mail, Microsoft Outlook e dispositivos móveis detectem automaticamente as configurações corretas dos servidores IMAP, SMTP, POP3, CalDAV e CardDAV quando um usuário adiciona sua conta de email. Isso é definido pelo RFC 6186 (email) e RFC 6764 (CalDAV/CardDAV) e utiliza registros DNS SRV.
Forward Email publica registros de autodetecção em forwardemail.net. Você pode adicionar registros SRV diretamente ao seu domínio ou usar uma abordagem mais simples com CNAME.
Opção A: registros CNAME (mais simples)
Adicione estes dois registros CNAME ao DNS do seu domínio. Isso delega a autodetecção aos servidores do Forward Email:
| Tipo | Nome/Host | Destino/Valor |
|---|---|---|
| CNAME | autoconfig |
autoconfig.forwardemail.net |
| CNAME | autodiscover |
autodiscover.forwardemail.net |
O registro autoconfig é usado pelo Thunderbird e outros clientes baseados em Mozilla. O registro autodiscover é usado pelo Microsoft Outlook.
Opção B: registros SRV (direto)
Se preferir adicionar os registros diretamente (ou se seu provedor DNS não suportar CNAME em subdomínios), adicione estes registros SRV ao seu domínio:
| Tipo | Nome/Host | Prioridade | Peso | Porta | Destino/Valor | Propósito |
|---|---|---|---|---|---|---|
| SRV | _imaps._tcp |
0 | 1 | 993 | imap.forwardemail.net |
IMAP sobre SSL/TLS (preferido) |
| SRV | _imap._tcp |
0 | 0 | 0 | . |
IMAP em texto simples desativado |
| SRV | _submissions._tcp |
0 | 1 | 465 | smtp.forwardemail.net |
Envio SMTP (SSL/TLS, recomendado) |
| SRV | _submission._tcp |
5 | 1 | 587 | smtp.forwardemail.net |
Envio SMTP (STARTTLS) |
| SRV | _pop3s._tcp |
10 | 1 | 995 | pop3.forwardemail.net |
POP3 sobre SSL/TLS |
| SRV | _pop3._tcp |
0 | 0 | 0 | . |
POP3 em texto simples desativado |
| SRV | _caldavs._tcp |
0 | 1 | 443 | caldav.forwardemail.net |
CalDAV sobre TLS (calendários) |
| SRV | _caldav._tcp |
0 | 0 | 0 | . |
CalDAV em texto simples desativado |
| SRV | _carddavs._tcp |
0 | 1 | 443 | carddav.forwardemail.net |
CardDAV sobre TLS (contatos) |
| SRV | _carddav._tcp |
0 | 0 | 0 | . |
CardDAV em texto simples desativado |
Note
IMAP tem um valor de prioridade menor (0) que POP3 (10), o que indica aos clientes de email para preferirem IMAP em vez de POP3 quando ambos estão disponíveis. Os registros com um destino de . (um único ponto) indicam que as versões em texto simples (não criptografadas) desses protocolos estão intencionalmente desativadas conforme RFC 6186 Seção 3.4. Os registros SRV CalDAV e CardDAV seguem RFC 6764 para autodiscovery de calendário e contatos.
Quais clientes de email suportam autodiscovery?
| Cliente | CalDAV/CardDAV | |
|---|---|---|
| Thunderbird | registros CNAME ou SRV autoconfig |
registros XML ou SRV autoconfig (RFC 6764) |
| Apple Mail (macOS) | registros SRV (RFC 6186) | registros SRV (RFC 6764) |
| Apple Mail (iOS) | registros SRV (RFC 6186) | registros SRV (RFC 6764) |
| Microsoft Outlook | CNAME autodiscover ou SRV _autodiscover._tcp |
Não suportado |
| GNOME (Evolution) | registros SRV (RFC 6186) | registros SRV (RFC 6764) |
| KDE (KMail) | registros SRV (RFC 6186) | registros SRV (RFC 6764) |
| eM Client | autoconfig ou autodiscover |
registros SRV (RFC 6764) |
Tip
Para a melhor compatibilidade entre todos os clientes, recomendamos usar a Opção A (registros CNAME) combinada com os registros SRV da Opção B. A abordagem CNAME sozinha cobre a maioria dos clientes de email. Os registros SRV CalDAV/CardDAV garantem que clientes de calendário e contatos também possam descobrir automaticamente as configurações do seu servidor.
Segurança
Técnicas Avançadas de Fortalecimento de Servidor
Tip
Saiba mais sobre nossa infraestrutura de segurança em nossa página de Segurança.
Forward Email implementa inúmeras técnicas de fortalecimento de servidor para garantir a segurança da nossa infraestrutura e dos seus dados:
-
Segurança de Rede:
- Firewall com regras rigorosas usando IP tables
- Fail2ban para proteção contra força bruta
- Auditorias regulares de segurança e testes de penetração
- Acesso administrativo somente via VPN
-
Fortalecimento do Sistema:
- Instalação mínima de pacotes
- Atualizações regulares de segurança
- SELinux em modo enforcing
- Acesso root via SSH desabilitado
- Autenticação somente por chave
-
Segurança da Aplicação:
- Cabeçalhos Content Security Policy (CSP)
- HTTPS Strict Transport Security (HSTS)
- Cabeçalhos de proteção contra XSS
- Cabeçalhos de opções de frame e política de referenciador
- Auditorias regulares de dependências
-
Proteção de Dados:
- Criptografia completa do disco com LUKS
- Gerenciamento seguro de chaves
- Backups regulares com criptografia
- Práticas de minimização de dados
-
Monitoramento e Resposta:
- Detecção de intrusão em tempo real
- Escaneamento automático de segurança
- Registro e análise centralizados
- Procedimentos de resposta a incidentes
Important
Nossas práticas de segurança são continuamente atualizadas para enfrentar ameaças e vulnerabilidades emergentes.
Tip
Para máxima segurança, recomendamos usar nosso serviço com criptografia de ponta a ponta via OpenPGP.
Vocês possuem certificações SOC 2 ou ISO 27001
Note
Forward Email opera em infraestrutura fornecida por subprocessadores certificados para garantir conformidade com os padrões da indústria.
Forward Email não possui diretamente certificações SOC 2 Tipo II ou ISO 27001. No entanto, o serviço opera em infraestrutura fornecida por subprocessadores certificados:
-
DigitalOcean: certificado SOC 2 Tipo II e SOC 3 Tipo II (auditado pela Schellman & Company LLC), certificado ISO 27001 em múltiplos data centers. Detalhes: https://www.digitalocean.com/trust/certification-reports
-
Vultr: certificado SOC 2+ (HIPAA), certificações ISO/IEC: 20000-1:2018, 27001:2022, 27017:2015, 27018:2019. Detalhes: https://www.vultr.com/legal/compliance/
-
DataPacket: compatível com SOC 2 (contate diretamente a DataPacket para obter a certificação), provedor de infraestrutura de nível empresarial (localização em Denver). Detalhes: https://www.datapacket.com/datacenters/denver
Forward Email segue as melhores práticas do setor para auditorias de segurança e se envolve regularmente com pesquisadores independentes de segurança. Fonte: https://forwardemail.net/technical-whitepaper.pdf#page=36
Você usa criptografia TLS para encaminhamento de e-mail
Sim. O Forward Email aplica rigorosamente TLS 1.2+ para todas as conexões (HTTPS, SMTP, IMAP, POP3) e implementa MTA-STS para suporte aprimorado ao TLS. A implementação inclui:
- Aplicação de TLS 1.2+ para todas as conexões de e-mail
- Troca de chaves ECDHE (Elliptic Curve Diffie-Hellman Ephemeral) para segredo perfeito à frente
- Suites de cifra modernas com atualizações regulares de segurança
- Suporte a HTTP/2 para melhor desempenho e segurança
- HSTS (HTTP Strict Transport Security) com pré-carregamento nos principais navegadores
- MTA-STS (Mail Transfer Agent Strict Transport Security) para aplicação rigorosa do TLS
Fonte: https://forwardemail.net/technical-whitepaper.pdf#page=25
Implementação do MTA-STS: O Forward Email implementa aplicação rigorosa do MTA-STS no código-fonte. Quando ocorrem erros TLS e o MTA-STS está aplicado, o sistema retorna códigos de status SMTP 421 para garantir que os e-mails sejam reenviados posteriormente em vez de serem entregues de forma insegura. Detalhes da implementação:
- Detecção de erro TLS: https://github.com/forwardemail/forwardemail.net/blob/master/helpers/is-tls-error.js
- Aplicação do MTA-STS no helper send-email: https://github.com/forwardemail/forwardemail.net/blob/master/helpers/send-email.js
Validação por terceiros: https://www.hardenize.com/report/forwardemail.net/1750312779 mostra classificações "Good" para todas as medidas de TLS e segurança de transporte.
Você preserva os cabeçalhos de autenticação de e-mail
Sim. O Forward Email implementa e preserva de forma abrangente os cabeçalhos de autenticação de e-mail:
- SPF (Sender Policy Framework): Implementado e preservado corretamente
- DKIM (DomainKeys Identified Mail): Suporte completo com gerenciamento adequado de chaves
- DMARC: Aplicação de política para e-mails que falham na validação SPF ou DKIM
- ARC: Embora não detalhado explicitamente, as pontuações perfeitas de conformidade do serviço sugerem um tratamento abrangente dos cabeçalhos de autenticação
Fonte: https://forwardemail.net/technical-whitepaper.pdf#page=31
Validação: O teste de e-mail do Internet.nl mostra pontuação 100/100 especificamente para a implementação de "SPF, DKIM e DMARC". A avaliação Hardenize confirma classificações "Good" para SPF e DMARC: https://www.hardenize.com/report/forwardemail.net/1750312779
Você preserva os cabeçalhos originais do e-mail e previne falsificação
Tip
O Forward Email implementa proteção sofisticada contra falsificação para prevenir abuso de e-mail.
O Forward Email preserva os cabeçalhos originais do e-mail enquanto implementa proteção abrangente contra falsificação através do código-fonte MX:
- Preservação de Cabeçalhos: Os cabeçalhos originais de autenticação são mantidos durante o encaminhamento
- Proteção contra Falsificação: Aplicação da política DMARC impede falsificação de cabeçalhos rejeitando e-mails que falham na validação SPF ou DKIM
- Prevenção de Injeção de Cabeçalhos: Validação e sanitização de entrada usando a biblioteca striptags
- Proteção Avançada: Detecção sofisticada de phishing com detecção de falsificação, prevenção de personificação e sistemas de notificação ao usuário
Detalhes da Implementação MX: A lógica principal de processamento de e-mail é tratada pelo código do servidor MX, especificamente:
- Manipulador principal de dados MX: https://github.com/forwardemail/forwardemail.net/blob/master/helpers/on-data-mx.js
- Filtragem arbitrária de e-mails (anti-falsificação): https://github.com/forwardemail/forwardemail.net/blob/master/helpers/is-arbitrary.js
O helper isArbitrary implementa regras sofisticadas anti-falsificação incluindo detecção de personificação de domínio, frases bloqueadas e vários padrões de phishing.
Como você se protege contra spam e abuso
Forward Email implementa uma proteção abrangente em múltiplas camadas:
- Limitação de Taxa: Aplicada a tentativas de autenticação, endpoints de API e conexões SMTP
- Isolamento de Recursos: Entre usuários para evitar impacto de usuários com alto volume
- Proteção contra DDoS: Proteção em múltiplas camadas através do sistema Shield da DataPacket e Cloudflare
- Escalonamento Automático: Ajuste dinâmico de recursos baseado na demanda
- Prevenção de Abuso: Verificações específicas para prevenção de abuso por usuário e bloqueio baseado em hash para conteúdo malicioso
- Autenticação de Email: Protocolos SPF, DKIM, DMARC com detecção avançada de phishing
Fontes:
- https://forwardemail.net/technical-whitepaper.pdf#page=18
- https://www.datapacket.com/datacenters/denver (detalhes da proteção contra DDoS)
- https://github.com/forwardemail/forwardemail.net/blob/master/helpers/abuse-prevention-by-user-id.js
Você armazena o conteúdo do email no disco
Important
Forward Email usa uma arquitetura de conhecimento zero que impede que o conteúdo do email seja gravado no disco.
- Arquitetura de Conhecimento Zero: Caixas de correio SQLite criptografadas individualmente significam que o Forward Email não pode acessar o conteúdo do email
- Processamento em Memória: O processamento do email ocorre inteiramente na memória, evitando armazenamento em disco
- Sem Registro de Conteúdo: "Nós não registramos nem armazenamos conteúdo ou metadados de email no disco"
- Criptografia em Sandbox: As chaves de criptografia nunca são armazenadas no disco em texto simples
Evidência no Código MX: O servidor MX processa emails inteiramente na memória sem gravar conteúdo no disco. O manipulador principal de processamento de email demonstra essa abordagem em memória: https://github.com/forwardemail/forwardemail.net/blob/master/helpers/on-data-mx.js
Fontes:
- https://forwardemail.net/technical-whitepaper.pdf#page=10 (Resumo)
- https://forwardemail.net/technical-whitepaper.pdf#page=59 (Detalhes sobre conhecimento zero)
- https://forwardemail.net/technical-whitepaper.pdf#page=21 (Criptografia em sandbox)
O conteúdo do email pode ser exposto durante falhas do sistema
Não. Forward Email implementa salvaguardas abrangentes contra exposição de dados relacionada a falhas:
- Core Dumps Desativados: Evita exposição de memória durante falhas
- Memória Swap Desativada: Completamente desativada para evitar extração de dados sensíveis de arquivos de swap
- Arquitetura em Memória: O conteúdo do email existe apenas na memória volátil durante o processamento
- Proteção das Chaves de Criptografia: As chaves nunca são armazenadas no disco em texto simples
- Segurança Física: Discos criptografados com LUKS v2 impedem acesso físico aos dados
- Armazenamento USB Desativado: Impede extração não autorizada de dados
Tratamento de Erros para Problemas do Sistema: Forward Email usa funções auxiliares isCodeBug e isTimeoutError para garantir que, se ocorrerem problemas de conectividade com banco de dados, problemas de rede/DNS/lista negra ou problemas de conectividade upstream, o sistema retorne códigos SMTP 421 para garantir que os emails sejam reenviados posteriormente em vez de serem perdidos ou expostos.
Detalhes da implementação:
- Classificação de erros: https://github.com/forwardemail/forwardemail.net/blob/master/helpers/is-code-bug.js
- Tratamento de erro de timeout no processamento MX: https://github.com/forwardemail/forwardemail.net/blob/master/helpers/on-data-mx.js
Fonte: https://forwardemail.net/technical-whitepaper.pdf#page=15
Quem tem acesso à sua infraestrutura de email
Forward Email implementa controles de acesso abrangentes para sua equipe mínima de engenharia de 2-3 pessoas com requisitos rigorosos de 2FA:
-
Controle de Acesso Baseado em Função: Para contas da equipe com permissões baseadas em recursos
-
Princípio do Menor Privilégio: Aplicado em todos os sistemas
-
Segregação de Funções: Entre papéis operacionais
-
Gerenciamento de Usuários: Usuários separados para deploy e devops com permissões distintas
-
Login Root Desativado: Obriga acesso através de contas devidamente autenticadas
-
2FA Rigoroso: Sem 2FA via SMS devido ao risco de ataques MiTM - apenas tokens baseados em app ou hardware
-
Registro Abrangente de Auditoria: Com redação de dados sensíveis
-
Detecção Automática de Anomalias: Para padrões de acesso incomuns
-
Revisões Regulares de Segurança: Dos logs de acesso
-
Prevenção contra Ataques Evil Maid: Armazenamento USB desativado e outras medidas de segurança física Fontes:
-
https://forwardemail.net/technical-whitepaper.pdf#page=30 (Controles de Autorização)
-
https://forwardemail.net/technical-whitepaper.pdf#page=30 (Segurança de Rede)
-
https://forwardemail.net/technical-whitepaper.pdf#page=15 (Prevenção contra ataque evil maid)
Quais provedores de infraestrutura você utiliza
Important
Forward Email utiliza múltiplos subprocessadores de infraestrutura com certificações abrangentes de conformidade.
Detalhes completos estão disponíveis em nossa página de conformidade com o GDPR: https://forwardemail.net/gdpr
Principais Subprocessadores de Infraestrutura:
| Provedor | Certificado no Framework de Privacidade de Dados | Página de Conformidade com GDPR |
|---|---|---|
| Cloudflare | ✅ Sim | https://www.cloudflare.com/trust-hub/gdpr/ |
| DataPacket | ❌ Não | https://www.datapacket.com/privacy-policy |
| DigitalOcean | ❌ Não | https://www.digitalocean.com/legal/gdpr |
| GitHub | ✅ Sim | https://docs.github.com/en/site-policy/privacy-policies/github-data-protection-agreement |
| Vultr | ❌ Não | https://www.vultr.com/legal/eea-gdpr-privacy/ |
Certificações Detalhadas:
DigitalOcean
- SOC 2 Tipo II & SOC 3 Tipo II (auditado pela Schellman & Company LLC)
- ISO 27001 certificado em múltiplos data centers
- Compatível com PCI-DSS
- Certificado CSA STAR Nível 1
- Certificado APEC CBPR PRP
- Detalhes: https://www.digitalocean.com/trust/certification-reports
Vultr
- Certificado SOC 2+ (HIPAA)
- Compatível com PCI Merchant
- Certificado CSA STAR Nível 1
- ISO/IEC 20000-1:2018, 27001:2022, 27017:2015, 27018:2019
- Detalhes: https://www.vultr.com/legal/compliance/
DataPacket
- Compatível com SOC 2 (contate diretamente a DataPacket para obter certificação)
- Infraestrutura de nível empresarial (localização em Denver)
- Proteção contra DDoS através da pilha de cibersegurança Shield
- Suporte técnico 24/7
- Rede global com 58 data centers
- Detalhes: https://www.datapacket.com/datacenters/denver
GitHub
- Certificado no Framework de Privacidade de Dados (EU-EUA, Suíça-EUA e Extensão do Reino Unido)
- Hospedagem de código-fonte, CI/CD e gerenciamento de projetos
- Acordo de Proteção de Dados do GitHub disponível
- Detalhes: https://docs.github.com/en/site-policy/privacy-policies/github-data-protection-agreement
Processadores de Pagamento:
- Stripe: Certificado no Framework de Privacidade de Dados - https://stripe.com/legal/privacy-center
- PayPal: Não certificado no DPF - https://www.paypal.com/uk/legalhub/privacy-full
Vocês oferecem um Acordo de Processamento de Dados (DPA)
Sim, o Forward Email oferece um Acordo de Processamento de Dados (DPA) abrangente que pode ser assinado junto com nosso contrato empresarial. Uma cópia do nosso DPA está disponível em: https://forwardemail.net/dpa
Detalhes do DPA:
- Cobre conformidade com GDPR e os frameworks EU-US/Swiss-US Privacy Shield
- Aceito automaticamente ao concordar com nossos Termos de Serviço
- Não requer assinatura separada para o DPA padrão
- Arranjos personalizados de DPA disponíveis através da Licença Empresarial
Framework de Conformidade com GDPR: Nosso DPA detalha a conformidade com o GDPR, bem como os requisitos internacionais para transferência de dados. Informações completas estão disponíveis em: https://forwardemail.net/gdpr
Para clientes empresariais que necessitam de termos personalizados no DPA ou acordos contratuais específicos, estes podem ser tratados através do nosso programa Licença Empresarial (US$250/mês).
Como vocês lidam com notificações de violação de dados
Note
A arquitetura zero-knowledge do Forward Email limita significativamente o impacto de violações.
- Exposição Limitada de Dados: Não pode acessar o conteúdo de e-mails criptografados devido à arquitetura de conhecimento zero
- Coleta Mínima de Dados: Apenas informações básicas do assinante e registros limitados de IP para segurança
- Estruturas de Subprocessadores: DigitalOcean, GitHub e Vultr mantêm procedimentos de resposta a incidentes em conformidade com o GDPR
Informações do Representante GDPR: Forward Email nomeou representantes GDPR em conformidade com o Artigo 27:
Representante da UE: Osano International Compliance Services Limited ATTN: LFHC 3 Dublin Landings, North Wall Quay Dublin 1, D01C4E0
Representante do Reino Unido: Osano UK Compliance LTD ATTN: LFHC 42-46 Fountain Street, Belfast Antrim, BT1 - 5EF
Para clientes empresariais que exigem SLAs específicos de notificação de violação, estes devem ser discutidos como parte de um acordo de Licença Empresarial.
Fontes:
Você oferece um ambiente de teste
A documentação técnica do Forward Email não descreve explicitamente um modo sandbox dedicado. No entanto, abordagens potenciais para testes incluem:
- Opção de Auto-Hospedagem: Capacidades abrangentes de auto-hospedagem para criação de ambientes de teste
- Interface API: Potencial para testes programáticos de configurações
- Código Aberto: Código 100% open-source permite que clientes examinem a lógica de encaminhamento
- Múltiplos Domínios: Suporte para múltiplos domínios pode possibilitar a criação de domínios de teste
Para clientes empresariais que exigem capacidades formais de sandbox, isso deve ser discutido como parte de um acordo de Licença Empresarial.
Fonte: https://github.com/forwardemail/forwardemail.net (Detalhes do ambiente de desenvolvimento)
Você fornece ferramentas de monitoramento e alerta
Forward Email oferece monitoramento em tempo real com algumas limitações:
Disponível:
- Monitoramento de Entrega em Tempo Real: Métricas de desempenho visíveis publicamente para os principais provedores de e-mail
- Alertas Automáticos: Equipe de engenharia alertada quando os tempos de entrega excedem 10 segundos
- Monitoramento Transparente: Sistemas de monitoramento 100% open-source
- Monitoramento de Infraestrutura: Detecção automática de anomalias e registro abrangente de auditoria
Limitações:
- Webhooks voltados para clientes ou notificações de status de entrega baseadas em API não são explicitamente documentados
Para clientes empresariais que exigem webhooks detalhados de status de entrega ou integrações personalizadas de monitoramento, essas capacidades podem estar disponíveis através de acordos de Licença Empresarial.
Fontes:
- https://forwardemail.net (Exibição de monitoramento em tempo real)
- https://github.com/forwardemail/forwardemail.net (Implementação do monitoramento)
Como você garante alta disponibilidade
Important
Forward Email implementa redundância abrangente através de múltiplos provedores de infraestrutura.
- Infraestrutura Distribuída: Múltiplos provedores (DigitalOcean, Vultr, DataPacket) em regiões geográficas
- Balanceamento de Carga Geográfico: Balanceamento de carga geolocalizado baseado em Cloudflare com failover automático
- Escalonamento Automático: Ajuste dinâmico de recursos baseado na demanda
- Proteção DDoS em Múltiplas Camadas: Através do sistema Shield da DataPacket e Cloudflare
- Redundância de Servidores: Múltiplos servidores por região com failover automático
- Replicação de Banco de Dados: Sincronização de dados em tempo real entre múltiplas localidades
- Monitoramento e Alertas: Monitoramento 24/7 com resposta automática a incidentes
Compromisso de Uptime: Disponibilidade do serviço superior a 99,9% com monitoramento transparente disponível em https://forwardemail.net
Fontes:
- https://forwardemail.net/technical-whitepaper.pdf#page=18
- https://www.datapacket.com/datacenters/denver
Você está em conformidade com a Seção 889 do National Defense Authorization Act (NDAA)
Important
Forward Email está totalmente em conformidade com a Seção 889 através da seleção cuidadosa de parceiros de infraestrutura.
Sim, o Forward Email está em conformidade com a Seção 889. A Seção 889 do National Defense Authorization Act (NDAA) proíbe agências governamentais de usar ou contratar entidades que utilizem equipamentos de telecomunicações e vigilância por vídeo de empresas específicas (Huawei, ZTE, Hikvision, Dahua e Hytera). Como o Forward Email Alcança a Conformidade com a Seção 889:
O Forward Email depende exclusivamente de dois provedores principais de infraestrutura, nenhum dos quais utiliza equipamentos proibidos pela Seção 889:
- Cloudflare: Nosso parceiro principal para serviços de rede e segurança de e-mail
- DataPacket: Nosso provedor principal para infraestrutura de servidores (utilizando exclusivamente equipamentos da Arista Networks e Cisco)
- Provedores de Backup: Nossos provedores de backup Digital Ocean e Vultr são adicionalmente confirmados por escrito como estando em conformidade com a Seção 889.
Compromisso da Cloudflare: A Cloudflare declara explicitamente em seu Código de Conduta para Terceiros que não utiliza equipamentos de telecomunicações, produtos de vigilância por vídeo ou serviços de quaisquer entidades proibidas pela Seção 889.
Caso de Uso Governamental: Nossa conformidade com a Seção 889 foi validada quando a US Naval Academy selecionou o Forward Email para suas necessidades de encaminhamento seguro de e-mails, exigindo documentação de nossos padrões de conformidade federal.
Para detalhes completos sobre nossa estrutura de conformidade governamental, incluindo regulamentações federais mais amplas, leia nosso estudo de caso abrangente: Serviço de Email do Governo Federal em Conformidade com a Seção 889
Detalhes do Sistema e Técnicos
Vocês armazenam e-mails e seus conteúdos
Não, não gravamos em disco nem armazenamos logs – com a exceção de erros e SMTP de saída (veja nossa Política de Privacidade).
Tudo é feito em memória e nosso código-fonte está no GitHub.
Como funciona o seu sistema de encaminhamento de e-mails
O e-mail depende do protocolo SMTP. Este protocolo consiste em comandos enviados a um servidor (geralmente rodando na porta 25). Há uma conexão inicial, depois o remetente indica de quem é o e-mail ("MAIL FROM"), seguido para quem ele está sendo enviado ("RCPT TO"), e finalmente os cabeçalhos e o corpo do e-mail em si ("DATA"). O fluxo do nosso sistema de encaminhamento de e-mails é descrito em relação a cada comando do protocolo SMTP abaixo:
-
Conexão Inicial (sem nome de comando, ex.
telnet example.com 25) - Esta é a conexão inicial. Verificamos remetentes que não estão em nossa lista de permissões contra nossa lista de bloqueios. Finalmente, se um remetente não estiver na lista de permissões, verificamos se ele foi colocado em lista cinza. -
HELO- Indica uma saudação para identificar o FQDN do remetente, endereço IP ou nome do manipulador de e-mail. Este valor pode ser falsificado, então não confiamos nesses dados e usamos a busca reversa do nome do host do endereço IP da conexão. -
MAIL FROM- Indica o endereço do remetente do envelope do e-mail. Se um valor for inserido, deve ser um endereço de e-mail válido conforme RFC 5322. Valores vazios são permitidos. Aqui verificamos backscatter e também verificamos o MAIL FROM contra nossa lista de bloqueios. Finalmente, verificamos remetentes que não estão na lista de permissões para limitação de taxa (veja a seção sobre Limitação de Taxa e lista de permissões para mais informações). -
RCPT TO- Indica o(s) destinatário(s) do e-mail. Devem ser endereços de e-mail válidos conforme RFC 5322. Permitimos até 50 destinatários no envelope por mensagem (isso é diferente do cabeçalho "Para" de um e-mail). Também verificamos um endereço válido do Sender Rewriting Scheme ("SRS") aqui para proteger contra falsificação com nosso nome de domínio SRS. -
DATA- Esta é a parte central do nosso serviço que processa um e-mail. Veja a seção Como vocês processam um e-mail para encaminhamento abaixo para mais detalhes.
Como você processa um email para encaminhamento
Esta seção descreve nosso processo relacionado ao comando do protocolo SMTP DATA na seção Como funciona seu sistema de encaminhamento de email acima – é como processamos os cabeçalhos, corpo, segurança do email, determinamos para onde ele precisa ser entregue e como lidamos com as conexões.
-
Se a mensagem exceder o tamanho máximo de 50mb, ela será rejeitada com um código de erro 552.
-
Se a mensagem não contiver um cabeçalho "From", ou se algum dos valores no cabeçalho "From" não for um endereço de email válido conforme RFC 5322, ela será rejeitada com um código de erro 550.
-
Se a mensagem tiver mais de 25 cabeçalhos "Received", será determinado que ela ficou presa em um loop de redirecionamento, e será rejeitada com um código de erro 550.
-
Usando a impressão digital do email (veja a seção sobre Fingerprinting), verificaremos se a mensagem foi tentada ser reenviada por mais de 5 dias (o que corresponde ao comportamento padrão do postfix), e se for o caso, ela será rejeitada com um código de erro 550.
-
Armazenamos em memória os resultados da varredura do email usando o Spam Scanner.
-
Se houver quaisquer resultados arbitrários do Spam Scanner, a mensagem será rejeitada com um código de erro 554. Resultados arbitrários incluem apenas o teste GTUBE no momento desta escrita. Veja https://spamassassin.apache.org/gtube/ para mais informações.
-
Adicionaremos os seguintes cabeçalhos à mensagem para fins de depuração e prevenção de abuso:
Received- adicionamos este cabeçalho padrão Received com IP e host de origem, tipo de transmissão, informações da conexão TLS, data/hora e destinatário.X-Original-To- o destinatário original da mensagem:- Isso é útil para determinar onde um email foi originalmente entregue (além do cabeçalho "Received").
- É adicionado por destinatário no momento do encaminhamento IMAP e/ou mascarado (para proteger a privacidade).
X-Forward-Email-Website- contém um link para nosso site https://forwardemail.netX-Forward-Email-Version- a versão atual SemVer dopackage.jsonda nossa base de código.X-Forward-Email-Session-ID- um valor de ID de sessão usado para fins de depuração (aplica-se apenas em ambientes não produtivos).X-Forward-Email-Sender- uma lista separada por vírgulas contendo o endereço original MAIL FROM do envelope (se não estiver em branco), o FQDN PTR reverso do cliente (se existir) e o endereço IP do remetente.X-Forward-Email-ID- aplicável apenas para SMTP de saída e correlaciona-se ao ID do email armazenado em Minha Conta → EmailsX-Report-Abuse- com o valorabuse@forwardemail.net.X-Report-Abuse-To- com o valorabuse@forwardemail.net.X-Complaints-To- com o valorabuse@forwardemail.net.
-
Em seguida, verificamos a mensagem para DKIM, SPF, ARC e DMARC.
- Se a mensagem falhar no DMARC e o domínio tiver uma política de rejeição (ex.:
p=rejectestava na política DMARC), ela será rejeitada com um código de erro 550. Normalmente, a política DMARC de um domínio pode ser encontrada no registro TXT do subdomínio_dmarc(ex.:dig _dmarc.example.com txt). - Se a mensagem falhar no SPF e o domínio tiver uma política de falha rígida (ex.:
-allestava na política SPF em vez de~allou nenhuma política), ela será rejeitada com um código de erro 550. Normalmente, a política SPF de um domínio pode ser encontrada no registro TXT do domínio raiz (ex.:dig example.com txt). Veja esta seção para mais informações sobre enviar email como no Gmail referente ao SPF.
- Se a mensagem falhar no DMARC e o domínio tiver uma política de rejeição (ex.:
-
Agora processamos os destinatários da mensagem conforme coletados a partir do comando
RCPT TOna seção Como funciona o seu sistema de encaminhamento de email acima. Para cada destinatário, realizamos as seguintes operações:- Consultamos os registros TXT do nome de domínio (a parte após o símbolo
@, por exemplo,example.comse o endereço de email fortest@example.com). Por exemplo, se o domínio forexample.com, fazemos uma consulta DNS comodig example.com txt. - Analisamos todos os registros TXT que começam com
forward-email=(planos gratuitos) ouforward-email-site-verification=(planos pagos). Note que analisamos ambos, para processar emails enquanto um usuário está atualizando ou rebaixando planos. - A partir desses registros TXT analisados, iteramos sobre eles para extrair a configuração de encaminhamento (conforme descrito na seção Como começar e configurar o encaminhamento de email acima). Note que suportamos apenas um valor
forward-email-site-verification=, e se mais de um for fornecido, ocorrerá um erro 550 e o remetente receberá um bounce para esse destinatário. - Recursivamente iteramos sobre a configuração de encaminhamento extraída para determinar o encaminhamento global, encaminhamento baseado em regex e todas as outras configurações de encaminhamento suportadas – que agora são conhecidas como nossos "Endereços de Encaminhamento".
- Para cada Endereço de Encaminhamento, suportamos uma consulta recursiva (que iniciará esta série de operações novamente para o endereço dado). Se uma correspondência recursiva for encontrada, o resultado pai será removido dos Endereços de Encaminhamento, e os filhos adicionados.
- Os Endereços de Encaminhamento são analisados para garantir unicidade (pois não queremos enviar duplicatas para um endereço ou gerar conexões SMTP adicionais desnecessárias).
- Para cada Endereço de Encaminhamento, consultamos seu nome de domínio em nosso endpoint de API
/v1/max-forwarded-addresses(para determinar quantos endereços o domínio está autorizado a encaminhar email por alias, por exemplo, 10 por padrão – veja a seção sobre limite máximo de encaminhamento por alias). Se esse limite for excedido, ocorrerá um erro 550 e o remetente receberá um bounce para esse destinatário. - Consultamos as configurações do destinatário original em nosso endpoint de API
/v1/settings, que suporta uma consulta para usuários pagos (com fallback para usuários gratuitos). Isso retorna um objeto de configuração para configurações avançadas deport(Número, por exemplo,25),has_adult_content_protection(Booleano),has_phishing_protection(Booleano),has_executable_protection(Booleano) ehas_virus_protection(Booleano). - Com base nessas configurações, verificamos os resultados do Scanner de Spam e, se ocorrerem erros, a mensagem é rejeitada com o código de erro 554 (por exemplo, se
has_virus_protectionestiver habilitado, verificaremos os resultados do Scanner de Spam para vírus). Note que todos os usuários do plano gratuito estarão optados para verificações contra conteúdo adulto, phishing, executáveis e vírus. Por padrão, todos os usuários do plano pago também estão optados, mas essa configuração pode ser alterada na página de Configurações para um domínio no painel do Forward Email).
- Consultamos os registros TXT do nome de domínio (a parte após o símbolo
-
Para cada Endereço de Encaminhamento processado do destinatário, realizamos as seguintes operações:
- O endereço é verificado contra nossa lista de negação, e se estiver listado, ocorrerá um código de erro 421 (indica ao remetente para tentar novamente mais tarde).
- Se o endereço for um webhook, definimos um Booleano para operações futuras (veja abaixo – agrupamos webhooks semelhantes para fazer uma única requisição POST em vez de múltiplas para entrega).
- Se o endereço for um endereço de email, analisamos o host para operações futuras (veja abaixo – agrupamos hosts semelhantes para fazer uma conexão única em vez de múltiplas conexões individuais para entrega).
-
Se não houver destinatários e não houver rejeições, então respondemos com um erro 550 de "Destinatários inválidos".
-
Se houver destinatários, então iteramos sobre eles (agrupados pelo mesmo host) e entregamos os e-mails. Veja a seção Como você lida com problemas de entrega de e-mail abaixo para mais detalhes.
- Se ocorrerem erros ao enviar os e-mails, então os armazenaremos na memória para processamento posterior.
- Usaremos o código de erro mais baixo (se houver) do envio dos e-mails – e usaremos esse código como resposta ao comando
DATA. Isso significa que e-mails não entregues normalmente serão reenviados pelo remetente original, enquanto e-mails que já foram entregues não serão reenviados na próxima vez que a mensagem for enviada (pois usamos Fingerprinting). - Se não ocorrerem erros, então enviaremos um código de status SMTP 250 de sucesso.
- Uma rejeição é determinada como qualquer tentativa de entrega que resulte em um código de status >= 500 (falhas permanentes).
-
Se não ocorreram rejeições (falhas permanentes), então retornaremos um código de status SMTP do menor código de erro de falhas não permanentes (ou um código 250 de sucesso se não houver nenhum).
-
Se ocorreram rejeições, então enviaremos e-mails de rejeição em segundo plano após retornar o menor de todos os códigos de erro para o remetente. No entanto, se o menor código de erro for >= 500, então não enviaremos nenhum e-mail de rejeição. Isso porque, se o fizéssemos, os remetentes receberiam um e-mail de rejeição duplo (por exemplo, um do seu MTA de saída, como Gmail – e também um nosso). Veja a seção sobre Como você protege contra backscatter abaixo para mais detalhes.
Como você lida com problemas de entrega de e-mail
Observe que faremos uma reescrita "Friendly-From" nos e-mails se e somente se a política DMARC do remetente não estiver passando E nenhuma assinatura DKIM estiver alinhada com o cabeçalho "From". Isso significa que alteraremos o cabeçalho "From" na mensagem, definiremos "X-Original-From" e também definiremos um "Reply-To" se ele ainda não estiver definido. Também re-selaremos o selo ARC na mensagem após alterar esses cabeçalhos.
Também usamos análise inteligente das mensagens de erro em todos os níveis da nossa pilha – em nosso código, requisições DNS, internos do Node.js, requisições HTTP (por exemplo, 408, 413 e 429 são mapeados para o código de resposta SMTP 421 se o destinatário for um webhook) e respostas do servidor de e-mail (por exemplo, respostas com "defer" ou "slowdown" seriam re-tentadas como erros 421).
Nossa lógica é à prova de falhas e também tentará novamente para erros SSL/TLS, problemas de conexão e mais. O objetivo da prova de falhas é maximizar a entregabilidade para todos os destinatários em uma configuração de encaminhamento.
Se o destinatário for um webhook, então permitiremos um tempo limite de 60 segundos para a requisição ser concluída com até 3 tentativas (totalizando 4 requisições antes de uma falha). Observe que analisamos corretamente os códigos de erro 408, 413 e 429 e os mapeamos para um código de resposta SMTP 421.
Caso contrário, se o destinatário for um endereço de e-mail, tentaremos enviar o e-mail com TLS oportunista (tentamos usar STARTTLS se estiver disponível no servidor de e-mail do destinatário). Se ocorrer um erro SSL/TLS ao tentar enviar o e-mail, tentaremos enviar o e-mail sem TLS (sem usar STARTTLS).
Se ocorrerem erros de DNS ou de conexão, retornaremos ao comando DATA um código de resposta SMTP 421, caso contrário, se houver erros de nível >= 500, serão enviadas rejeições.
Se detectarmos que um servidor de e-mail para o qual estamos tentando entregar bloqueou um ou mais dos nossos endereços IP de troca de e-mail (por exemplo, pela tecnologia que usam para adiar spammers), enviaremos um código de resposta SMTP 421 para que o remetente tente reenviar a mensagem mais tarde (e seremos alertados sobre o problema para que possamos tentar resolvê-lo antes da próxima tentativa).
Como você lida com seus endereços IP sendo bloqueados
Monitoramos rotineiramente todas as principais listas de negação DNS e, se algum dos nossos endereços IP de troca de correio ("MX") estiver listado em uma lista de negação importante, retiraremos ele do registro DNS A relevante de round robin, se possível, até que o problema seja resolvido.
No momento em que este texto foi escrito, também estamos listados em várias listas de permissão DNS, e levamos a sério o monitoramento das listas de negação. Se você notar algum problema antes que tenhamos a chance de resolvê-lo, por favor, nos notifique por escrito em support@forwardemail.net.
Nossos endereços IP são publicamente disponíveis, veja esta seção abaixo para mais informações.
O que são endereços postmaster
Para evitar devoluções mal direcionadas e o envio de mensagens de resposta automática para caixas de correio não monitoradas ou inexistentes, mantemos uma lista de nomes de usuário semelhantes a mailer-daemon:
automailerautoresponderbouncebounce-notificationbounce-notificationsbounceshostmasterlistservlocalhostmail-daemonmail.daemonmaildaemonmailer-daemonmailer.daemonmailerdaemonmajordomopostmaster- e qualquer endereço no-reply
Veja RFC 5320 Seção 4.6 para mais informações sobre como listas como essas são usadas para criar sistemas de email eficientes.
O que são endereços no-reply
Nomes de usuário de email iguais a qualquer um dos seguintes (insensível a maiúsculas/minúsculas) são considerados endereços no-reply:
do-not-replydo-not-responddo.not.replydonotreplydonotresponddont-replynaorespondano-repliesno-replyno-replysno.repliesno.replyno.replysno_replynobodynorepliesnoreplynoreplys
Esta lista é mantida como um projeto open-source no GitHub.
Quais são os endereços IP do seu servidor
Publicamos nossos endereços IP em https://forwardemail.net/ips.
Vocês têm uma lista de permissão
Sim, temos uma lista de extensões de nomes de domínio que são permitidas por padrão e uma lista de permissão dinâmica, em cache e rotativa baseada em critérios rigorosos.
Todos os domínios, emails e endereços IP usados por clientes pagantes são automaticamente verificados contra nossa lista de negação a cada hora – o que alerta os administradores que podem intervir manualmente se necessário.
Além disso, se um dos seus domínios ou seus endereços de email estiverem em lista de negação (por exemplo, por envio de spam, vírus ou devido a ataques de personificação) – então os administradores do domínio (você) e os administradores da nossa equipe serão notificados por email imediatamente. Recomendamos fortemente que você configure DMARC para evitar isso.
Quais extensões de nomes de domínio são permitidas por padrão
As seguintes extensões de nomes de domínio são consideradas permitidas por padrão (independentemente de estarem ou não na Umbrella Popularity List):
edugovmilintarpadni.usfed.usisa.uskids.usnsn.usak.usal.usar.usas.usaz.usca.usco.usct.usdc.usde.usfl.usga.usgu.ushi.usia.usid.usil.usin.usks.usky.usla.usma.usmd.usme.usmi.usmn.usmo.usms.usmt.usnc.usnd.usne.usnh.usnj.usnm.usnv.usny.usoh.usok.usor.uspa.uspr.usri.ussc.ussd.ustn.ustx.usut.usva.usvi.usvt.uswa.uswi.uswv.uswy.usmil.ttedu.ttedu.tredu.uaedu.auac.atedu.brac.nzschool.nzcri.nzhealth.nzmil.nzparliament.nzac.inedu.inmil.inac.jped.jplg.jpac.zaedu.zamil.zaschool.zamil.krac.krhs.krms.kres.krsc.krkg.kredu.esac.lksch.lkedu.lkac.thmi.thadmin.chcanada.cagc.cago.idgo.jpgo.kego.krgo.thgob.argob.clgob.esgob.mxgob.vegob.svgouv.frgouv.ncgouv.qc.cagov.adgov.afgov.aigov.algov.amgov.aogov.augov.awgov.axgov.azgov.bdgov.begov.bggov.bmgov.bygov.clgov.cngov.cogov.cygov.czgov.dzgov.eggov.figov.fkgov.gggov.grgov.hkgov.hrgov.hugov.iegov.ilgov.imgov.ingov.iqgov.irgov.itgov.jegov.kpgov.krdgov.kygov.kzgov.lbgov.lkgov.ltgov.lvgov.magov.mmgov.mogov.mtgov.mygov.nggov.npgov.phgov.pkgov.plgov.ptgov.pygov.rogov.rugov.scotgov.segov.sggov.sigov.skgov.trgov.ttgov.twgov.uagov.ukgov.vngov.walesgov.zagovernment.pngovt.nzgv.atac.ukbl.ukjudiciary.ukmod.uknhs.ukparliament.ukpolice.ukrct.ukroyal.uksch.ukukaea.uk
aaaaarpabarthabbabbottabbvieabcaccentureacoaegaetnaaflagakhanaigaigoairbusairtelakdnalfaromeoalibabaalipayallfinanzallstateallyalstomamazonamericanexpressamexamicaandroidanzaolappleaquarellearamcoaudiauspostawsaxaazurebaidubananarepublicbarclaycardbarclaysbasketballbauhausbbcbbtbbvabcgbentleybhartibingblancobloombergbmsbmwbnlbnpparibasboehringerbookingboschbostikbradescobridgestonebrotherbugatticalcalvinkleincanoncapitalonecaravancartiercbacbncbrecbscerncfachanelchasechintaichromechryslerciprianiciscocitadelciticiticclubmedcomcastcommbankcreditunioncrowncrscsccuisinelladaburdatsundealerdelldeloittedeltadhldiscoverdishdnpdodgedunlopdupontdvagedekaemerckepsonericssonerniesuranceetisalateurovisioneverbankextraspacefagefairwindsfarmersfedexferrariferrerofiatfidelityfirestonefirmdaleflickrflirflsmidthfordfoxfreseniusforexfrogansfrontierfujitsufujixeroxgallogallupgapgbizgeagentinggivinggleglobogmailgmogmxgodaddygoldpointgoodyeargooggooglegraingerguardianguccihbohdfchdfcbankhermeshisamitsuhitachihkthondahoneywellhotmailhsbchugheshyatthyundaiibmieeeifmikanoimdbinfinitiintelintuitipirangaiselectitauitvivecojaguarjavajcbjcpjeepjpmorganjuniperkddikerryhotelskerrylogisticskerrypropertieskfhkiakinderkindlekomatsukpmgkredkuokgrouplacaixaladbrokeslamborghinilancasterlancialancomelandroverlanxesslasallelatrobeldsleclerclegoliaisonlexuslidllifestylelillylincolnlindelipsylixillocuslottelpllplfinanciallundbecklupinmacysmaifmanmangomarriottmaseratimattelmckinseymetlifemicrosoftminimitmitsubishimlbmmamonashmormonmotomovistarmsdmtnmtrmutualnadexnationwidenaturanbanecnetflixneustarnewhollandnflnhkniconikenikonnissannissaynokianorthwesternmutualnortonnranttobiofficeomegaoracleorangeotsukapanasonicpccwpfizerphilipspiagetpictetpingpioneerplayplaystationpohlpolitiepraxiprodprogressivepruprudentialpwcqvcredstonereliancerexrothricohrmitrocherrogersrwesafetysakurasamsungsandviksandvikcoromantsanofisapsaxosbiscascbschaefflerschmidtschwarzscjohnsonscorseatsenersessewsevensfrseekshangrilasharpshawshellshriramsinaskyskypesmartsncfsoftbanksohusonyspiegelstadastaplesstarstarhubstatebankstatefarmstatoilstcstcgroupsuzukiswatchswiftcoversymantectaobaotargettatamotorstdktelecitytelefonicatemasektevatiffanytjxtoraytoshibatotaltoyotatravelchanneltravelerstuitvsubsunicomuolupsvanguardverisignvigvikingvirginvisavistavistaprintvivovolkswagenvolvowalmartwalterweatherchannelweberweirwilliamhillwindowswmewolterskluwerwoodsidewtcxboxxeroxxfinityyahooyamaxunyandexyodobashiyoutubezapposzarazippo
bzhgfgpmqncpfpmretfwfyt
A partir de 8 de julho de 2025, adicionamos estes países específicos da Europa:
axbgfogigrhrhultlumcmkmtroskva
Em outubro de 2025, também adicionamos cz (República Tcheca) devido à demanda.
Especificamente, não incluímos ru e ua devido à alta atividade de spam.
Qual é o seu critério para a lista de permissões
Temos uma lista estática de extensões de nomes de domínio permitidas por padrão – e também mantemos uma lista dinâmica, em cache, rolante, baseada nos seguintes critérios rigorosos:
- O domínio raiz do remetente deve ser de uma extensão de nome de domínio que corresponda à lista que oferecemos em nosso plano gratuito (com a adição de
bizeinfo). Também incluímos correspondências parciais deedu,govemil, comoxyz.gov.auexyz.edu.au. - O domínio raiz do remetente deve estar entre os 100.000 principais resultados únicos de domínios raiz analisados da Umbrella Popularity List ("UPL").
- O domínio raiz do remetente deve estar entre os 50.000 principais resultados de domínios raiz únicos que aparecem em pelo menos 4 dos últimos 7 dias da UPL (~50%+).
- O domínio raiz do remetente não deve ser classificado como conteúdo adulto ou malware pela Cloudflare.
- O domínio raiz do remetente deve ter registros A ou MX configurados.
- O domínio raiz do remetente deve ter registros A, registros MX, registro DMARC com
p=rejectoup=quarantine, ou um registro SPF com qualificador-allou~all.
Se este critério for satisfeito, o domínio raiz do remetente será armazenado em cache por 7 dias. Note que nosso trabalho automatizado é executado diariamente – portanto, esta é uma lista de permissões rolante em cache que é atualizada diariamente.
Nosso trabalho automatizado fará o download dos últimos 7 dias de UPLs na memória, descompactará e então analisará na memória de acordo com os critérios rigorosos acima.
Domínios populares na época desta redação, como Google, Yahoo, Microsoft, Amazon, Meta, Twitter, Netflix, Spotify e outros – estão, claro, incluídos. Se você for um remetente que não está em nossa lista de permissões, então na primeira vez que seu domínio raiz FQDN ou endereço IP enviar um e-mail, você será limitado por taxa e colocado na lista cinza. Note que esta é uma prática padrão adotada como um padrão de e-mail. A maioria dos clientes de servidores de e-mail tentará reenviar se receberem um erro de limite de taxa ou lista cinza (por exemplo, um código de status de erro 421 ou nível 4xx).
Observe que remetentes específicos como a@gmail.com, b@xyz.edu e c@gov.au ainda podem ser negados (por exemplo, se detectarmos automaticamente spam, phishing ou malware desses remetentes).
Quais extensões de nome de domínio podem ser usadas gratuitamente
A partir de 31 de março de 2023, aplicamos uma nova regra geral de spam para proteger nossos usuários e serviço.
Esta nova regra permite apenas as seguintes extensões de nome de domínio para serem usadas em nosso plano gratuito:
acadagaialamappasatauaxbabebgbrbybzhcacatcccdchckcocomdedevdjdkeeeseufamilyfifmfofrgfgggiglgpgrhrhuidieiliminioirisitjejpkekrlaliltlulvlymcmdmemkmnmqmsmtmumxncnetninlnonunzorgpfplpmprptpwrerorsscseshsisksmsrsttctftmtotvukusuzvavcvgvuwfwsxyzytza
Sim, usamos uma política de greylisting de email muito flexível. O greylisting só se aplica a remetentes que não estão na nossa allowlist e permanece em nosso cache por 30 dias.
Para qualquer remetente novo, armazenamos uma chave em nosso banco de dados Redis por 30 dias com um valor definido como o horário inicial de chegada da sua primeira solicitação. Em seguida, rejeitamos o email com um código de status de retry 450 e só permitimos a passagem após 5 minutos terem se passado.
Se eles esperarem com sucesso por 5 minutos a partir desse horário inicial de chegada, então seus emails serão aceitos e eles não receberão mais esse código de status 450.
A chave consiste no domínio raiz FQDN ou no endereço IP do remetente. Isso significa que qualquer subdomínio que passar pela greylist também passará para o domínio raiz, e vice-versa (é isso que queremos dizer com uma política "muito flexível").
Por exemplo, se um email vier de test.example.com antes de vermos um email vindo de example.com, então qualquer email de test.example.com e/ou example.com terá que esperar 5 minutos a partir do horário inicial de chegada da conexão. Não fazemos com que tanto test.example.com quanto example.com esperem seus próprios períodos de 5 minutos (nossa política de greylisting se aplica no nível do domínio raiz).
Note que o greylisting não se aplica a nenhum remetente em nossa allowlist (por exemplo, Meta, Amazon, Netflix, Google, Microsoft no momento desta escrita).
Você tem uma denylist
Sim, operamos nossa própria denylist e a atualizamos automaticamente em tempo real e manualmente com base em spam e atividade maliciosa detectada.
Também puxamos todos os endereços IP da denylist UCEPROTECT Nível 1 em http://wget-mirrors.uceprotect.net/rbldnsd-all/dnsbl-1.uceprotect.net.gz a cada hora e os inserimos em nossa denylist com expiração de 7 dias.
Remetentes encontrados na denylist receberão um código de erro 421 (indica ao remetente para tentar novamente mais tarde) se não estiverem na allowlist.
Ao usar um código de status 421 em vez de 554, potenciais falsos positivos podem ser aliviados em tempo real e a mensagem pode ser entregue com sucesso na próxima tentativa.
Isso é diferente de outros serviços de email, onde se você for colocado em uma blocklist, ocorre uma falha permanente e definitiva. Muitas vezes é difícil pedir para remetentes tentarem reenviar mensagens (especialmente de grandes organizações), e portanto essa abordagem dá cerca de 5 dias a partir da tentativa inicial de email para que o remetente, destinatário ou nós possamos intervir e resolver o problema (solicitando a remoção da denylist).
Todas as solicitações de remoção da denylist são monitoradas em tempo real por administradores (por exemplo, para que falsos positivos recorrentes possam ser permanentemente adicionados à allowlist pelos administradores).
Solicitações de remoção da denylist podem ser feitas em https://forwardemail.net/denylist. Usuários pagos têm suas solicitações de remoção processadas instantaneamente, enquanto usuários não pagos devem aguardar os administradores processarem sua solicitação.
Remetentes detectados enviando spam ou conteúdo de vírus serão adicionados à denylist da seguinte forma:
- A impressão digital inicial da mensagem é greylistada ao detectar spam ou blocklist de um remetente "confiável" (por exemplo,
gmail.com,microsoft.com,apple.com).- Se o remetente estava na allowlist, a mensagem é greylistada por 1 hora.
- Se o remetente não está na allowlist, a mensagem é greylistada por 6 horas.
- Extraímos chaves para a denylist a partir das informações do remetente e da mensagem, e para cada uma dessas chaves criamos (se ainda não existir) um contador, incrementamos em 1 e armazenamos em cache por 24 horas.
- Para remetentes na allowlist:
- Adicionamos uma chave para o endereço de email do envelope "MAIL FROM" se ele passou SPF ou não tiver SPF, e não for um nome de usuário postmaster ou um nome de usuário no-reply.
- Se o cabeçalho "From" estava na allowlist, então adicionamos uma chave para o endereço de email do cabeçalho "From" se ele passou SPF ou passou e alinhou DKIM.
- Se o cabeçalho "From" não estava na allowlist, então adicionamos uma chave para o endereço de email do cabeçalho "From" e seu domínio raiz analisado.
- Para remetentes não na allowlist:
- Adicionamos uma chave para o endereço de email do envelope "MAIL FROM" se ele passou SPF.
- Se o cabeçalho "From" estava na allowlist, então adicionamos uma chave para o endereço de email do cabeçalho "From" se ele passou SPF ou passou e alinhou DKIM.
- Se o cabeçalho "From" não estava na allowlist, então adicionamos uma chave para o endereço de email do cabeçalho "From" e seu domínio raiz analisado.
- Adicionamos uma chave para o endereço IP remoto do remetente.
- Adicionamos uma chave para o hostname resolvido do cliente por lookup reverso do endereço IP do remetente (se houver).
- Adicionamos uma chave para o domínio raiz do hostname resolvido do cliente (se houver, e se for diferente do hostname resolvido do cliente).
- Para remetentes na allowlist:
- Se o contador atingir 5 para um remetente e chave não na allowlist, então adicionamos a chave à denylist por 30 dias e um email é enviado para nossa equipe de abuso. Esses números podem mudar e atualizações serão refletidas aqui conforme monitoramos abusos.
- Se o contador atingir 10 para um remetente e chave na allowlist, então adicionamos a chave à denylist por 7 dias e um email é enviado para nossa equipe de abuso. Esses números podem mudar e atualizações serão refletidas aqui conforme monitoramos abusos.
NOTA: Em um futuro próximo, introduziremos monitoramento de reputação. O monitoramento de reputação calculará quando negar a lista de um remetente com base em um limite percentual (em vez de um contador rudimentar como mencionado acima).
Você tem limitação de taxa
A limitação de taxa do remetente é feita pelo domínio raiz extraído de uma pesquisa PTR reversa no endereço IP do remetente – ou, se isso não resultar em nada, então simplesmente usa o endereço IP do remetente. Note que nos referimos a isso como Sender abaixo.
Nossos servidores MX têm limites diários para o correio recebido para armazenamento IMAP criptografado:
- Em vez de limitar a taxa do correio recebido em uma base individual de alias (ex.:
you@yourdomain.com) – limitamos pela própria nome de domínio do alias (ex.:yourdomain.com). Isso impede queSendersinundem as caixas de entrada de todos os aliases em seu domínio de uma só vez. - Temos limites gerais que se aplicam a todos os
Sendersem nosso serviço independentemente do destinatário:Sendersque consideramos "confiáveis" como fonte de verdade (ex.:gmail.com,microsoft.com,apple.com) são limitados a enviar 100 GB por dia.Sendersque estão na lista de permissão são limitados a enviar 10 GB por dia.- Todos os outros
Senderssão limitados a enviar 1 GB e/ou 1000 mensagens por dia.
- Temos um limite específico por
Sendereyourdomain.comde 1 GB e/ou 1000 mensagens diárias.
Os servidores MX também limitam mensagens encaminhadas para um ou mais destinatários por meio de limitação de taxa – mas isso se aplica apenas a Senders que não estão na lista de permissão:
-
Permitimos até 100 conexões por hora, por domínio raiz FQDN resolvido do
Sender(ou) endereço IP remoto doSender(se não houver PTR reverso disponível), e por destinatário do envelope. Armazenamos a chave para limitação de taxa como um hash criptográfico em nosso banco de dados Redis. -
Se você estiver enviando e-mail através do nosso sistema, por favor, certifique-se de ter um PTR reverso configurado para todos os seus endereços IP (caso contrário, cada domínio raiz FQDN único ou endereço IP do qual você enviar será limitado na taxa).
-
Note que se você enviar através de um sistema popular como Amazon SES, então você não será limitado na taxa, pois (no momento desta escrita) o Amazon SES está listado em nossa lista de permissão.
-
Se você estiver enviando de um domínio como
test.abc.123.example.com, então o limite de taxa será imposto emexample.com. Muitos spammers usam centenas de subdomínios para contornar filtros comuns de spam que limitam taxa apenas por nomes de host únicos em vez de domínios raiz FQDN únicos. -
Sendersque excederem o limite de taxa serão rejeitados com um erro 421.
Nossos servidores IMAP e SMTP limitam seus aliases a não terem mais de 60 conexões simultâneas ao mesmo tempo.
Nossos servidores MX limitam Senders não na lista de permissão a estabelecerem mais de 10 conexões simultâneas (com expiração de cache de 3 minutos para o contador, que espelha nosso tempo limite de socket de 3 minutos).
Como você protege contra backscatter
Rebotes mal direcionados ou spam de rebote (conhecido como "Backscatter") podem causar reputação negativa para endereços IP do remetente.
Tomamos duas medidas para proteger contra backscatter, que são detalhadas nas seções seguintes Prevenir rebotes de spammers conhecidos do MAIL FROM e Prevenir rebotes desnecessários para proteger contra backscatter abaixo.
Prevenir rebotes de spammers conhecidos do MAIL FROM
Extraímos a lista de Backscatter.org (alimentado por UCEPROTECT) em http://wget-mirrors.uceprotect.net/rbldnsd-all/ips.backscatterer.org.gz a cada hora e a alimentamos em nosso banco de dados Redis (também comparamos a diferença antecipadamente; caso algum IP tenha sido removido e precise ser respeitado). Se o MAIL FROM estiver em branco OU for igual (case-insensitive) a qualquer um dos endereços postmaster (a parte antes do @ em um e-mail), então verificamos se o IP do remetente corresponde a algum desta lista.
Se o IP do remetente estiver listado (e não estiver em nossa lista de permissões), então enviamos um erro 554 com a mensagem The IP ${session.remoteAddress} is blocked by https://www.backscatterer.org/index.php?target=test&ip=${session.remoteAddress}. Seremos alertados se um remetente estiver tanto na lista Backscatterer quanto em nossa lista de permissões para que possamos resolver o problema, se necessário.
As técnicas descritas nesta seção aderem à recomendação "SAFE MODE" em https://www.backscatterer.org/?target=usage – onde só verificamos o IP do remetente se certas condições já foram atendidas.
Prevenir rejeições desnecessárias para proteger contra backscatter
Rejeições (bounces) são e-mails que indicam que o encaminhamento do e-mail falhou completamente para o destinatário e o e-mail não será reenviado.
Uma razão comum para ser listado na lista Backscatterer é rejeições mal direcionadas ou spam de rejeição, então devemos proteger contra isso de algumas maneiras:
-
Só enviamos quando ocorrem erros com código >= 500 (quando e-mails tentados a serem encaminhados falharam, por exemplo, o Gmail responde com um erro de nível 500).
-
Enviamos apenas uma vez e somente uma vez (usamos uma chave de impressão digital de rejeição calculada e armazenamos em cache para evitar envios duplicados). A impressão digital da rejeição é uma chave que é a impressão digital da mensagem combinada com um hash do endereço de rejeição e seu código de erro). Veja a seção sobre Impressão Digital para mais detalhes sobre como a impressão digital da mensagem é calculada. Impressões digitais de rejeições enviadas com sucesso expirarão após 7 dias em nosso cache Redis.
-
Só enviamos quando o MAIL FROM e/ou From não estiverem em branco e não contiverem (case-insensitive) um nome de usuário postmaster (a parte antes do @ em um e-mail).
-
Não enviamos se a mensagem original tiver algum dos seguintes cabeçalhos (case-insensitive):
- Cabeçalho
auto-submittedcom valor diferente deno. - Cabeçalho
x-auto-response-suppresscom valordr,autoreply,auto-reply,auto_replyouall - Cabeçalho
list-id,list-subscribe,list-unsubscribe,list-help,list-post,list-owner,list-archive,x-autoreply,x-autorespondoux-auto-respond(independente do valor). - Cabeçalho
precedencecom valorbulk,autoreply,auto-reply,auto_replyoulist.
- Cabeçalho
-
Não enviamos se o endereço de e-mail MAIL FROM ou From terminar com
+donotreply,-donotreply,+noreplyou-noreply. -
Não enviamos se a parte do nome de usuário do endereço de e-mail From for
mdaemone tiver um cabeçalho case-insensitiveX-MDDSN-Message. -
Não enviamos se houver um cabeçalho case-insensitive
content-typecom valormultipart/report.
Como você determina a impressão digital de um e-mail
A impressão digital de um e-mail é usada para determinar a unicidade de um e-mail e para evitar que mensagens duplicadas sejam entregues e rejeições duplicadas sejam enviadas.
A impressão digital é calculada a partir da seguinte lista:
- Nome de host FQDN resolvido pelo cliente ou endereço IP
- Valor do cabeçalho
Message-ID(se houver) - Valor do cabeçalho
Date(se houver) - Valor do cabeçalho
From(se houver) - Valor do cabeçalho
To(se houver) - Valor do cabeçalho
Cc(se houver) - Valor do cabeçalho
Subject(se houver) - Valor do
Body(se houver)
Posso encaminhar e-mails para portas diferentes da 25 (por exemplo, se meu ISP bloqueou a porta 25)
Sim, desde 5 de maio de 2020 adicionamos esse recurso. Atualmente o recurso é específico por domínio, e não por alias. Se você precisar que seja específico por alias, por favor entre em contato conosco para informar suas necessidades.
Por exemplo, se eu quiser que todos os e-mails que vão para example.com sejam encaminhados para a porta SMTP dos destinatários alias 1337 em vez de 25:
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email-port=1337 |
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=example.com |
Ele suporta o símbolo de mais + para aliases do Gmail
Sim, absolutamente.
Ele suporta subdomínios
Sim, absolutamente. Em vez de usar "@", ".", ou em branco como nome/host/alias, você simplesmente usa o nome do subdomínio como valor.
Se você quiser que foo.example.com encaminhe e-mails, então insira foo como valor do nome/host/alias nas suas configurações DNS (para ambos registros MX e TXT).
Isso encaminha os cabeçalhos dos meus e-mails
Sim, absolutamente.
Isso é bem testado
Sim, há testes escritos com ava e também possui cobertura de código.
Vocês repassam mensagens e códigos de resposta SMTP
Sim, absolutamente. Por exemplo, se você está enviando um e-mail para hello@example.com e ele está registrado para encaminhar para user@gmail.com, então a mensagem e o código de resposta SMTP do servidor SMTP "gmail.com" serão retornados em vez do servidor proxy em "mx1.forwardemail.net" ou "mx2.forwardemail.net".
Como vocês previnem spammers e garantem uma boa reputação de encaminhamento de e-mails
Veja nossas seções sobre Como funciona seu sistema de encaminhamento de e-mails, Como vocês lidam com problemas de entrega de e-mails, e Como vocês lidam com o bloqueio dos seus endereços IP acima.
Como vocês realizam consultas DNS em nomes de domínio
Criamos um projeto de software open-source 🍊 Tangerine e o usamos para consultas DNS. Os servidores DNS padrão usados são 1.1.1.1 e 1.0.0.1, e as consultas DNS são feitas através de DNS sobre HTTPS ("DoH") na camada de aplicação.
🍊 Tangerine usa o serviço DNS para consumidores focado em privacidade da CloudFlare por padrão.
Conta e Faturamento
Vocês oferecem garantia de reembolso nos planos pagos
Sim! Reembolsos automáticos ocorrem quando você faz upgrade, downgrade ou cancela sua conta dentro de 30 dias a partir do início do seu plano. Isso se aplica apenas para clientes pela primeira vez.
Se eu mudar de plano, vocês fazem prorrateio e reembolsam a diferença
Não fazemos prorrateio nem reembolsamos a diferença quando você muda de plano. Em vez disso, convertemos a duração restante a partir da data de expiração do seu plano atual para a duração relativa mais próxima do seu novo plano (arredondada para baixo por mês).
Observe que, se você fizer upgrade ou downgrade entre planos pagos dentro de uma janela de 30 dias desde o início do plano pago, reembolsaremos automaticamente o valor total do seu plano atual.
Posso usar este serviço de encaminhamento de e-mail apenas como um servidor MX "fallback" ou "fallover"
Não, não é recomendado, pois você só pode usar um servidor de troca de e-mails por vez. Fallbacks geralmente nunca são tentados novamente devido a configurações incorretas de prioridade e servidores de e-mail que não respeitam a verificação de prioridade MX.
Posso desativar aliases específicos
Sim, basta editar seu registro DNS TXT e prefixar o alias com um, dois ou três pontos de exclamação (veja abaixo).
Observe que você deve preservar o mapeamento ":" pois isso é necessário caso decida desativar isso no futuro (e também é usado para importação se você fizer upgrade para um de nossos planos pagos).
Para rejeição silenciosa (aparece para o remetente como se a mensagem tivesse sido enviada com sucesso, mas na verdade não vai para lugar algum) (código de status 250): Se você prefixar um alias com "!" (um ponto de exclamação) ele retornará um código de status 250 bem-sucedido para remetentes tentando enviar para esse endereço, mas os e-mails em si não irão para lugar algum (ex.: um buraco negro ou /dev/null).
Para rejeição suave (código de status 421): Se você prefixar um alias com "!!" (dois pontos de exclamação) ele retornará um código de erro temporário 421 para remetentes tentando enviar para esse endereço, e os e-mails geralmente serão tentados novamente por até 5 dias antes de serem rejeitados e devolvidos.
Para rejeição definitiva (código de status 550): Se você prefixar um alias com "!!!" (três pontos de exclamação) ele retornará um código de erro permanente 550 para remetentes tentando enviar para esse endereço e os e-mails serão rejeitados e devolvidos.
Por exemplo, se eu quiser que todos os e-mails que vão para alias@example.com parem de ser encaminhados para user@gmail.com e sejam rejeitados e devolvidos (ex.: usar três pontos de exclamação):
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=!!!alias:user@gmail.com |
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=!!!alias:nobody@forwardemail.net |
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=!!!alias |
Posso encaminhar e-mails para múltiplos destinatários
Sim, absolutamente. Basta especificar múltiplos destinatários nos seus registros TXT.
Por exemplo, se eu quiser que um e-mail enviado para hello@example.com seja encaminhado para user+a@gmail.com e user+b@gmail.com, então meu registro TXT ficaria assim:
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=hello:user+a@gmail.com,hello:user+b@gmail.com |
Ou, você pode especificá-los em duas linhas separadas, como esta:
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=hello:user+a@gmail.com |
| "@", ".", ou em branco | 3600 | TXT | forward-email=hello:user+b@gmail.com |
Fica a seu critério!
Posso ter múltiplos destinatários globais catch-all
Sim, você pode. Basta especificar múltiplos destinatários globais catch-all nos seus registros TXT.
Por exemplo, se eu quiser que todo e-mail enviado para *@example.com (o asterisco significa que é um curinga, ou seja, catch-all) seja encaminhado para user+a@gmail.com e user+b@gmail.com, então meu registro TXT ficaria assim:
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=user+a@gmail.com,user+b@gmail.com |
Ou, você pode especificá-los em duas linhas separadas, como esta:
| Nome/Host/Alias | TTL | Tipo | Resposta/Valor |
|---|---|---|---|
| "@", ".", ou em branco | 3600 | TXT | forward-email=user+a@gmail.com |
| @, ".", ou em branco | 3600 | TXT | forward-email=user+b@gmail.com |
Existe um limite máximo para o número de endereços de email para os quais posso encaminhar por alias
Sim, o limite padrão é 10. Isso NÃO significa que você pode ter apenas 10 aliases no seu nome de domínio. Você pode ter quantos aliases quiser (uma quantidade ilimitada). Significa que você só pode encaminhar um alias para 10 endereços de email únicos. Você poderia ter hello:user+1@gmail.com, hello:user+2@gmail.com, hello:user+3@gmail.com, … (de 1 a 10) – e qualquer email para hello@example.com seria encaminhado para user+1@gmail.com, user+2@gmail.com, user+3@gmail.com, … (de 1 a 10).
Posso encaminhar emails recursivamente
Sim, você pode, porém ainda deve respeitar o limite máximo. Se você tem hello:linus@example.com e linus:user@gmail.com, então emails para hello@example.com seriam encaminhados para linus@example.com e user@gmail.com. Note que um erro será gerado se você tentar encaminhar emails recursivamente além do limite máximo.
As pessoas podem cancelar ou registrar meu encaminhamento de email sem minha permissão
Usamos verificação de registros MX e TXT, portanto, se você adicionar os respectivos registros MX e TXT deste serviço, então você está registrado. Se você removê-los, então você está cancelado. Você tem a propriedade do seu domínio e gerenciamento de DNS, então se alguém tem acesso a isso, então isso é um problema.
Como é gratuito
Forward Email oferece um nível gratuito por meio de uma combinação de desenvolvimento open-source, infraestrutura eficiente e planos pagos opcionais que suportam o serviço.
Nosso nível gratuito é suportado por:
-
Desenvolvimento Open Source: Nossa base de código é open source, permitindo contribuições da comunidade e operação transparente.
-
Infraestrutura Eficiente: Otimizamos nossos sistemas para lidar com encaminhamento de email com recursos mínimos.
-
Planos Premium Pagos: Usuários que precisam de recursos adicionais como envio SMTP, recebimento IMAP ou opções avançadas de privacidade assinam nossos planos pagos.
-
Limites de Uso Razoáveis: O nível gratuito possui políticas de uso justo para evitar abusos.
Note
Estamos comprometidos em manter o encaminhamento básico de email gratuito enquanto oferecemos recursos premium para usuários com necessidades mais avançadas.
Tip
Se você achar nosso serviço valioso, considere fazer upgrade para um plano pago para apoiar o desenvolvimento e manutenção contínuos.
Qual é o limite máximo de tamanho de email
O limite padrão é de 50MB, que inclui conteúdo, cabeçalhos e anexos. Note que serviços como Gmail e Outlook permitem apenas limite de 25MB, e se você ultrapassar o limite ao enviar para endereços nesses provedores, receberá uma mensagem de erro.
Um erro com o código de resposta apropriado é retornado se o limite de tamanho do arquivo for excedido.
Vocês armazenam logs de emails
Não, não escrevemos no disco nem armazenamos logs – com a exceção de erros e SMTP de saída (veja nossa Política de Privacidade).
Tudo é feito em memória e nosso código-fonte está no GitHub.
Vocês armazenam logs de erros
Sim. Você pode acessar os logs de erros em Minha Conta → Logs ou Minha Conta → Domínios.
Desde fevereiro de 2023, armazenamos logs de erros para códigos de resposta SMTP 4xx e 5xx por um período de 7 dias – que contêm o erro SMTP, envelope e cabeçalhos do email (nós não armazenamos o corpo do email nem anexos).
Os logs de erro permitem que você verifique e-mails importantes ausentes e mitigue falsos positivos de spam para seus domínios. Eles também são um ótimo recurso para depurar problemas com webhooks de e-mail (já que os logs de erro contêm a resposta do endpoint do webhook).
Os logs de erro para limitação de taxa e greylisting não são acessíveis, pois a conexão termina cedo (por exemplo, antes que os comandos RCPT TO e MAIL FROM possam ser transmitidos).
Veja nossa Política de Privacidade para mais informações.
Você lê meus e-mails
Não, absolutamente não. Veja nossa Política de Privacidade.
Muitos outros serviços de encaminhamento de e-mail armazenam e podem potencialmente ler seu e-mail. Não há razão para que e-mails encaminhados precisem ser armazenados em disco – e por isso arquitetamos a primeira solução open-source que faz tudo na memória.
Acreditamos que você deve ter direito à privacidade e a respeitamos estritamente. O código que é implantado no servidor é software open-source no GitHub para transparência e para construir confiança.
Posso "enviar e-mail como" no Gmail com isso
Sim! A partir de 2 de outubro de 2018 adicionamos esse recurso. Veja Como Enviar E-mail Como usando o Gmail acima!
Você também deve configurar o registro SPF para o Gmail na sua configuração DNS no registro TXT.
include:_spf.google.com ao seu registro SPF TXT, por exemplo:
v=spf1 a include:spf.forwardemail.net include:_spf.google.com -all
Posso "enviar e-mail como" no Outlook com isso
Sim! A partir de 2 de outubro de 2018 adicionamos esse recurso. Basta consultar estes dois links da Microsoft abaixo:
- https://support.office.com/en-us/article/add-or-remove-an-email-alias-in-outlook-com-459b1989-356d-40fa-a689-8f285b13f1f2
- https://support.office.com/en-us/article/send-email-from-a-different-address-in-outlook-com-ccba89cb-141c-4a36-8c56-6d16a8556d2e
Você também deve configurar o registro SPF para o Outlook na sua configuração DNS no registro TXT.
include:spf.protection.outlook.com ao seu registro SPF TXT, por exemplo:
v=spf1 a include:spf.forwardemail.net include:spf.protection.outlook.com -all
Posso "enviar e-mail como" no Apple Mail e iCloud Mail com isso
Se você é assinante do iCloud+, pode usar um domínio personalizado. Nosso serviço também é compatível com Apple Mail.
Por favor, consulte https://support.apple.com/en-us/102540 para mais informações.
Posso encaminhar e-mails ilimitados com isso
Sim, entretanto remetentes "relativamente desconhecidos" são limitados a 100 conexões por hora por hostname ou IP. Veja a seção sobre Limitação de Taxa e Greylisting acima.
Por "relativamente desconhecidos", queremos dizer remetentes que não aparecem na lista de permissões.
Se esse limite for excedido, enviamos um código de resposta 421 que informa ao servidor de e-mail do remetente para tentar novamente mais tarde.
Vocês oferecem domínios ilimitados por um preço único
Sim. Independentemente do plano que você esteja, você pagará apenas uma taxa mensal – que cobre todos os seus domínios.
Quais métodos de pagamento vocês aceitam
Forward Email aceita os seguintes métodos de pagamento únicos ou mensais/trimestrais/anuais:
- Cartões de Crédito/Débito/Transferências Bancárias: Visa, Mastercard, American Express, Discover, JCB, Diners Club, etc.
- PayPal: Conecte sua conta PayPal para pagamentos fáceis
- Criptomoeda: Aceitamos pagamentos via pagamentos em stablecoin da Stripe nas redes Ethereum, Polygon e Solana
Note
Armazenamos informações limitadas de pagamento em nossos servidores, que incluem apenas identificadores de pagamento e referências às transações, clientes, assinaturas e IDs de pagamento do Stripe e PayPal.
Tip
Para máxima privacidade, considere usar pagamentos em criptomoeda.
Todos os pagamentos são processados com segurança através do Stripe ou PayPal. Seus dados de pagamento nunca são armazenados em nossos servidores.
Recursos Adicionais
Tip
Nossos artigos abaixo são atualizados regularmente com novos guias, dicas e informações técnicas. Volte sempre para conferir o conteúdo mais recente.